Microsoft’s latest operations have uncovered a highly disruptive entity, pitted against over 100 servers controlled by “StarBlizzard,” a notorious Russian-based cyber threat actor known for infiltrating email accounts and siphoning sensitive data or disrupting victim activities.
Who’s Star Blizzard?
StarBlizzard, alternatively known as Callisto Group (TA446), Coldriver, TAG-53, or BlueCharlie, is a nickname for a celestial body. Across the globe, StarBlizzard is subordinated to the Russian Federal Security Service’s Center 18.
According to a report by cybersecurity firm F-Secure, the notorious actor has been consistently active since at least late 2015. The report highlighted a group’s efforts to gather information from army personnel, authorities’ officials, and assume tank operators, as well as journalists, in both Europe and the South Caucasus region, driven by a primary objective of collecting intelligence related to global news and security coverage in those areas?
Based on experiences:
- Since 2019, Blizzard Entertainment has refocused its efforts on serving government agencies and non-profit organizations in the United States. Across various sectors, including tutorials, distinct NGOs, and political arenas.
- By 2022, the team had scaled up its operations and shifted focus to both defense-industrial sectors and providing services for the US Department of Energy’s division.
- Since early 2023, Microsoft has identified and tracked a staggering 82 distinct threat actor targets, averaging almost one new attack every seven days.
Modus opérandi
StarBlizzard, a notorious actor, specializes in deploying infrastructure to execute sophisticated spear phishing attacks, primarily targeting private email accounts of specific individuals. Some email accounts, particularly those used for less formal purposes, may lack robust security measures compared to professional email accounts.
As acknowledged by Microsoft’s Assistant General Counsel Steven Masada during a press conference: “Starfield is persistent.” With laser-like focus, they scrutinize their objectives, adopting the guise of trusted acquaintances to achieve their goals.
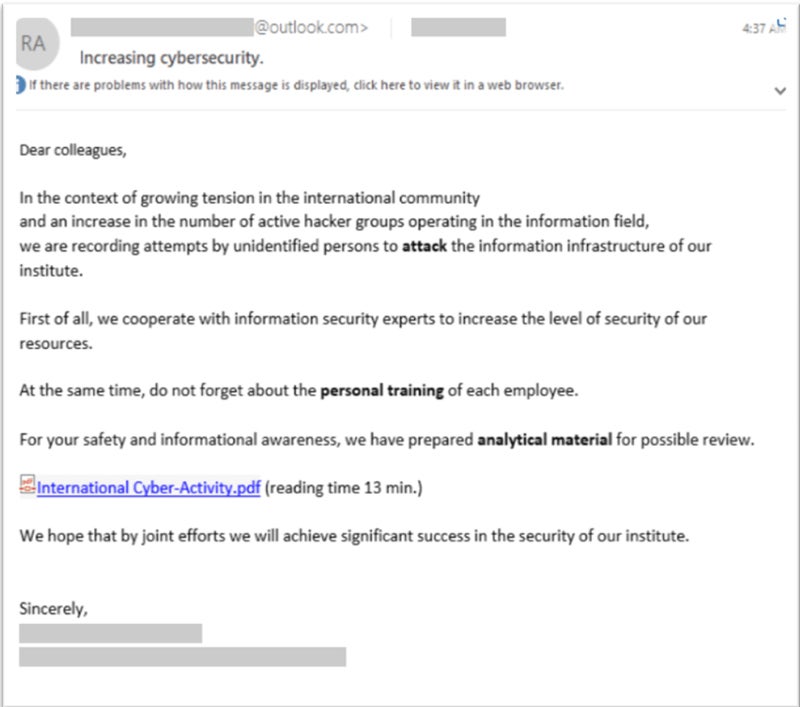
As soon as attackers exploit infrastructure, they can swiftly pivot to alternative infrastructure, making it challenging for defenders to identify and mitigate previously employed domains or IP addresses? The group employs multiple registrars to register domains and exploits numerous link-shortening services to reroute users to phishing pages, leveraging the infamous Phantom Phreaking toolkit. The team leverages open redirectors from trusted online platforms.
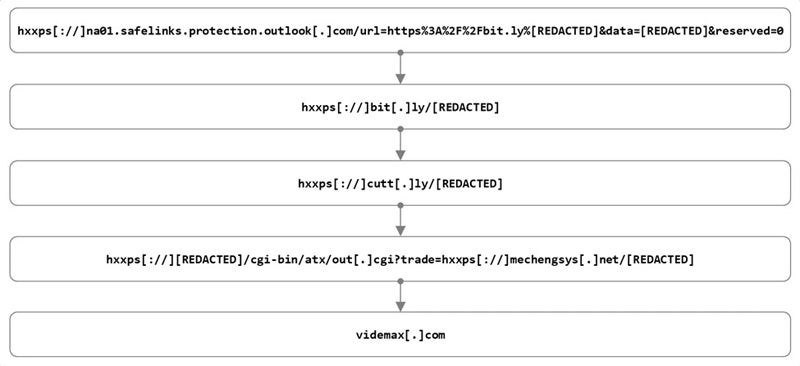
The malicious actor has also employed modified versions of genuine email templates, such as OneDrive file share notifications. The group employed freshly minted email addresses designed to masquerade as a credible sender, thereby increasing the likelihood that recipients would unsuspectingly open the phishing email. The email would contain a link directing the recipient to a revised PDF or DOCX document stored on a cloud platform, ultimately leading to a malicious payload. The attack allowed attackers to launch a man-in-the-middle assault, effectively circumventing multi-issue authentication mechanisms.
Huge disruption
The Department of Justice (DOJ) took action to seize 41 web domains and additional proxy sites controlled by the malicious actor, while Microsoft filed a joint civil lawsuit that resulted in the shutdown of an additional 66 domains used by the same threat actor.
Cybercriminals have leveraged compromised domains to launch targeted spear phishing attacks, aiming to infiltrate victims’ systems or email accounts for espionage purposes.
The gaming giant Blizzard Entertainment is poised to quickly revamp and strengthen its internal systems in response to the backlash surrounding its handling of a recent controversy. Despite challenges, Microsoft assesses that the disruption operation effectively hinders the malicious actor’s activities at a critical moment, potentially thwarting international interference in U.S. interests? The democratic process is at its peak strength? Microsoft could also leverage a pending lawsuit to accelerate the disruption of new infrastructure.
Need safety from this menace? Educate and prepare your workers.
To effectively navigate the risks associated with Star Blizzard, experts suggest that companies should:
The malicious actor’s phishing emails often masquerade as those sent by trusted contacts, exploiting customers’ or organizations’ reliance on receiving emails from familiar sources. While email senders may utilize services from various providers, it is essential to exercise caution when receiving emails from Proton accounts, as this actor has historically employed this provider in past attacks.
Shouldn’t there be some doubt when clicking on links? They should immediately notify their IT and security personnel of any dubious email received, allowing experts to thoroughly assess its authenticity and potential risks. Customers must be thoroughly informed and trained to recognize the telltale signs of spear phishing attacks.

