As online marketplaces gain popularity, they have also become a haven for scammers targeting both buyers and sellers who seek to exploit credit card information rather than secure a bargain? Researchers at ESET have identified an organized scammer group that has leveraged the Telekopye toolkit, first discovered by ESET analysts in 2023, to target customers of fashionably themed booking platforms.
In the final 12 months, we published a comprehensive two-part blog post series on Telekopye, a Telegram-based toolset that cybercriminals exploit to defraud unsuspecting individuals on online marketplaces. While investigators focused on Telekopye’s primary choices, others delved into the inner mechanisms of linked fraudulent organizations. On this blog post, we take stock of what’s changed in Telekopye operations since our last publication, drawing insights from our ongoing monitoring efforts. Scammers’ tactics evolve as they shift focus from traditional platforms to Reservation.com and Airbnb, refining operational efficiency to amplify financial gains through various means. Finally, but not least, our comprehensive guidance provides valuable insights on how to stay protected from these scams.
We presented our most recent research findings on Telekopye on October 2?nd
, 2024. You’ll have the opportunity to delve into all the details in our forthcoming white paper. The research was publicly disclosed on the Virus Bulletin platform.
- ESET analysis reveals the latest insights into Telekopye, a notorious toolkit that empowers cybercriminals to orchestrate fraudulent schemes and deceive online marketplace users.
- While our initial research delved into the Telekopye scam’s historical context, this latest investigation reveals the cunning tactics employed by scammers to amplify their financial gains, including expanding their victim base, capitalizing on seasonal trends, and refining their tools and methodologies.
- Telekopye teams have increasingly focused on popular accommodation booking platforms like Booking.com and Airbnb.
- The proliferation of fake vacation listings, often masquerading as genuine offerings from reputable hotels and accommodation providers, has become an increasingly prevalent issue.
- Scams targeting tourists had reached alarming levels during the summer vacation season in specific regions, exceeding those detected by ESET’s telemetry in Telekopye markets.
Telekopye overview
A cutting-edge platform dubbed Telekopye has emerged as a sophisticated Telegram bot, essentially transforming online market fraud into a coordinated criminal operation with unparalleled ease and versatility. Utilized by numerous fraudulent groups, comprising dozens of operatives, to pilfer tens of thousands of dollars from unsuspecting “Mammoths”, a term coined to describe targeted buyers and sellers.
Without needing advanced technical knowledge, Neanderthals can seamlessly utilize Telekopye’s comprehensive suite of tools within mere seconds.
Discovered by ESET analysis in 2023, the Telekopye malware has been operational since at least 2016, compromising victims globally. While some leads appear to be related to Russia due to the nation of origin for both the bot’s creator(s) and the scammers employing it, Telekopye targets numerous online marketplaces in Europe and North America, similar to prominent platforms like OLX, Vinted, eBay, and Wallapop. As of this writing, we’ve identified approximately 90 distinct companies that are being targeted by these scams.
Members of any Telegram group utilising the Telekopye platform gain seamless access to the bot’s user interface, allowing for effortless creation of phishing emails, SMS messages, webpages, and other functionalities.
Telekopye teams operate with a professional structure, featuring a clear chain of command, defined positions, established protocols, as well as rigorous onboarding and mentorship programs for new team members, standardized work schedules, and performance-based compensation for directors. The staff responsible for executing fraudulent schemes are tasked with flipping sensitive information obtained through illicit means, leaving financial transactions to other designated roles within the organization. Each group maintains a comprehensive record of all transactions, accessible to all members.
Neanderthals capitalize on two primary scenarios in online marketplaces: first, they operate as sellers; secondly, and more commonly, they engage as consumers. As users navigate through various online platforms and transactions, they unknowingly stumble upon cleverly crafted phishing nets that masquerade as authentic payment gateways, culminating in the unsuspecting victim’s entry of sensitive information such as credit card data or online banking credentials into these deceptively designed websites?
Recently, Telekopye teams have shifted their attention to developing tools that aid scammers in targeting unsuspecting customers of online booking platforms, which we’ll discuss further in the next section.
What’s driving the surge in demand for online hotel booking platforms?
By 2024, scammers operating under the guise of Telekopye had refined their tactics, targeting unsuspecting consumers of popular online booking services such as Booking.com and Airbnb. They have further refined their patient selection and focus strategies.
Concentrating on with a twist
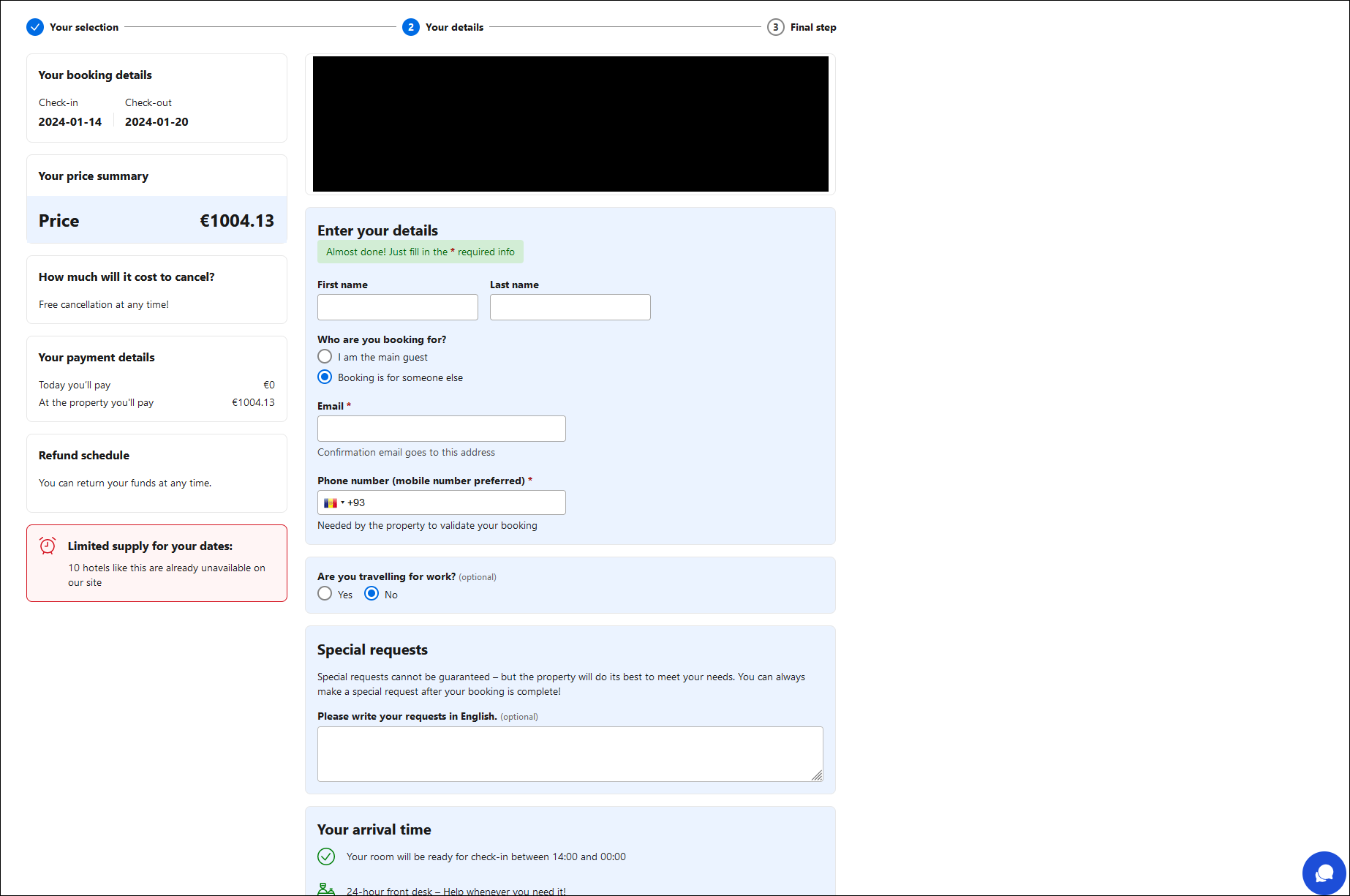
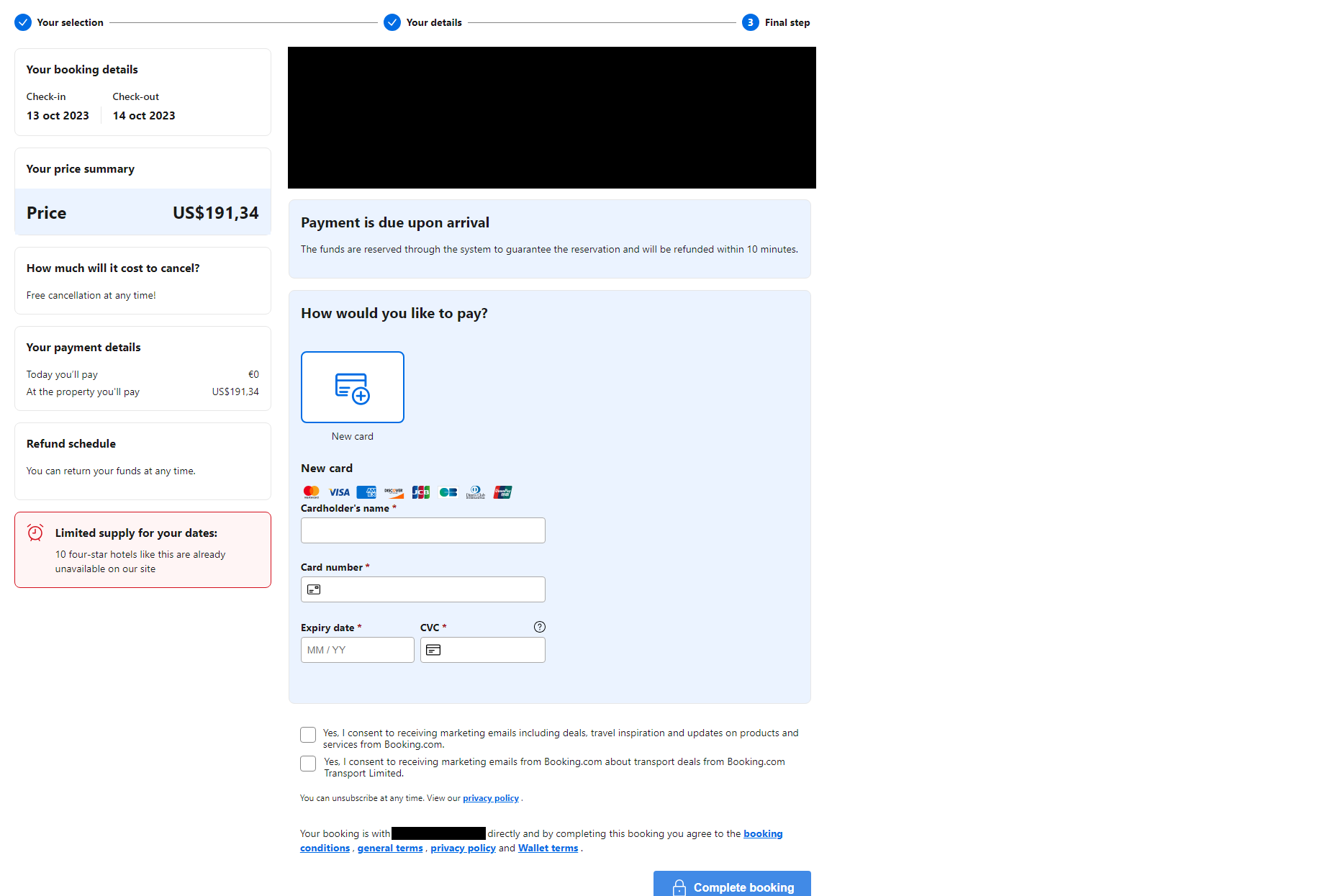
As the latest scam unfolds, a supposed representative from one of these online platforms reaches out to an unsuspecting individual, citing a supposedly critical issue with their booking fee. The message contains a link that directs users to a counterfeit webpage masquerading as the genuine social media platform.
The webpage conveniently pre-populates essential reservation information, including check-in and checkout dates, price, and location. The fabricated content on these deceitful websites eerily aligns with the specific concerns of targeted individuals.
Hackers gain access to luxury accommodations by exploiting vulnerabilities in booking platforms, often using stolen login credentials purchased from illegal marketplaces. Scammers exploit recent bookings that remain unpaid or were settled only briefly, initiating unsolicited chats via the booking platform’s messaging system to target unsuspecting customers. Upon configuration of the platform and Mammoth settings, a notification is automatically triggered, prompting the Mammoth to receive either an email or SMS from the booking system.
The rip-off becomes significantly more challenging to detect, as the targeted information is tailored to the victims’ personal experiences, delivered through an expected communication pathway, and linked websites that mimic genuine online platforms. While the presence of mismatched URLs might initially suggest an issue, it’s the sole indicator of something being awry in terms of impersonated, genuine websites. Neanderthals may utilize unique email addresses for initial contact, potentially rendering malicious emails more easily identifiable.
As soon as the user completes the fraudulent form on the phishing webpage, they’re redirected to the final stage of the “booking” process – a page requesting sensitive financial information. Scammers exploiting online platforms, card details entered fraudulently, allowing them to pilfer funds from unsuspecting victims’ accounts?
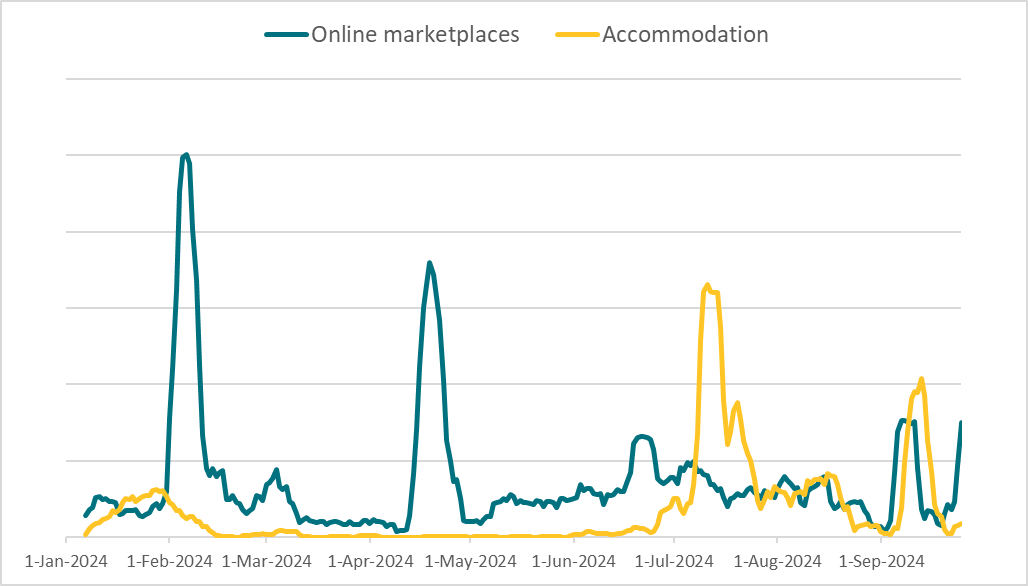
As evident from ESET telemetry data, this malicious campaign started to gain momentum in 2024. According to data, July saw a notable surge in accommodation-themed scams, outpacing Telekopye market scams for the first time, with a staggering more than double the number of detections recorded during that month. By late August and into September, the detection ranges for both classes had converged.
As summer’s vacation season arrives in prime destinations, the optimal window for booking stays is now open – but only time will tell if this trend will persist? By 2024, available intelligence suggests that emerging scams have accumulated nearly 50% of the detection metrics associated with Marketplace variations. Notably, the latest scams focus on just two platforms, a stark contrast to the numerous online marketplaces targeted by Telekopye.
Superior Telekopye options
Neanderthals enhanced their financial performance by expanding their investment portfolios, while also refining their tools and techniques to maximize gains.
Throughout our surveillance of Telekopye, we’ve observed that distinct Telegram groups develop their unique, high-level features within the toolkit, tailored to accelerate the fraudulent process, facilitate communication with victims, safeguard phishing websites against adversary interference, and other strategic goals.
Automated phishing web page era
In a bid to accelerate the process of producing counterfeit goods to deceive buyers on online marketplaces, ancient humans utilized makeshift tools like net scrapers to create fake products for sale on trendy digital platforms. To streamline the process, providing the sole URL to the product suffices, eliminating the need for a questionnaire regarding the specific Mammoth and product in question. TeleKopye automatically parses online web pages to extract essential data, significantly accelerating the process for fraudsters.
Interactive chatbot with on-the-fly translation
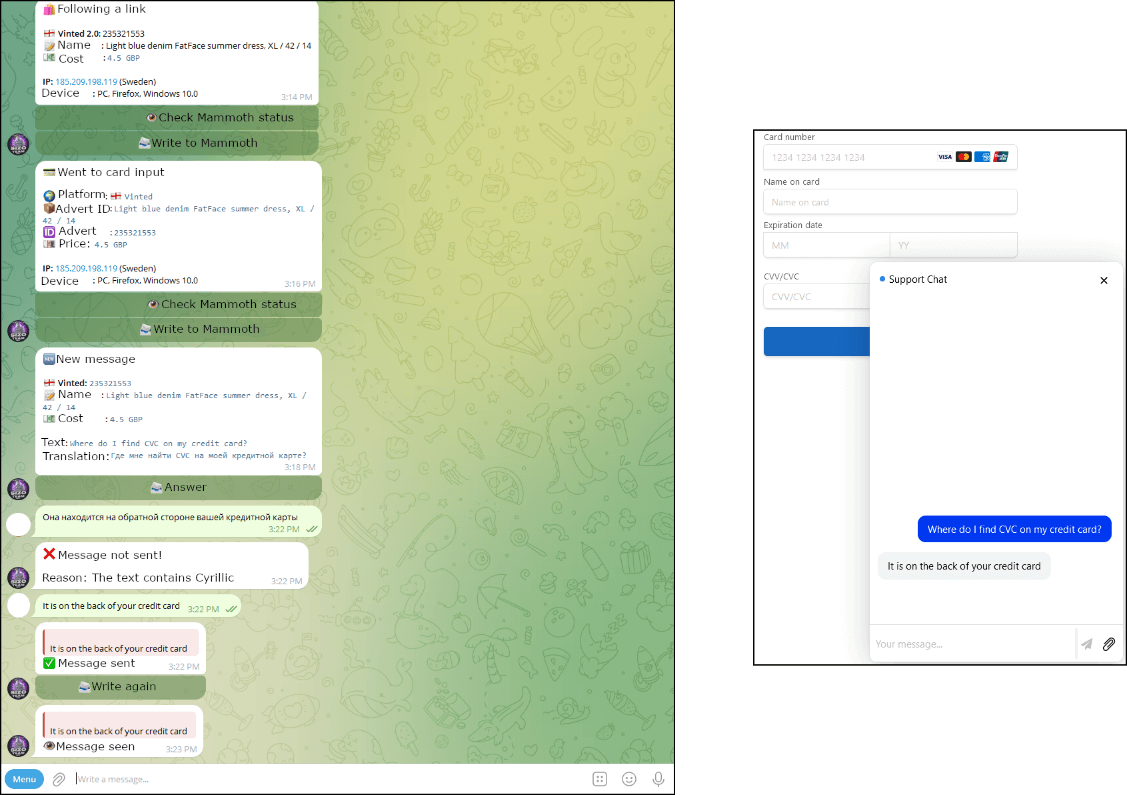
Neanderthals maintained a substantial repertoire of preconceived answers addressing common inquiries posed by Mammoths. Translated into multiple languages and stored within internal documentation, these texts have undergone refinement over the years to ensure precise and accurate renditions.
Neanderthals occasionally employed preconceived phrasing to prompt the mammoth towards a deceitful website featuring an embedded conversational AI in its lower right corner. Whenever the Mammoth initiates a conversation within this chat, its input is automatically transmitted to the Neanderthal’s designated Telegram group, where advanced algorithms seamlessly translate and disseminate the message. Automated translation of Neanderthals’ messages is not feasible – Neanderthals relied on manual communication methods, frequently employing primitive written systems. Examine three exhibits that illustrate this interplay from the perspectives of both Neanderthals and mammoths.
Anti-DDoS measures
While a significant portion of phishing websites leverages Cloudflare’s security features, particularly against bots and automated scans, relying on this service does not necessarily guarantee their legitimacy. A few Telekopye phishing websites also feature integrated DDoS protection. By leveraging our covertly acquired intelligence from within Neanderthal society, this specific behavioral trait aims to protect against potential threats or attacks from rival groups. These types of attacks often serve as a means to momentarily disrupt a rival’s operations.
Regulation enforcement operations
In late 2023, following ESET’s analysis of the Telekopye malware, authorities from the Czech Republic and Ukraine collaborated on a two-part operation to apprehend scores of cybercriminals, alongside notable gaming platform users. Operations were deliberately targeted against a multitude of unknown Telekopye teams, which had amassed at least €5 million (approximately US$5.5 million) since 2021, according to police estimates.
The successful disruption of criminal activity also shed light on the groups’ inner mechanics, particularly their methods for recruiting and utilizing members. Teams queried were led by middle-aged men from Japanese Europe, Western Asia, and Central Asia, operating from dedicated workspaces. Recruiting individuals from challenging backgrounds, the company posted job openings touting “easy money” and targeted technically skilled international students at universities with similar opportunities.
Several individuals implicated in this scheme also admitted to involvement with a similar fraudulent organization, dubbed Telekopye, which exploited identity verification services. The authorities uncovered a disturbing practice, where new recruits were deprived of their passports and personal identification documents, rendering it extremely difficult for them to disengage from the operation. Managers often resorted to intimidation tactics, issuing veiled threats against workers and their loved ones in an attempt to maintain control. This drastic reorientation transforms these processes into an entirely distinct ambiance.
Suggestions
To avoid falling victim to Telekopye’s scams, it’s essential to be aware of the tactics employed by scammers and exercise caution when using compromised platforms. To effectively safeguard against potential threats, it is essential to identify and focus on red flags. Additionally, installing a reliable anti-malware solution on your device can provide an extra layer of protection if you accidentally stumble upon a phishing website.
On-line market scams
- To verify the authenticity of an individual, it’s crucial to confirm their profile details, specifically their history on the platform, account age, ranking, and position. A significant red flag can be a location that’s too distant from their claimed identity or a recent account with no verifiable past; similarly, a negative ranking may also indicate scammer activity.
- As machine translation advances, scammers’ messages may no longer trigger red flags through grammatical inconsistencies. Rather than focusing solely on linguistic nuances, it’s crucial to prioritize the dialogue itself – excessive assertiveness can lead to unwanted complications.
- Maintain open lines of communication, regardless of whether the person you’re interacting with agrees or disagrees with your approach. The persistence of their reluctance to stay on the platform warrants utmost concern.
- When acting as a buyer, utilize secure interfaces within the platform throughout the entirety of the purchasing process whenever possible. We strongly advocate for direct exchange of goods or services, accompanied by the option to settle accounts in person or through a reliable supplier’s arrangement, which enables payment upon receipt.
- When operating as a vendor, ensure that you consistently leverage secure interfaces within the platform throughout the entirety of the promotional process each and every time it is available. In all instances, exercise autonomy in handling supply options and refrain from adhering to those specified by the client.
- When navigating links sent by someone you’re conversing with, thoroughly inspect the URL, website content, and certification credentials before engaging with the site.
Lodging reserving scams
- Before completing any forms related to your booking, always confirm that you are still within the official website or mobile application of the service provider in question, to guarantee a secure and legitimate transaction. Being directed to an external URL to proceed with your reservations and costs is often an indication of a potential scam.
- Due to the prevalence of fraudulent activity involving the exploitation of compromised lodging supplier accounts, it is crucially important that alternative verification methods be employed in place of immediate contact with suppliers to authenticate the authenticity of cost requests. In cases of uncertainty, reach out to the official buyer assistance team on the platform or report any suspicious activity.
- To safeguard your account from potential compromise, regardless of whether you’re booking accommodations or listing them for rent, utilize a robust password and enable two-factor authentication whenever possible.
Conclusion
Our investigation into Telekopye’s tactics has yielded valuable insights into these scams: by analyzing the technical underpinnings, business models, and human factors driving these operations, we’ve gained a nuanced understanding of this phenomenon.
Our analysis reveals that teams have exhaustively pursued strategies to optimize financial performance, including expanding patient populations, capitalizing on seasonal opportunities, and refining tools and processes. Notably, our research has revealed that Neanderthals are employing a new approach to booking lodging through specialized platforms, accompanied by a refined level of focus.
During our investigation, it’s worth highlighting that we’ve engaged with multiple platforms linked to Telekopye; these entities are well aware of such scams and have implemented various strategies to combat them effectively. Despite the constant advancements in scam tactics, warnings continue to be advised for customers to protect themselves from the ever-evolving array of fraudulent schemes.
IoCs
Recordsdata
| PHP/HackTool.Telekopye.B | Telekopye bot. | ||
| PHP/HackTool.Telekopye.B | Telekopye bot. | ||
| PHP/HackTool.Telekopye.A | Telekopye bot. | ||
| PHP/HackTool.Telekopye.B | Telekopye bot. | ||
| PHP/HackTool.Telekopye.A | Telekopye bot. | ||
| PHP/HackTool.Telekopye.A | Telekopye bot. | ||
| PHP/HackTool.Telekopye.A | Telekopye bot. |
Community
| N/A | Cloudflare, Inc. | 2024-05-30 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-06-28 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-06-01 | Telekopye phishing area. | |
| N/A | TIMEWEB-RU | 2024-01-02 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-05-31 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-05-30 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-05-26 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-05-30 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-05-31 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-05-30 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-05-29 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-05-29 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-06-02 | Telekopye phishing area. | |
| N/A | Cloudflare, Inc. | 2024-05-29 | Telekopye phishing area. |
MITRE ATT&CK strategies
This desk was constructed utilizing of the MITRE ATT&CK framework.
| Collect Sufferer Identification Info | The Telekopye software enables users to compile detailed cost cards, including mobile phone numbers and email addresses. Through phishing websites? | ||
| Purchase Infrastructure: Domains | Telescope operators typically register their own unique domain names. | ||
| Set up Accounts | Telekopye operators establish online accounts on marketplaces. | ||
| Create unique login credentials for new email accounts to ensure secure and efficient management of digital communications. | Telecopy operators arrange email addresses associated with the domains they register. | ||
| Compromise Accounts: E mail Accounts | Cybercriminals employing telecopye operations exploit compromised email accounts to amplify their clandestine nature. | ||
| Develop Capabilities: Malware | Telekopye is customized malware. | ||
| Receive Capabilities: Instrument | Telecope operators employ additional bots to facilitate money laundering, gather market insights, and deploy distributed denial-of-service (DDoS) protection measures. | ||
| Phishing: Spearphishing Hyperlink | Telekopye transmits emails and SMS messages containing links to fraudulent online destinations, attempting to deceive victims into divulging sensitive information. | ||
| Enter Seize: Internet Portal Seize | Telekopye’s internet pages capture sensitive information and transmit it to the relevant operators. |

