
SAP has launched patches to handle a second vulnerability exploited in latest assaults focusing on SAP NetWeaver servers as a zero-day.
The corporate issued safety updates for this safety flaw (CVE-2025-42999) on Monday, Might 12, saying it was found whereas investigating zero-day assaults involving one other unauthenticated file add flaw (tracked as CVE-2025-31324) in SAP NetWeaver Visible Composer that was fastened in April.
“SAP is conscious of and has been addressing vulnerabilities in SAP NETWEAVER Visible Composer,” a SAP spokesperson instructed BleepingComputer. “We ask all clients utilizing SAP NETWEAVER to put in these patches to guard themselves. The Safety Notes may be discovered right here: 3594142 & 3604119.”
ReliaQuest first detected the assaults exploiting CVE-2025-31324 as a zero-day in April, reporting that risk actors have been importing JSP internet shells to public directories and the Brute Ratel crimson group device after breaching clients’ programs by way of unauthorized file uploads on SAP NetWeaver. The hacked situations have been totally patched, indicating the attackers used a zero-day exploit.
This malicious exercise was additionally confirmed by cybersecurity companies watchTowr and Onapsis, who additionally noticed the attackers importing internet shell backdoors on unpatched situations uncovered on-line. Forescout’s Vedere Labs has linked a few of these assaults to a Chinese language risk actor it tracks as Chaya_004.
Onyphe CTO Patrice Auffret instructed BleepingComputer in late April that “One thing like 20 Fortune 500/World 500 firms are susceptible, and plenty of of them are compromised,” including that there have been 1,284 susceptible situations uncovered on-line on the time, 474 already compromised.
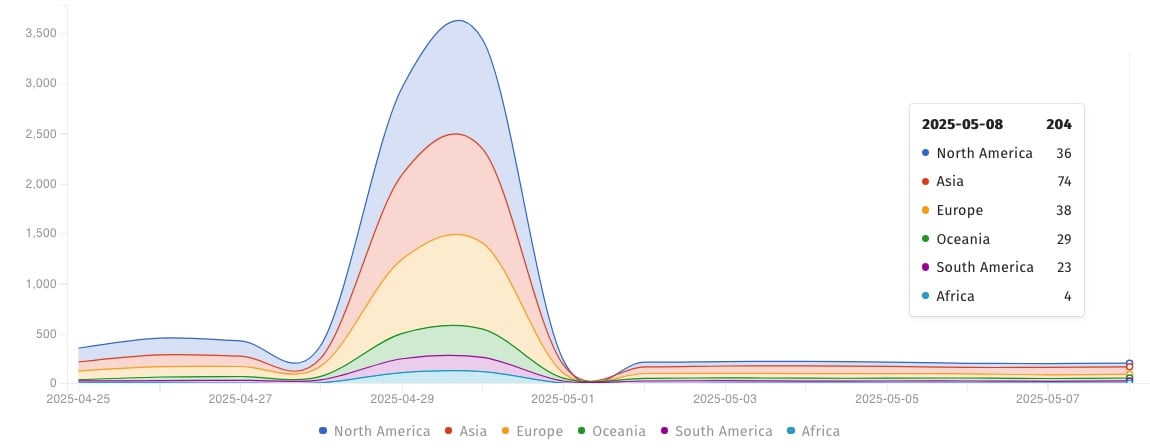
The Shadowserver Basis is now monitoring over 2040 SAP Netweaver servers uncovered on the Web and susceptible to assaults.
New flaw additionally exploited in zero-day assaults
Whereas SAP didn’t affirm that CVE-2025-42999 was exploited within the wild, Onapsis CTO Juan Pablo Perez-Etchegoyen instructed BleepingComputer that the risk actors have been chaining each vulnerabilities in assaults since January.
“The assaults we noticed throughout March 2025 (that began with primary proves again in January 2025) are literally abusing each, the shortage of authentication (CVE-2025-31324) in addition to the insecure de-serialization (CVE-2025-42999),” Perez-Etchegoyen instructed BleepingComputer.
“This mix allowed attackers to execute arbitrary instructions remotely and with none sort of privileges on the system. This residual threat is principally a de-serialization vulnerability solely exploitable by customers with VisualComposerUser position on the SAP goal system.”
SAP admins are suggested to right away patch their NetWeaver situations and contemplate disabling the Visible Composer service if doable, in addition to limit entry to metadata uploader companies and monitor for suspicious exercise on their servers.
For the reason that assaults began, CISA has added the CVE-2025-31324 flaw to its Identified Exploited Vulnerabilities Catalog, ordering federal businesses to safe their programs by Might 20, as mandated by Binding Operational Directive (BOD) 22-01.
“These kinds of vulnerabilities are frequent assault vectors for malicious cyber actors and pose important dangers to the federal enterprise,” CISA warned.


