
A wave of knowledge breaches impacting corporations like Qantas, Allianz Life, LVMH, and Adidas has been linked to the ShinyHunters extortion group, which has been utilizing voice phishing assaults to steal information from Salesforce CRM cases.
In June, Google’s Menace Intelligence Group (GTIG) warned that risk actors tracked as UNC6040 had been focusing on Salesforce clients in social engineering assaults.
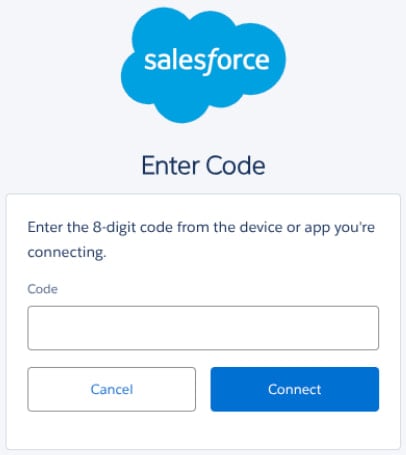
In these assaults, the risk actors impersonated IT help employees in cellphone calls to focused staff, trying to influence them into visiting Salesforce’s linked app setup web page. On this web page, they had been informed to enter a “connection code”, which linked a malicious model of Salesforce’s Knowledge Loader OAuth app to the goal’s Salesforce surroundings.
In some circumstances, the Knowledge Loader part was renamed to “My Ticket Portal,” to make it extra convincing within the assaults.
Supply: Google
GTIG says that these assaults had been normally performed by means of vishing (voice phishing), however credentials and MFA tokens had been additionally stolen by means of phishing pages that impersonated Okta login pages.
Across the time of this report, a number of corporations reported information breaches involving third-party customer support or cloud-based CRM techniques.
LVMH subsidiaries Louis Vuitton, Dior, and Tiffany & Co. every disclosed unauthorized entry to a buyer data database, with Tiffany Korea notifying clients the attackers breached a “vendor platform used for managing buyer information.”
Adidas, Qantas, and Allianz Life additionally reported breaches involving third-party techniques, with Allianz confirming it was a third-party buyer relationship administration platform.
“On July 16, 2025, a malicious risk actor gained entry to a third-party, cloud-based CRM system utilized by Allianz Life Insurance coverage Firm of North America (Allianz Life),” an Allianz Life spokesperson informed BleepingComputer.
Whereas BleepingComputer has discovered that the Qantas information breach additionally concerned a third-party buyer relationship administration platform, the corporate is not going to affirm it’s Salesforce. Nevertheless, earlier reporting from native media claims the information was stolen from Qantas’ Salesforce occasion.
Moreover, courtroom paperwork state that the risk actors focused “Accounts” and “Contacts” database tables, each of that are Salesforce objects.
Whereas none of those corporations have publicly named Salesforce, BleepingComputer has since confirmed that each one had been focused in the identical marketing campaign detailed by Google.
The assaults haven’t led to public extortion or information leaks but, with BleepingComputer studying that the risk actors try to privately extort corporations over electronic mail, the place they title themselves as ShinyHunters.
It’s believed that when these extortion makes an attempt fail, the risk actors will launch stolen data in an extended wave of leaks, much like ShinyHunter’s earlier Snowflake assaults.
Who’s ShinyHunters
The breaches have brought on confusion among the many cybersecurity group and the media, together with BleepingComputer, with the assaults attributed to Scattered Spider (tracked by Mandiant as UNC3944), as these risk actors had been additionally focusing on the aviation, retail, and insurance coverage sectors across the similar time and demonstrated related techniques.
Nevertheless, risk actors related to Scattered Spider are inclined to carry out full-blown community breaches, culminating with information theft and, generally, ransomware. ShinyHunters, tracked as UNC6040, alternatively, tends to focus extra on data-theft extortion assaults focusing on a selected cloud platform or internet software.
It’s BleepingComputer’s and a few safety researchers’ perception that each UNC6040 and UNC3944 encompass overlapping members that talk throughout the similar on-line communities. The risk group can also be believed to overlap with “The Com,” a community of skilled English-speaking cybercriminals.
“Based on Recorded Future intelligence, the overlapping TTPs between recognized Scattered Spider and ShinyHunters assaults point out possible some crossover between the 2 teams,” Allan Liska, an Intelligence Analyst for Recorded Future, informed BleepingComputer.
Different researchers have informed BleepingComputer that ShinyHunters and Scattered Spider look like working in lockstep, focusing on the identical industries on the similar time, making it tougher to attribute assaults.
Some additionally consider that each teams have ties to risk actors from the now-defunct Lapsus$ hacking group, with experiences indicating that one of many just lately arrested Scattered Spider hackers was additionally in Lapsus$.
One other principle is that ShinyHunters is appearing as an extortion-as-a-service, the place they extort corporations on behalf of different risk actors in trade for a income share, much like how ransomware-as-a-service gangs function.
This principle is supported by earlier conversations BleepingComputer has had with ShinyHunters, the place they claimed to not be behind a breach, however simply appearing as the vendor of the stolen information.
These breaches embrace PowerSchool, Oracle Cloud, the Snowflake data-theft assaults, AT&T, NitroPDF, Wattpad, MathWay, and many extra.
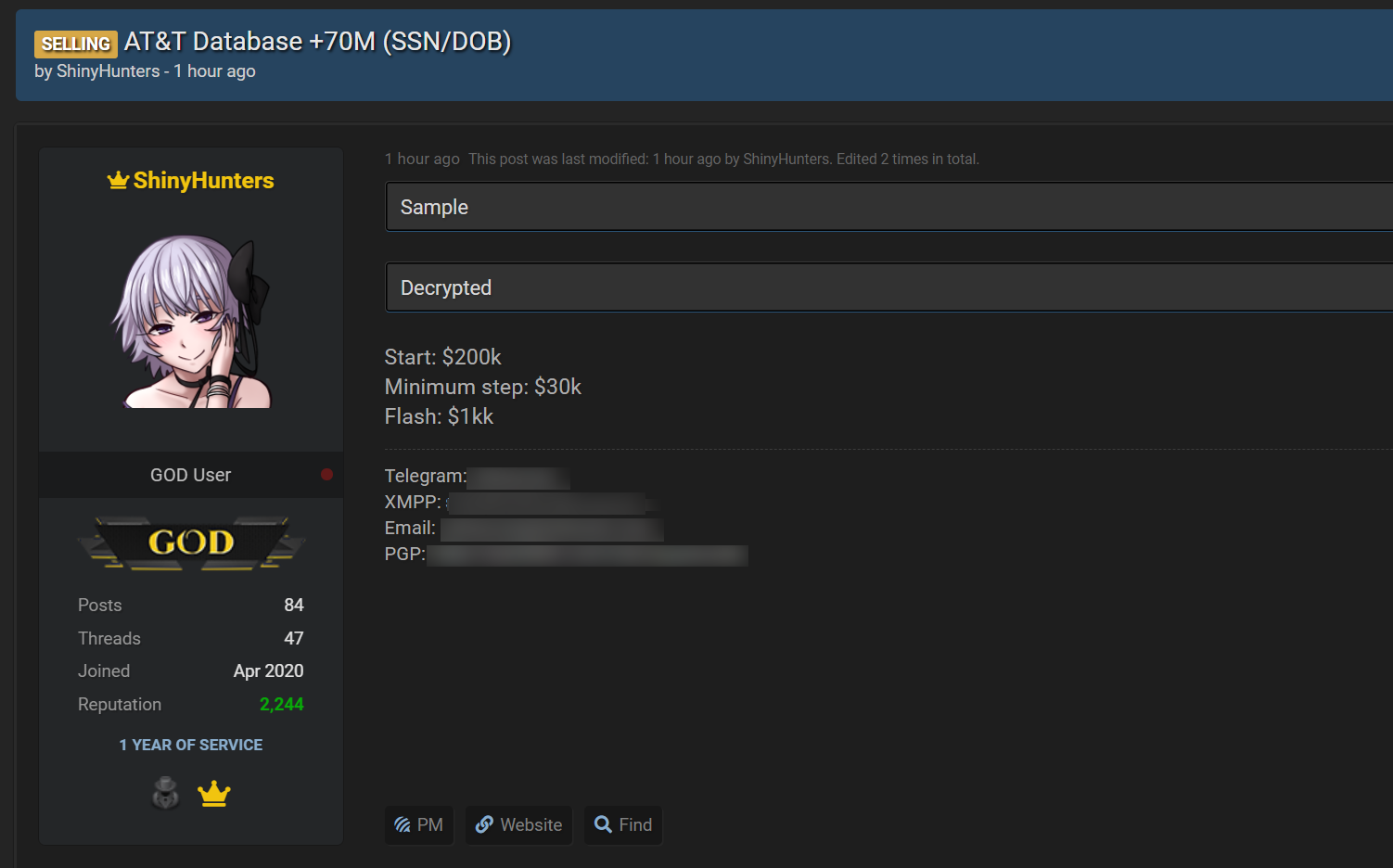
Supply: BleepingComputer
To muddy the waters additional, there have been quite a few arrests of individuals linked to the title “ShinyHunters,” together with those that have been arrested for the Snowflake data-theft assaults, breaches at PowerSchool, and the operation of the Breached v2 hacking discussion board.
But even after these arrests, new assaults happen with corporations receiving extortion emails stating, “We’re ShinyHunters,” referring to themselves as a “collective.”
Defending Salesforce cases from assaults
In a press release to BleepingComputer, Salesforce emphasised that the platform itself was not compromised, however quite, clients’ accounts are being breached by way of social engineering.
“Salesforce has not been compromised, and the problems described will not be resulting from any recognized vulnerability in our platform. Whereas Salesforce builds enterprise-grade safety into every part we do, clients additionally play a vital position in retaining their information secure — particularly amid an increase in refined phishing and social engineering assaults,” Salesforce informed BleepingComputer.
“We proceed to encourage all clients to comply with safety finest practices, together with enabling multi-factor authentication (MFA), implementing the precept of least privilege, and thoroughly managing linked functions. For extra data, please go to: https://www.salesforce.com/weblog/protect-against-social-engineering/.”
Salesforce is urging clients to strengthen their safety posture by:
- Imposing trusted IP ranges for logins
- Following the precept of least privilege for app permissions
- Enabling multi-factor authentication (MFA)
- Proscribing use of linked apps and managing entry insurance policies
- Utilizing Salesforce Protect for superior risk detection, occasion monitoring, and transaction insurance policies
- Including a delegated Safety Contact for incident communication
Additional particulars on these mitigations might be present in Salesforce’s steerage linked above.
CISOs know that getting board buy-in begins with a transparent, strategic view of how cloud safety drives enterprise worth.
This free, editable board report deck helps safety leaders current threat, impression, and priorities in clear enterprise phrases. Flip safety updates into significant conversations and quicker decision-making within the boardroom.


