Legislation enforcement companies in the USA and Europe at present introduced Operation Endgame, a coordinated motion towards a few of the hottest cybercrime platforms for delivering ransomware and data-stealing malware. Dubbed “the most important ever operation towards botnets,” the worldwide effort is being billed because the opening salvo in an ongoing marketing campaign focusing on superior malware “droppers” or “loaders” like IcedID, Smokeloader and Trickbot.

A body from certainly one of three animated movies launched at present in reference to Operation Endgame.
Operation Endgame targets the cybercrime ecosystem supporting droppers/loaders, slang phrases used to explain tiny, custom-made applications designed to surreptitiously set up malware onto a goal system. Droppers are sometimes used within the preliminary levels of a breach, they usually permit cybercriminals to bypass safety measures and deploy extra dangerous applications, together with viruses, ransomware, or adware.
Droppers like IcedID are most frequently deployed by electronic mail attachments, hacked web sites, or bundled with professional software program. For instance, cybercriminals have lengthy used paid advertisements on Google to trick folks into putting in malware disguised as in style free software program, comparable to Microsoft Groups, Adobe Reader and Discord. In these instances, the dropper is the hidden element bundled with the professional software program that quietly hundreds malware onto the person’s system.
Droppers stay such a crucial, human-intensive element of practically all main cybercrime enterprises that the most well-liked have changed into full-fledged cybercrime companies of their very own. By focusing on the people who develop and preserve dropper companies and their supporting infrastructure, authorities are hoping to disrupt a number of cybercriminal operations concurrently.
In line with a press release from the European police company Europol, between Might 27 and Might 29, 2024 authorities arrested 4 suspects (one in Armenia and three in Ukraine), and disrupted or took down greater than 100 Web servers in Bulgaria, Canada, Germany, Lithuania, the Netherlands, Romania, Switzerland, the UK, United States and Ukraine. Authorities say in addition they seized greater than 2,000 domains that supported dropper infrastructure on-line.
As well as, Europol launched info on eight fugitives suspected of involvement in dropper companies and who’re needed by Germany; their names and images have been added to Europol’s “Most Needed” listing on 30 Might 2024.
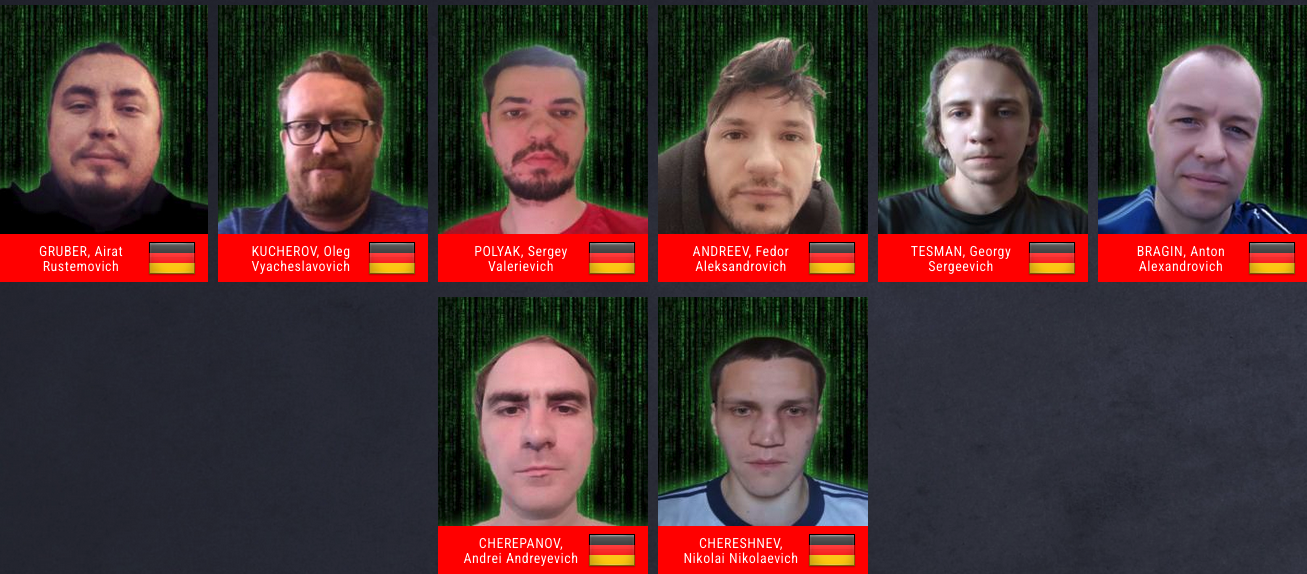
A “needed” poster together with the names and images of eight suspects needed by Germany and now on Europol’s “Most Needed” listing.
“It has been found by the investigations up to now that one of many principal suspects has earned not less than EUR 69 million in cryptocurrency by renting out legal infrastructure websites to deploy ransomware,” Europol wrote. “The suspect’s transactions are always being monitored and authorized permission to grab these property upon future actions has already been obtained.”
There have been quite a few such coordinated malware takedown efforts prior to now, and but typically the substantial quantity of coordination required between regulation enforcement companies and cybersecurity companies concerned just isn’t sustained after the preliminary disruption and/or arrests.
However a brand new web site erected to element at present’s motion — operation-endgame.com — makes the case that this time is totally different, and that extra takedowns and arrests are coming. “Operation Endgame doesn’t finish at present,” the location guarantees. “New actions will likely be introduced on this web site.”
A message on operation-endgame.com guarantees extra regulation enforcement and disruption actions.
Maybe in recognition that lots of at present’s high cybercriminals reside in international locations which can be successfully past the attain of worldwide regulation enforcement, actions like Operation Endgame appear more and more centered on thoughts video games — i.e., trolling the hackers.
Writing on this month’s problem of Wired, Matt Burgess makes the case that Western regulation enforcement officers have turned to psychological measures as an added approach to decelerate Russian hackers and lower to the center of the sweeping cybercrime ecosystem.
“These nascent psyops embrace efforts to erode the restricted belief the criminals have in one another, driving delicate wedges between fragile hacker egos, and sending offenders personalised messages displaying they’re being watched,” Burgess wrote.
When authorities within the U.S. and U.Okay. introduced in February 2024 that they’d infiltrated and seized the infrastructure utilized by the notorious LockBit ransomware gang, they borrowed the prevailing design of LockBit’s sufferer shaming web site to hyperlink as a substitute to press releases in regards to the takedown, and included a countdown timer that was ultimately changed with the non-public particulars of LockBit’s alleged chief.
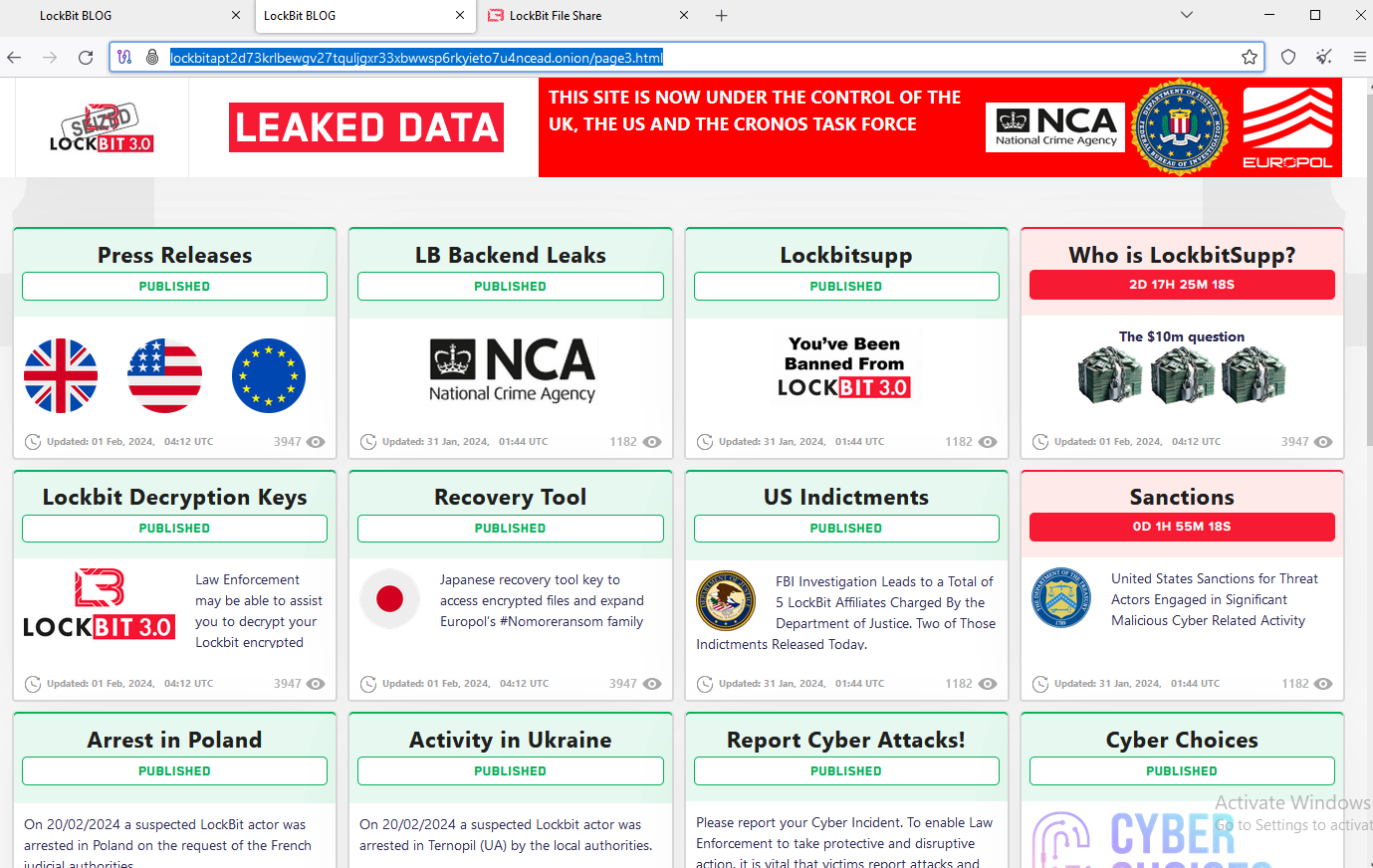
The feds used the prevailing design on LockBit’s sufferer shaming web site to characteristic press releases and free decryption instruments.
The Operation Endgame web site additionally features a countdown timer, which serves to tease the discharge of a number of animated movies that mimic the identical form of flashy, quick ads that established cybercriminals typically produce to advertise their companies on-line. No less than two of the movies embrace a considerable quantity of textual content written in Russian.
The coordinated takedown comes on the heels of one other regulation enforcement motion this week towards what the director of the FBI known as “doubtless the world’s largest botnet ever.” On Wednesday U.S. Division of Justice (DOJ) introduced the arrest of YunHe Wang, the alleged operator of the ten-year-old on-line anonymity service 911 S5. The federal government additionally seized 911 S5’s domains and on-line infrastructure, which allegedly turned computer systems working varied “free VPN” merchandise into Web site visitors relays that facilitated billions of {dollars} in on-line fraud and cybercrime.

