Microsoft Menace Intelligence has noticed financially motivated risk actor Storm-0501 constantly evolving their campaigns to attain sharpened give attention to cloud-based ways, strategies, and procedures (TTPs). Whereas the risk actor has been recognized for focusing on hybrid cloud environments, their major goal has shifted from deploying on-premises endpoint ransomware to utilizing cloud-based ransomware ways.
In contrast to conventional on-premises ransomware, the place the risk actor usually deploys malware to encrypt crucial recordsdata throughout endpoints inside the compromised community after which negotiates for a decryption key, cloud-based ransomware introduces a elementary shift. Leveraging cloud-native capabilities, Storm-0501 quickly exfiltrates giant volumes of knowledge, destroys knowledge and backups inside the sufferer atmosphere, and calls for ransom—all with out counting on conventional malware deployment.
Storm-0501’s focusing on is opportunistic. The risk actor initially deployed Sabbath ransomware in an assault in opposition to United States college districts in 2021. In November 2023, the actor focused the healthcare sector. Through the years, the actor switched ransomware payloads a number of instances, utilizing Embargo ransomware in 2024 assaults.
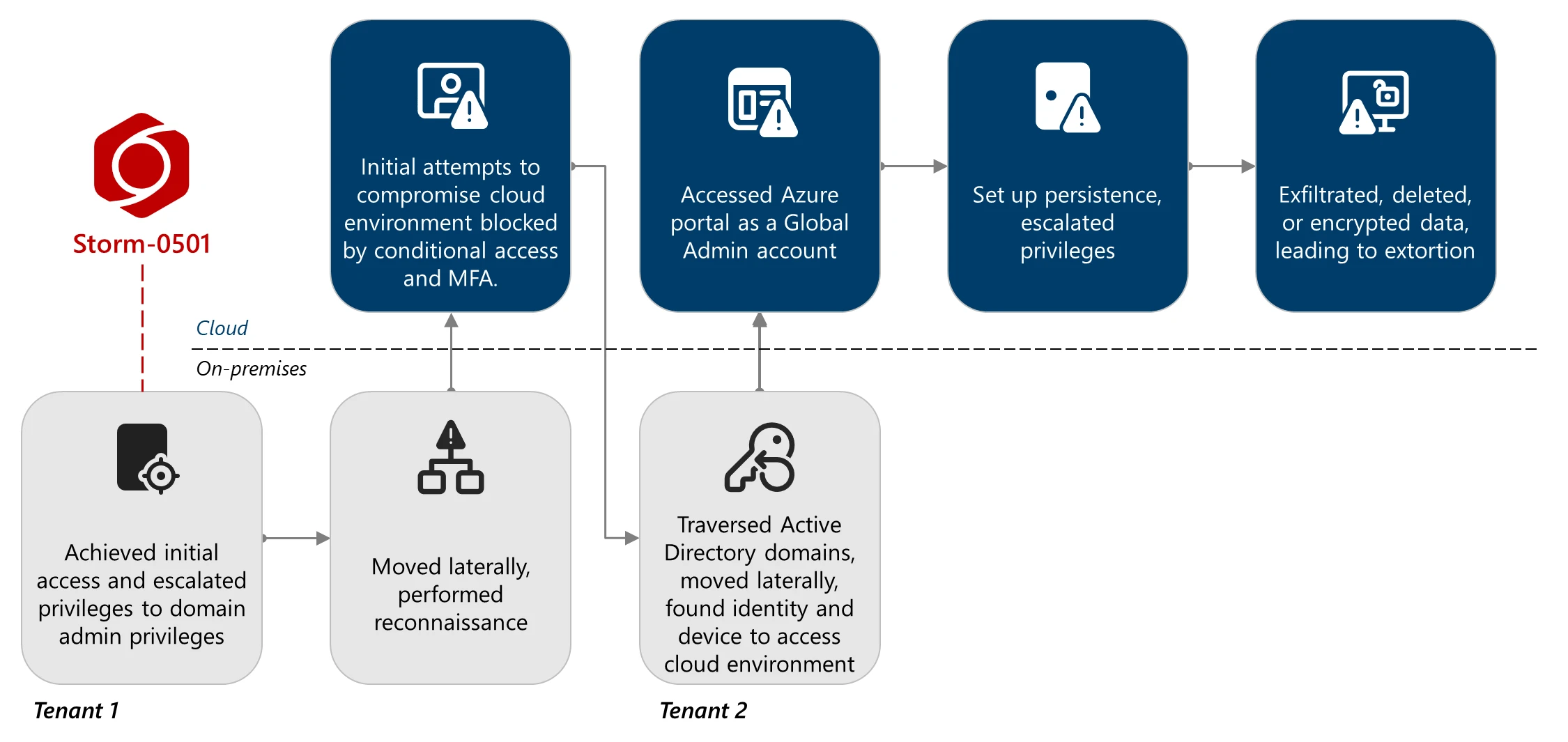
In September 2024, we revealed a weblog detailing how Storm-0501 prolonged its on-premises ransomware operations into hybrid cloud environments. The risk actor gained a foothold by compromising Lively Listing environments after which pivoted to Microsoft Entra ID, escalating privileges on hybrid and cloud identities to realize international administrator privileges. The impression section of those assaults took one in all two varieties: implanting backdoors in Entra ID tenant configurations utilizing maliciously added federated domains to permit sign-in as almost any consumer or deploying on-premises ransomware to encrypt endpoints and servers, ultimately demanding ransom for the decryption keys.
Storm-0501 has continued to reveal proficiency in shifting between on-premises and cloud environments, exemplifying how risk actors adapt as hybrid cloud adoption grows. They hunt for unmanaged gadgets and safety gaps in hybrid cloud environments to evade detection and escalate cloud privileges and, in some instances, traverse tenants in multi-tenant setups to attain their targets.
On this weblog put up, we describe the impression of a latest Storm-0501 assault on a compromised cloud atmosphere. We hint how the risk actor achieved cloud-based ransomware impression by cloud privilege escalation, making the most of safety and visibility gaps throughout the compromised atmosphere, and pivoting from on-premises to cloud pivots. Understanding how such assaults are carried out is crucial in defending cloud environments. Beneath we share safety and mitigation suggestions, together with strengthening protections for cloud identities and cloud assets, and detection steerage throughout Microsoft safety options to assist organizations harden their networks in opposition to these assaults.
On-premises compromise and pivot to the cloud
In a latest marketing campaign, Storm-0501 compromised a big enterprise composed of a number of subsidiaries, every working its personal Lively Listing area. These domains are interconnected by area belief relationships, enabling cross-domain authentication and useful resource entry.
The cloud atmosphere mirrors this complexity. Completely different subsidiaries keep separate Microsoft Azure tenants, with various Microsoft Defender product protection. Notably, just one tenant had Microsoft Defender for Endpoint deployed, and gadgets from a number of Lively Listing domains had been onboarded to this single tenant’s license. This fragmented deployment created visibility gaps throughout the atmosphere.
Lively Listing domains had been synchronized to a number of Entra ID tenants utilizing Entra Join Sync servers. In some instances, a single area was synced to a couple of tenant, additional complicating id administration and monitoring. For readability, this weblog focuses on the 2 tenants impacted by the assault: one the place on-premises exercise was noticed, and one other the place cloud-based exercise occurred.
On-premises exercise
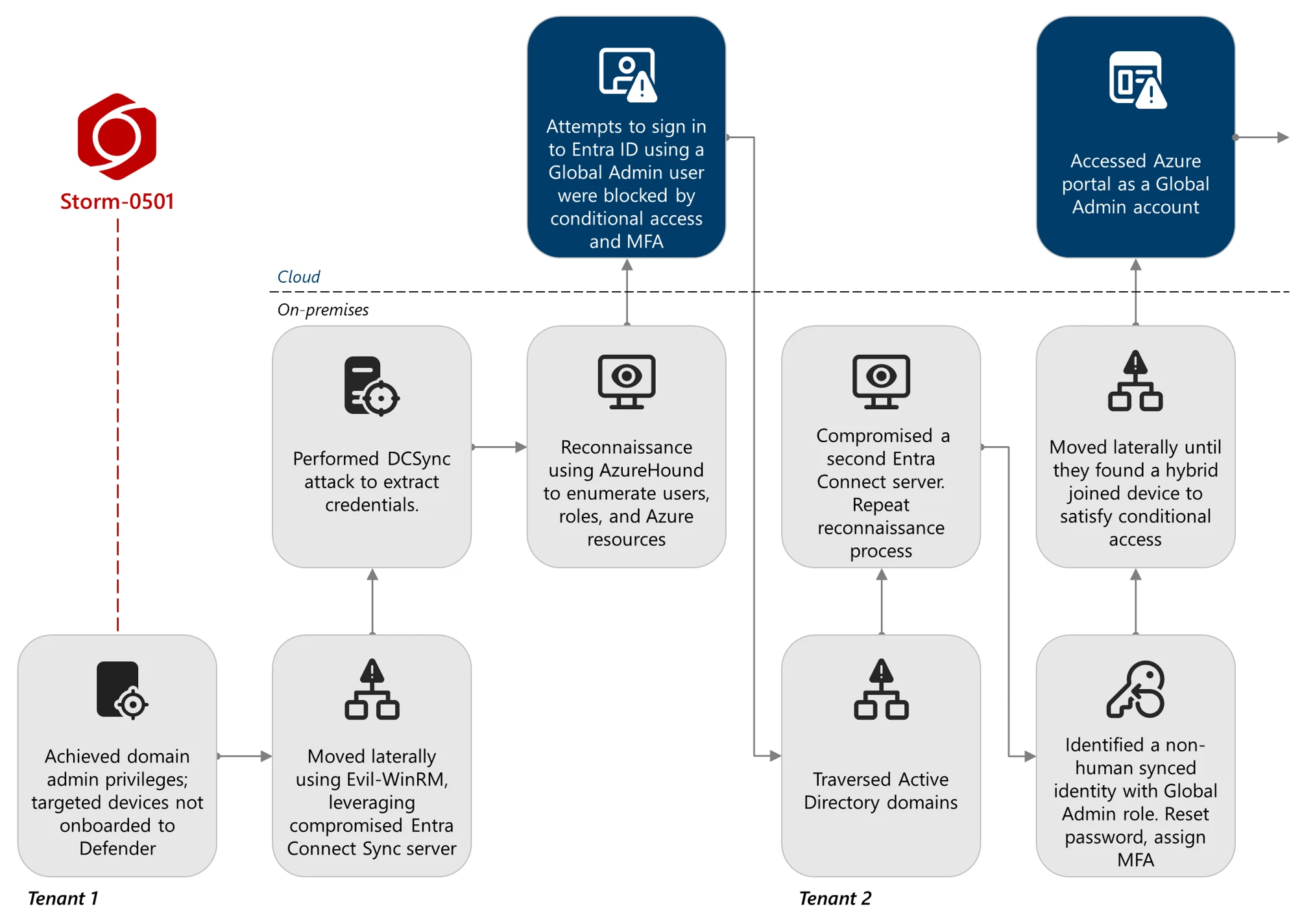
For the needs of this weblog, we focus our evaluation on the post-compromise section of the on-premises assault, which means that the risk actor had already achieved area administrator privileges within the focused area. Learn our earlier weblog for a extra complete overview of Storm-0501 ways in on-premises environments.
The restricted deployment of Microsoft Defender for Endpoint throughout the atmosphere considerably hindered detection. Of the a number of compromised domains, just one area had vital Defender for Endpoint deployment, leaving parts of the community unmonitored. On the few onboarded gadgets the place Storm-0501 exercise was noticed, we famous that the risk actor carried out reconnaissance earlier than executing malicious actions. Particularly, the risk actor used the next instructions:
sc question sense
sc question windefend
The risk actor checked for the presence of Defender for Endpoint companies, suggesting a deliberate effort to keep away from detection by focusing on non-onboarded techniques. This highlights the significance of complete endpoint protection.
Lateral motion was facilitated utilizing Evil-WinRM, a post-exploitation instrument that makes use of PowerShell over Home windows Distant Administration (WinRM) for distant code execution. The abovementioned instructions had been executed over classes initiated with the instrument, in addition to discovery utilizing different frequent native Home windows instruments and instructions resembling quser.exe and web.exe. Earlier within the assault, the risk actor had compromised an Entra Join Sync server that was not onboarded to Defender for Endpoint. We assess that this server served as a pivot level, with the risk actor establishing a tunnel to maneuver laterally inside the community.
The risk actor additionally carried out a DCSync assault, a method that abuses the Listing Replication Service (DRS) Distant Protocol to simulate the conduct of a website controller. By impersonating a website controller, the risk actor might request password hashes for any consumer within the area, together with privileged accounts. This system is usually used to extract credentials with out triggering conventional authentication-based alerts.
Pivot to the cloud
Following the on-premises compromise of the primary tenant, the risk actor leveraged the Entra Join Sync Listing Synchronization Account (DSA) to enumerate customers, roles, and Azure assets inside the tenant. This reconnaissance was carried out utilizing AzureHound, a instrument designed to map relationships and permissions in Azure environments and consequently discover potential assault paths and escalations.
Shortly thereafter, the risk actor tried to check in as a number of privileged customers. These makes an attempt had been unsuccessful, blocked by Conditional Entry insurance policies and multifactor authentication (MFA) necessities. This means that whereas Storm-0501 had legitimate credentials, they lacked the mandatory second issue or had been unable to fulfill coverage circumstances.
Undeterred, Storm-0501 shifted ways. Leveraging their foothold within the Lively Listing atmosphere, they traversed between Lively Listing domains and ultimately moved laterally to compromise a second Entra Join server related to totally different Entra ID tenant and Lively Listing area. The risk actor extracted the Listing Synchronization Account to repeat the reconnaissance course of, this time focusing on identities and assets within the second tenant.
Identification escalation
On account of the invention section the place the risk actor leveraged on-premises management to pivot throughout Lively Listing domains and vastly enumerate cloud assets, they gained crucial visibility of the group’s safety posture. They then recognized a non-human synced id that was assigned with the World Administrator position in Microsoft Entra ID on that tenant. Moreover, this account lacked any registered MFA methodology. This enabled the risk actor to reset the consumer’s on-premises password, which shortly after was then legitimately synced to the cloud id of that consumer utilizing the Entra Join Sync service. We recognized that that password change was carried out by the Entra Join’s Listing Synchronization Account (DSA), for the reason that Entra Join Sync service was configured on the most typical mode Password-Hash Synchronization (PHS). Consequently, the risk actor was capable of authenticate in opposition to Entra ID as that consumer utilizing the brand new password.
Since no MFA was registered to that consumer, after efficiently authenticating utilizing the newly assigned password, the risk actor was redirected to easily register a brand new MFA methodology below their management. From then on, the compromised consumer had a registered MFA methodology that enabled the risk actor to satisfy MFA circumstances and adjust to the client’s Conditional Entry insurance policies configuration per useful resource.
To entry the Azure portal utilizing the compromised World Admin account, the risk actor needed to bypass another situation that was enforced by Conditional Entry insurance policies for that useful resource, which require authentication to happen from a Microsoft Entra hybrid joined machine. Hybrid joined gadgets are gadgets which might be joined to each the Lively Listing area and Entra ID. We noticed failed authentication makes an attempt coming from firm gadgets which might be both domain-joined or Entra-joined gadgets that didn’t meet the Conditional Entry situation. The risk actor needed to transfer laterally between totally different gadgets within the community, till we noticed a profitable sign-in to the Azure portal with the World Admin account coming from a server that was hybrid joined.
From the purpose that the risk actor was capable of efficiently meet the Conditional Entry insurance policies and check in to the Azure portal as a World Admin account, Storm-0501 primarily achieved full management over the cloud area. The risk actor then utilized the very best attainable cloud privileges to acquire their targets within the cloud.
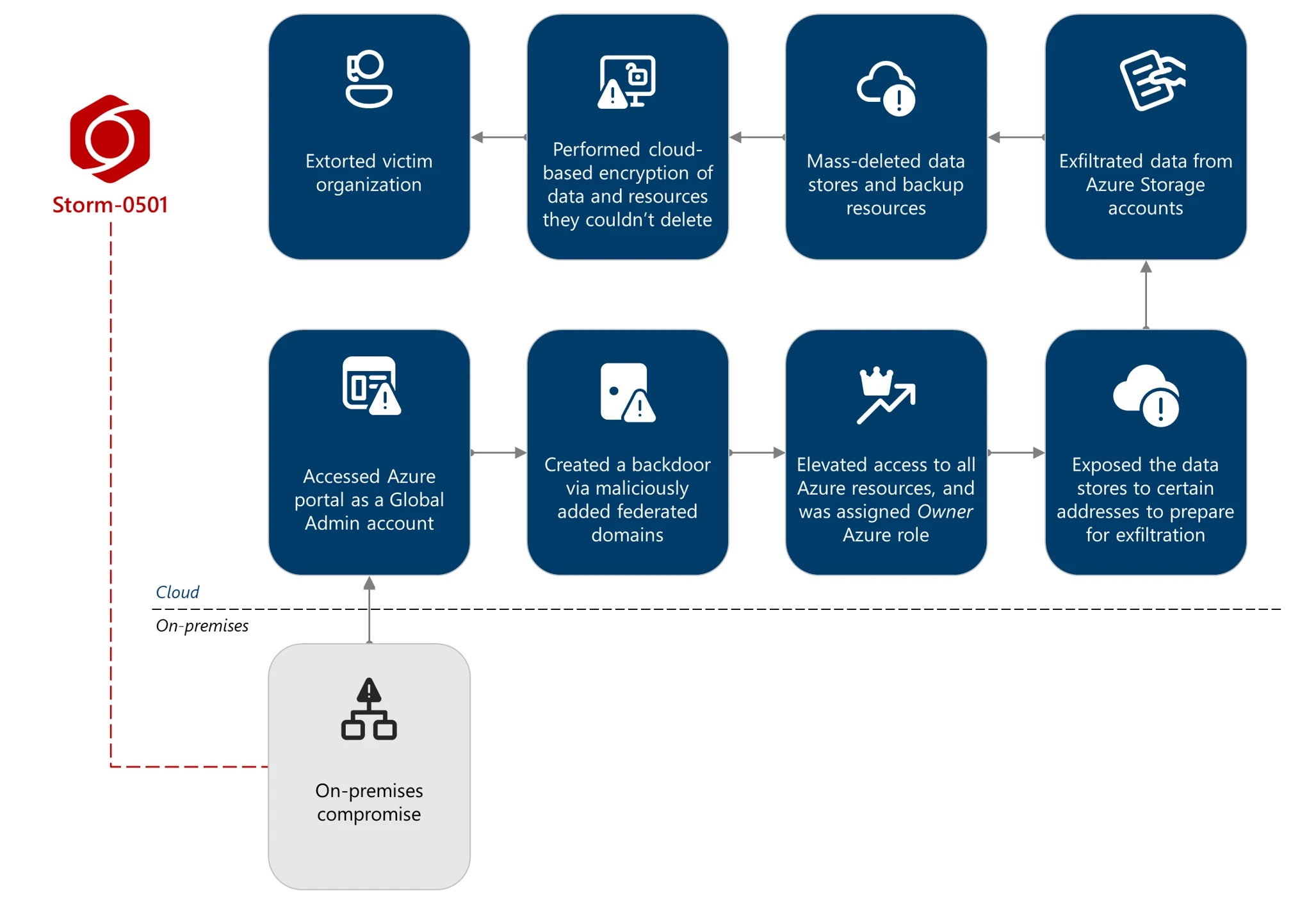
Cloud id compromise: Entra ID
Cloud persistence
Following profitable authentication as a World Admin to the tenant, Storm-0501 instantly established a persistence mechanism. As was seen within the risk actor’s earlier exercise, Storm-0501 created a backdoor utilizing a maliciously added federated area, enabling them to check in as nearly any consumer, in line with the ImmutableId consumer property. The risk actor leveraged the World Administrator Entra position privileges and the AADInternals instrument to register a risk actor-owned Entra ID tenant as a trusted federated area by the focused tenant. To ascertain belief between the 2 tenants, a risk actor-generated root certificates is supplied to the sufferer tenant, which in flip is used to permit authentication requests coming from the risk actor-owned tenant. The backdoor enabled Storm-0501 to craft safety assertion markup language (SAML) tokens relevant to the sufferer tenant, impersonating customers within the sufferer tenant whereas assuming the impersonated consumer’s Microsoft Entra roles.
Cloud compromise: Azure
Azure preliminary entry and privilege escalation
A tenant’s Entra ID and Azure environments are intertwined. And since Storm-0501 gained top-level Entra ID privileges, they might proceed to their ultimate purpose, which was to make use of cloud-based ransomware ways for financial achieve. To realize this purpose, they needed to discover the group’s priceless knowledge shops, and these had been residing within the cloud: in Azure.
As a result of that they had compromised a consumer with the Microsoft Entra World Administrator position, the one operation they needed to do to infiltrate the Azure atmosphere was to elevate their entry to Azure assets. They elevated their entry to Azure assets by invoking the Microsoft.Authorization/elevateAccess/motion operation. By doing so, they gained the Person Entry Administrator Azure position over all of the group’s Azure subscriptions, together with all the precious knowledge residing inside them.
To freely function inside the atmosphere, the risk actor assigned themselves the Proprietor Azure position over all of the Azure subscriptions obtainable by invoking the Microsoft.Authorization/roleAssignments/write operation.
Discovery
After taking management over the group’s Azure atmosphere, we assess that the risk actor initiated a complete discovery section utilizing numerous strategies, together with the utilization of the AzureHound instrument, the place they tried to find the group’s crucial belongings, together with knowledge shops that contained delicate data, and knowledge retailer assets that are supposed to again up on-premises and cloud endpoint gadgets. The risk actor managed to map out the Azure atmosphere, together with the understanding of current atmosphere protections, resembling Azure insurance policies, useful resource locks, Azure Storage immutability insurance policies, and extra.
Protection evasion
The risk actor then focused the group’s Azure Storage accounts. Utilizing the general public entry options in Azure Storage, Storm-0501 uncovered non-remotely accessible accounts to the web and to their very own infrastructure, paving the way in which for knowledge exfiltration section. They did this by using the general public entry options in Azure Storage. To change the Azure Storage account assets, the risk actor abused the Azure Microsoft.Storage/storageAccounts/write operation.
Credential entry
For Azure Storage accounts which have key entry enabled, the risk actor abused their Azure Proprietor position to entry and steal the entry keys for them by abusing the Azure Microsoft.Storage/storageAccounts/listkeys/motion operation.
Exfiltration
After exposing the Azure Storage accounts, the risk actor exfiltrated the information in these accounts to their very own infrastructure by abusing the AzCopy Command-line instrument (CLI).
Impression
In on-premises ransomware, the risk actor usually deploys malware that encrypts essential recordsdata on as many endpoints as attainable, then negotiates with the sufferer for the decryption key. In cloud-based ransomware assaults, cloud options and capabilities give the risk actor the potential to rapidly exfiltrate and transmit giant quantities of knowledge from the sufferer atmosphere to their very own infrastructure, destroy the information and backup cloud assets within the sufferer cloud atmosphere, after which demand the ransom.
After finishing the exfiltration section, Storm-0501 initiated the mass-deletion of the Azure assets containing the sufferer group knowledge, stopping the sufferer from taking remediation and mitigation motion by restoring the information. They accomplish that by abusing the next Azure operations in opposition to a number of Azure useful resource suppliers:
- Microsoft.Compute/snapshots/delete – Deletes Azure Snapshot, a read-only, point-in-time copy of an Azure VM’s disk (VHD), capturing its state and knowledge at a selected second, that exists independently from the supply disk and can be utilized as a backup or clone of that disk.
- Microsoft.Compute/restorePointCollections/delete – Deletes the Azure VM Restore Level, which shops digital machines (VM) configuration and point-in-time application-consistent snapshots of all of the managed disks connected to the VM.
- Microsoft.Storage/storageAccounts/delete – Deletes the Azure storage account, which incorporates and group’s Azure Storage knowledge objects: blobs, recordsdata, queues, and tables. In all of Storm-0501 Azure campaigns we investigated, that is the place they primarily targeted, deleting as many Azure Storage account assets as attainable within the atmosphere.
- Microsoft.RecoveryServices/Vaults/backupFabrics/protectionContainers/delete – Deletes an Azure restoration companies vault safety container. A safety container is a logical grouping of assets (like VMs or workloads) that may be backed up collectively, inside the Restoration Companies vault.
Throughout the risk actor’s makes an attempt to mass-delete the data-stores/housing assets, they confronted errors and did not delete among the assets because of the current protections within the atmosphere. These protections embrace Azure useful resource locks and Azure Storage immutability insurance policies. They then tried to delete these protections utilizing the next operations:
- Microsoft.Authorization/locks/delete – Deletes Azure useful resource locks, that are used to stop unintentional consumer deletion and modification of Azure subscriptions, useful resource teams, or assets. The lock overrides any consumer permission.
- Microsoft.Storage/storageAccounts/blobServices/containers/immutabilityPolicies/delete – Deletes Azure storage immutability insurance policies, which defend blob knowledge from being overwritten or deleted.
After efficiently deleting a number of Azure useful resource locks and Azure Storage immutability insurance policies, the risk actor continued the mass deletion of the Azure knowledge shops, efficiently erasing assets in numerous Azure subscriptions. For assets that remained protected by immutability insurance policies, the actor resorted to cloud-based encryption.
To carry out cloud-based encryption, Storm-0501 created a brand new Azure Key Vault and a brand new Buyer-managed key contained in the Key Vault, which is supposed for use to encrypt the left Azure Storage accounts utilizing the Azure Encryption scopes function:
- Microsoft.KeyVault/vaults/write – Creates or modifies an current Azure Key Vault. The risk actor creates a brand new Azure key vault to host the encryption key.
- Microsoft.Storage/storageAccounts/encryptionScopes/write – Creates or modifies Azure storage encryption scopes, which handle encryption with a key that’s scoped to a container or a person blob. Once you outline an encryption scope, you’ll be able to specify whether or not the scope is protected with a Microsoft-managed key or with a customer-managed key that’s saved in Azure Key Vault.
The risk actor abused the Azure Storage encryption scopes function and encrypted the Storage blobs within the Azure Storage accounts. This wasn’t adequate, because the group might nonetheless entry the information with the suitable Azure permissions. In try and make the information inaccessible, the actor deletes the important thing that’s used for the encryption. Nonetheless, it’s vital to notice that Azure Key vaults and keys which might be used for encryption functions are protected by the Azure Key Vault soft-delete function, with a default interval of 90 days, which permits the consumer to retrieve the deleted key/vault from deletion, stopping cloud-based encryption for ransomware functions.
After efficiently exfiltrating and destroying the information inside the Azure atmosphere, the risk actor initiated the extortion section, the place they contacted the victims utilizing Microsoft Groups utilizing one of many beforehand compromised customers, demanding ransom.
Mitigation and safety steerage
Microsoft lately applied a change in Microsoft Entra ID that restricts permissions on the Listing Synchronization Accounts (DSA) position in Microsoft Entra Join Sync and Microsoft Entra Cloud Sync. This modification helps stop risk actors from abusing Listing Synchronization Accounts in assaults to escalate privileges. Moreover, a brand new model launched in Might 2025 introduces fashionable authentication, permitting prospects to configure application-based authentication for enhanced safety (at present in public preview). It is usually vital to allow Trusted Platform Module (TPM) on the Entra Join Sync server to securely retailer delicate credentials and cryptographic keys, mitigating Storm-0501’s credential extraction strategies.
The strategies utilized by risk actors and described on this weblog will be mitigated by adopting the next safety measures:
Defending on-premises
- Activate tamper safety options to stop risk actors from stopping safety companies resembling Microsoft Defender for Endpoint, which might help stop hybrid cloud atmosphere assaults resembling Microsoft Entra Join abuse.
- Run endpoint detection and response (EDR) in block mode in order that Defender for Endpoint can block malicious artifacts, even when your non-Microsoft antivirus doesn’t detect the risk or when Microsoft Defender Antivirus is working in passive mode. EDR in block mode works behind the scenes to remediate malicious artifacts detected post-breach.
- Activate investigation and remediation in full automated mode to permit Defender for Endpoint to take quick motion on alerts to assist remediate alerts, considerably lowering alert quantity.
Defending cloud identities
- Safe accounts with credential hygiene: apply the precept of least privilege and audit privileged account exercise in your Microsoft Entra ID and Azure environments to gradual or cease risk actors.
- Allow Conditional Entry insurance policies – Conditional Entry insurance policies are evaluated and enforced each time the consumer makes an attempt to check in. Organizations can defend themselves from assaults that leverage stolen credentials by enabling insurance policies resembling machine compliance or trusted IP handle necessities.
- Set a Conditional Entry coverage to restrict the entry of Microsoft Entra ID Listing Synchronization Accounts (DSA) from untrusted IP addresses to all cloud apps. Please discuss with the superior looking part and examine the related question to get these IP addresses.
- Guarantee multifactor authentication (MFA) requirement for all customers. Including extra authentication strategies, such because the Microsoft Authenticator app or a cellphone quantity, will increase the extent of safety if one issue is compromised.
- Guarantee separate consumer accounts and mail forwarding for World Administrator accounts. World Administrator (and different privileged teams) accounts ought to be cloud-native accounts with no ties to on-premises Lively Listing. See different greatest practices for utilizing Privileged roles right here.
- Guarantee all current privileged customers have an already registered MFA methodology to guard in opposition to malicious MFA registrations
- Implement Conditional Entry authentication power to require phishing-resistant authentication for workers and exterior customers for crucial apps.
- Discuss with Azure Identification Administration and entry management safety greatest practices for additional steps and suggestions to handle, design, and safe your Entra ID atmosphere.
- Guarantee Microsoft Defender for Cloud Apps connectors are turned on in your group to obtain alerts on the Microsoft Entra ID Listing Synchronization Account and all different customers.
- Allow safety to stop by-passing of cloud Microsoft Entra MFA when federated with Microsoft Entra ID. This enhances safety in opposition to federated domains assaults.
- Set the validatingDomains property of federatedTokenValidationPolicy to “all” to dam makes an attempt to sign-in to any non-federated area (like .onmicrosoft.com) with SAML tokens.
- If solely Microsoft Entra ID performs MFA for a federated area, set federatedIdpMfaBehavior to rejectMfaByFederatedIdp to stop bypassing MFA CAPs.
- Activate Microsoft Entra ID safety to observe identity-based dangers and create risk-based Conditional Entry insurance policies to remediate dangerous sign-ins.
Defending cloud assets
- Use options like Microsoft Defender for Cloud to guard your cloud assets and belongings from malicious exercise, each in posture administration, and risk detection capabilities.
- Allow Microsoft Defender for Useful resource Supervisor as a part of Defender for Cloud to robotically monitor the useful resource administration operations in your group. Defender for Useful resource Supervisor runs superior safety analytics to detect threats and alerts you about suspicious exercise.
- Enabling Defender for Useful resource Supervisor permits customers to analyze Azure administration operations inside the Defender XDR, utilizing the superior looking expertise.
- Make the most of the Azure Monitor exercise log to analyze and monitor Azure administration occasions.
- Make the most of Azure insurance policies for Azure Storage to stop community and safety misconfigurations and maximize the safety of enterprise knowledge saved in your storage accounts.
- Implement Azure Weblog Storage safety suggestions for enhanced knowledge safety.
- Make the most of the choices obtainable for knowledge safety in Azure Storage.
- Allow immutable storage for Azure Blob Storage to guard from unintentional or malicious modification or deletion of blobs or storage accounts.
- Apply Azure Useful resource Supervisor locks to guard from unintentional or malicious modifications or deletions of storage accounts.
- Allow Azure Monitor for Azure Blob Storage to gather, mixture, and log knowledge to allow recreation of exercise trails for investigation functions when a safety incident happens or community is compromised.
- Enabled Microsoft Defender for Storage utilizing a built-in Azure coverage.
- After enabling Microsoft Defender for Storage as a part of Defender for Cloud, make the most of the CloudStorageAggregatedEvents (preview) desk in superior looking to proactively hunt for storage malicious exercise.
- Allow Azure blob backup to guard from unintentional or malicious deletions of blobs or storage accounts.
- Apply the precept of least privilege when authorizing entry to blob knowledge in Azure Storage utilizing Microsoft Entra and RBAC and configure fine-grained Azure Blob Storage entry for delicate knowledge entry by Azure ABAC.
- Use non-public endpoints for Azure Storage account entry to disable public community entry for elevated safety.
- Keep away from utilizing nameless learn entry for blob knowledge.
- Allow purge safety in Azure Key Vaults to stop quick, irreversible deletion of vaults and secrets and techniques. Use the default retention interval of 90 days.
- Allow logs in Azure Key Vault and retain them for as much as a 12 months to allow recreation of exercise trails for investigation functions when a safety incident happens or community is compromised.
- Allow Microsoft Azure Backup for digital machines to guard the information in your Microsoft Azure digital machines, and to create restoration factors which might be saved in geo-redundant restoration vaults.
Basic hygiene suggestions
- Make the most of Microsoft Safety Publicity Administration, obtainable within the Microsoft Defender portal, with capabilities resembling crucial asset safety and assault path evaluation that allow safety groups to proactively scale back publicity and mitigate the impression of Storm-0501 hybrid assault ways. On this case, every of the crucial belongings concerned – Entra Join server, customers with DCSync permissions, World Directors – will be recognized by related alerts and suggestions.
- Examine on-premises and hybrid Microsoft Safety Publicity Administration assault paths. Safety groups can use assault path evaluation to hint cross-domain threats that exploit the crucial Entra Join server to pivot into cloud workloads, escalate privileges, and broaden their attain. Groups can use the ‘Chokepoint’ view within the assault path dashboard in Microsoft Safety Publicity Administration to spotlight entities showing in a number of paths.
- Make the most of the Important asset administration functionality in Microsoft Safety Publicity Administration by configuring your individual customized queries to pinpoint your group’s business-critical belongings in line with your wants, resembling business-critical Azure Storage accounts.
Microsoft Defender XDR detections
Microsoft Defender XDR prospects can discuss with the listing of relevant detections beneath. Microsoft Defender XDR coordinates detection, prevention, investigation, and response throughout endpoints, identities, e-mail, apps to offer built-in safety in opposition to assaults just like the risk mentioned on this weblog.
Prospects with provisioned entry can even use Microsoft Safety Copilot in Microsoft Defender to analyze and reply to incidents, hunt for threats, and defend their group with related risk intelligence.
| Tactic | Noticed exercise | Microsoft Defender protection |
| Preliminary entry | – Suspicious sign-ins | Microsoft Defender XDR – Authentication with compromised credentials – Compromised consumer account in a acknowledged assault sample – Malicious check in from a dangerous IP handle – Malicious check in from an IP handle related to acknowledged attacker infrastructure – Malicious check in from acknowledged attacker infrastructure -Malicious sign-in from an uncommon consumer agent – Malicious sign-in from recognized risk actor IP handle – Profitable authentication from a malicious IP – Profitable authentication from a suspicious IP – Profitable authentication utilizing compromised credentials – Person compromised by session cookie hijack – Person signed in from a recognized malicious IP Tackle – Suspicious Azure sign-in by consumer with lively session on a tool concerned in a credential theft try Microsoft Defender for Identification Microsoft Defender for Cloud Apps Microsoft Defender for Cloud |
| Execution | – Numerous varieties of execution-related suspicious exercise by an attacker had been noticed – Crafting entry tokens and executing actions in opposition to the cloud | Microsoft Defender for Endpoint – Compromised account conducting hands-on-keyboard assault – Potential human-operated malicious exercise – Suspicious cmdlets launch utilizing AADInternals |
| Persistence | – Federated area backdoor was added | Microsoft Defender for Cloud Apps – Backdoor creation utilizing AADInternals instrument |
| Privilege escalation | – Elevated entry to Azure assets – Project of Proprietor Azure position | Microsoft Defender XDR – Suspicious Azure elevate entry operation by a consumer with an lively session on a tool concerned in a credential theft try – Presumably compromised Microsoft Entra Join Sync account elevated its entry to Azure assets – Presumably compromised consumer elevated entry to Azure assets Microsoft Defender for Cloud |
| Protection evasion | – Makes an attempt to tamper with Microsoft Defender Antivirus – Manipulation of Azure Storage account configurations | Microsoft Defender for Endpoint – Try to show off Microsoft Defender Antivirus safety Microsoft Defender for Cloud |
| Credential entry | – Entra Join Sync server compromise and sync accounts extraction – Extracting credentials from distant machines – Executing DCSync operation in opposition to a website controller – Entry Azure Storage accounts entry keys – Creation of a key inside an Azure Key Vault for encryption of Azure Storage knowledge | Microsoft Defender Antivirus – Trojan:Win32/SuspAdSyncAccess.A!EntraConnect – Backdoor:Win32/AdSyncDump!EntraConnect – Habits:Win32/DumpADConnectCreds.A!EntraConnect – Trojan:Win32/SuspAdSyncAccess.A!EntraConnect – Habits:Win32/SuspAdsyncBin.A!EntraConnect Microsoft Defender for Endpoint Microsoft Defender for Identification Microsoft Defender for Cloud Apps Microsoft Defender for Cloud |
| Discovery | – Verifying whether or not Microsoft Defender for Endpoint is onboarded on a machine – Reconnaissance exercise in opposition to Lively Listing/Entra ID/Azure – AzureHound instrument invocation within the cloud atmosphere | Microsoft Defender for Endpoint – Suspicious sequence of exploration actions Microsoft Defender for Cloud Apps Microsoft Defender for Identification Microsoft Defender for Cloud |
| Lateral motion | – Lateral motion between endpoints within the community – Lateral motion utilizing Evil-WinRM – Cloud sign-in makes an attempt utilizing stolen credentials or entry tokens extracted from compromised endpoints | Microsoft Defender for Endpoint – Presumably malicious use of proxy or tunneling instrument – Suspicious distant PowerShell execution Microsoft Defender for Cloud Apps |
| Exfiltration | – Knowledge assortment and theft from Azure Storage accounts | Microsoft Defender for Cloud Defender for Useful resource Supervisor – Suspicious invocation of a high-risk ‘Knowledge Assortment’ operation detected (Preview) Defender for Storage – The entry stage of a doubtlessly delicate storage blob container was modified to permit unauthenticated public entry – Publicly accessible storage containers efficiently found – Publicly accessible storage containers unsuccessfully scanned – Uncommon quantity of knowledge extracted from a storage account – Uncommon deletion in a storage account – Uncommon quantity of knowledge extracted from a delicate blob container – Uncommon variety of blobs extracted from a delicate blob container – Uncommon SAS token was used to entry an Azure storage account from a public IP handle – Suspicious exterior entry to an Azure storage account with overly permissive SAS token – Suspicious exterior operation to an Azure storage account with overly permissive SAS token – Entry from a suspicious IP handle |
| Impression | – Mass Azure knowledge retailer assets deletion and encryption | Microsoft Defender XDR – Suspicious Azure knowledge retailer assets deletion try by a consumer with an lively session on a tool concerned in a credential theft try Microsoft Defender for Cloud |
Menace intelligence experiences
Microsoft prospects can use the next experiences in Microsoft merchandise to get probably the most up-to-date details about the risk actor, malicious exercise, and strategies mentioned on this weblog. These experiences present the intelligence, safety data, and really helpful actions to stop, mitigate, or reply to related threats present in buyer environments.
Microsoft Defender XDR risk analytics
Microsoft Safety Copilot prospects can even use the Microsoft Safety Copilot integration in Microsoft Defender Menace Intelligence, both within the Safety Copilot standalone portal or within the embedded expertise within the Microsoft Defender portal to get extra details about this risk actor.
Looking queries
Microsoft Defender XDR
Microsoft Defender XDR prospects can run the next question to seek out associated exercise of their networks:
Signal-in exercise
Discover sign-in exercise from IdentityLogonEvents, search for unusual conduct, resembling sign-ins from newly seen IP addresses or sign-ins to new purposes which might be non-sync associated:
IdentityLogonEvents | the place Timestamp > in the past(30d) | the place AccountDisplayName incorporates "On-Premises Listing Synchronization Service Account" | lengthen ApplicationName = tostring(RawEventData.ApplicationName) | project-reorder Timestamp, AccountDisplayName, AccountObjectId, IPAddress, ActionType, ApplicationName, OSPlatform, DeviceType The exercise of the sync account is usually repetitive, coming from the identical IP handle to the identical utility. Any deviation from the pure stream is price investigating. Cloud purposes which might be normally accessed by the Microsoft Entra ID sync account are Microsoft Azure Lively Listing Join, Home windows Azure Lively Listing, and Microsoft On-line Syndication Companion Portal.
Cloud exercise
Discover the cloud exercise (ActionType) of the sync account. Much like sign-in exercise, this account by nature performs a sure set of actions together with replace Person., replace Machine., and so forth. New and unusual exercise from this consumer may point out an interactive use of the account, which might official motion from somebody within the group or malicious motion by the risk actor.
CloudAppEvents | the place Timestamp > in the past(30d) | the place AccountDisplayName has "On-Premises Listing Synchronization Service Account" | lengthen Workload = RawEventData.Workload | project-reorder Timestamp, IPAddress, AccountObjectId, ActionType, Software, Workload, DeviceType, OSPlatform, UserAgent, ISP Pay shut consideration to motion from totally different DeviceTypes or OSPlatforms, this account automated service is carried out from one particular machine, so there shouldn’t be any selection in these fields.
Azure administration occasions
Discover Azure administration occasions by querying the brand new CloudAuditEvents desk in superior looking within the Defender portal. The OperationName column signifies the kind of control-plane occasion executed by the consumer.
let Storm0501Operations = dynamic([ //Microsoft.Authorization "Microsoft.Authorization/elevateAccess/action", "Microsoft.Authorization/roleAssignments/write", "Microsoft.Authorization/locks/delete", //Microsoft.Storage "Microsoft.Storage/storageAccounts/write", "Microsoft.Storage/storageAccounts/listkeys/action", "Microsoft.Storage/storageAccounts/delete", "Microsoft.Storage/storageAccounts/blobServices/containers/immutabilityPolicies/delete", "Microsoft.Storage/storageAccounts/encryptionScopes/write", //Microsoft.Compute "Microsoft.Compute/snapshots/delete", "Microsoft.Compute/restorePointCollections/delete", //Microsoft.RecoveryServices "Microsoft.RecoveryServices/Vaults/backupFabrics/protectionContainers/delete", //Microsoft.KeyVault "Microsoft.KeyVault/vaults/write" ]); CloudAuditEvents | the place Timestamp > in the past(30d) | the place AuditSource == "Azure" and DataSource == "Azure Logs" | the place OperationName in~ (Storm0501Operations) | lengthen EventName = RawEventData.eventName | lengthen UserId = RawEventData.principalOid, ApplicationId = RawEventData.applicationId | lengthen Standing = RawEventData.standing, SubStatus = RawEventData.subStatus | lengthen Claims = parse_json(tostring(RawEventData.claims)) | lengthen UPN = Claims["http://schemas.xmlsoap.org/ws/2005/05/identity/claims/upn"] | lengthen AuthMethods = Claims["http://schemas.microsoft.com/claims/authnmethodsreferences"] | project-reorder ReportId, EventName, Timestamp, UPN, UserId, AuthMethods, IPAddress, OperationName, AzureResourceId, Standing, SubStatus, ResourceId, Claims, ApplicationId Publicity of assets and customers
Discover Microsoft Safety Publicity Administration capabilities by querying the ExposureGraphNodes and ExposureGraphEdges tables within the superior looking within the Defender portal. By using these tables, you’ll be able to determine crucial belongings, together with Azure Storage accounts that include delicate knowledge or protected by an immutable storage coverage. All predefined criticality guidelines will be discovered right here: Predefined classifications
ExposureGraphNodes | the place NodeLabel =~ "microsoft.storage/storageaccounts" // Criticality examine | lengthen CriticalityInfo = NodeProperties["rawData"]["criticalityLevel"] | the place isnotempty( CriticalityInfo) | lengthen CriticalityLevel = CriticalityInfo["criticalityLevel"] | lengthen CriticalityLevel = case( CriticalityLevel == 0, "Important", CriticalityLevel == 1, "Excessive", CriticalityLevel == 2, "Medium", CriticalityLevel == 3, "Low", "") | lengthen CriticalityRules = CriticalityInfo["ruleNames"] | lengthen StorageContainsSensitiveData = CriticalityRules has "Databases with Delicate Knowledge" | lengthen ImmutableStorageLocked = CriticalityRules has "Immutable and Locked Azure Storage" // Publicity examine | lengthen ExposureInfo = NodeProperties["rawData"]["exposedToInternet"] | project-reorder NodeName, NodeId, CriticalityLevel, CriticalityRules, StorageContainsSensitiveData, ImmutableStorageLocked, ExposureInfo The next question can determine crucial customers who’re primarily assigned with privileged Microsoft Entra roles, together with World Administrator:
ExposureGraphNodes | the place NodeLabel =~ "consumer" | lengthen UserId = NodeProperties["rawData"]["accountObjectId"] | lengthen IsActive = NodeProperties["rawData"]["isActive"] // Criticality examine | lengthen CriticalityInfo = NodeProperties["rawData"]["criticalityLevel"] | the place isnotempty(CriticalityInfo) | lengthen CriticalityLevel = CriticalityInfo["criticalityLevel"] | lengthen CriticalityLevel = case( CriticalityLevel == 0, "Important", CriticalityLevel == 1, "Excessive", CriticalityLevel == 2, "Medium", CriticalityLevel == 3, "Low", "") | lengthen CriticalityRules = CriticalityInfo["ruleNames"] | lengthen GlobalAdministrator = CriticalityRules has "World Administrator" | project-reorder NodeName, NodeId, UserId, IsActive, CriticalityLevel, CriticalityRules, GlobalAdministrator Omri Refaeli, Karam Abu Hanna, and Alon Marom
Be taught extra
For the most recent safety analysis from the Microsoft Menace Intelligence group, take a look at the Microsoft Menace Intelligence Weblog.
To get notified about new publications and to hitch discussions on social media, observe us on LinkedIn, X (previously Twitter), and Bluesky.
To listen to tales and insights from the Microsoft Menace Intelligence group in regards to the ever-evolving risk panorama, take heed to the Microsoft Menace Intelligence podcast.

