The 2024 vacation season revealed a posh and evolving risk panorama for Distributed Denial-of-Service (DDoS) assaults. This yr’s tendencies included superior ways similar to a rise in DDoS-for-hire operations, the meeting of large DDoS botnets by script kiddies, politically motivated assault campaigns, and the bypass of CDN (Content material Supply Community) protections amongst different evolving threats.
The 2024 vacation season revealed a posh and evolving risk panorama for Distributed Denial-of-Service (DDoS) assaults. This yr’s tendencies included superior ways similar to a rise in DDoS-for-hire operations, the meeting of large DDoS botnets by script kiddies, politically motivated assault campaigns, and the bypass of CDN (Content material Supply Community) protections amongst different evolving threats.
The 2024 vacation season assault panorama in Azure
In the course of the vacation season, we famous a shift in assault patterns from final yr, highlighting how malicious actors repeatedly refine their ways to bypass DDoS safety.
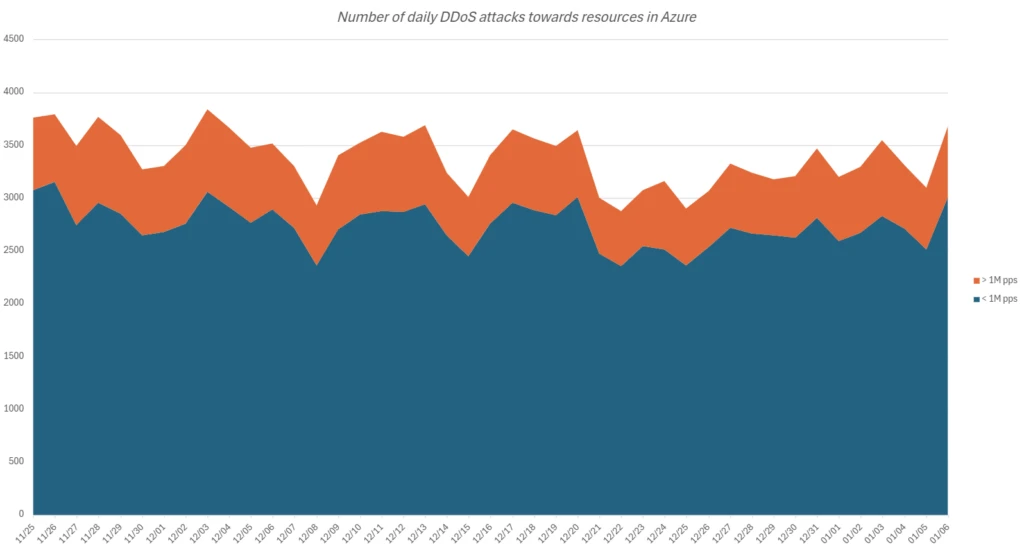
Each day assault quantity
Azure’s safety infrastructure mitigates as much as 3,800 assaults day by day. Massive-scale assaults over a million packets per second (pps) make up about 81% of those, just like final yr’s evaluation. Extremely volumetric assaults exceeding 10M pps are uncommon, at simply 0.2% of all assaults, reflecting attackers’ intention to reduce sources and keep away from detection.
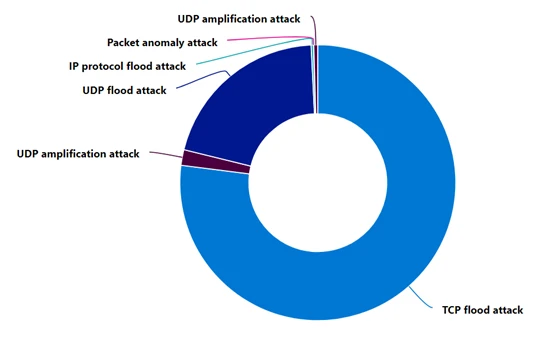
Assault protocols
The 2024 vacation season noticed a predominant use of TCP-based assaults (Transport Management Protocol), concentrating on varied internet purposes and sources, accounting for 77% of the assaults. That is in distinction to final yr when UDP-based assaults (Consumer Datagram Protocol) accounted for almost 80% of the assaults on gaming and different sources. The primary TCP assault vectors this yr had been TCP SYN (Synchronize) and ACK (Acknowledge) floods.
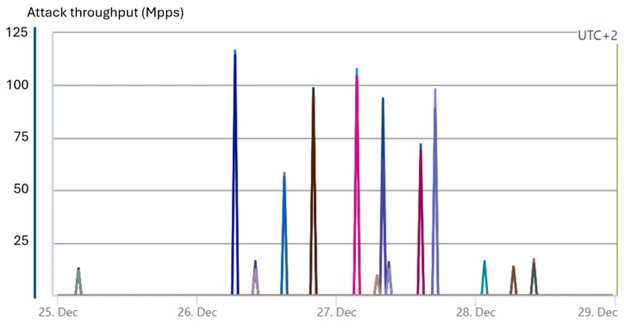
Azure blocks large typhon assault
A staggering assault on gaming sources reached 100-125 million pps in a number of waves. This assault, whose signatures hyperlink to Typhon botnet, was absolutely mitigated by Azure’s defenses.
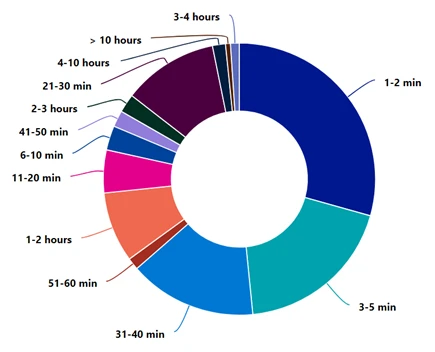
Assaults length
This vacation season once more we witnessed the identical adversaries’ ways of making an attempt to bypass DDoS mitigation methods by launching burst or short-lived assaults. 49% of all assaults lasted as much as 5 minutes, whereas 83% of assaults lasted lower than 40 minutes. It’s insightful to grasp that any DDoS mitigation countermeasure we implement to guard our utility ought to kick in efficient mitigation as quickly as doable.
Political motives and DDoS-for-hire surge
This vacation season, Azure’s assault tendencies mirror international patterns. Politically motivated assaults, pushed by geopolitical tensions, persist. DDoS threats stay a big concern as new actors use accessible instruments to trigger disruption.
The rise of DDoS-for-hire providers, also known as stressers and booters, has gained vital reputation amongst attackers. These platforms, that are readily accessible on cybercriminal boards, have democratized the potential to launch sturdy DDoS assaults, making them attainable for much less subtle criminals at minimal prices. Lately, there was a rise in each the provision and utilization of those providers. Throughout this vacation season, worldwide regulation enforcement companies performed operations similar to Operation PowerOFF final December, ensuing within the arrest of three people and the shutdown of 27 domains related to DDoS-for-hire platforms. Regardless of these efforts, DDoS stressers proceed to thrive, providing a wide range of assault strategies and energy, and are more likely to persist of their prevalence.
Making ready for 2025
The 2024 vacation season has emphasised the continued risk of DDoS assaults. Organizations should improve their cybersecurity methods to counter these evolving threats within the new yr. Strengthening defenses and staying vigilant to new ways is essential in 2025. Azure’s resilience in opposition to superior DDoS threats highlights the significance of strong safety measures for shielding digital belongings and guaranteeing enterprise continuity.
Figuring out publicity factors
Begin by pinpointing which of your purposes are uncovered to the general public web. Evaluating the potential dangers and vulnerabilities of those purposes is essential to understanding the place you could be most vulnerable to assaults.
Recognizing regular operations
Familiarize your self with the traditional habits of your purposes. Azure supplies monitoring providers and greatest practices that can assist you acquire insights into the well being of your purposes and diagnose points successfully.
Simulating assault situations
Repeatedly working assault simulations is an efficient strategy to take a look at your providers’ responses to potential DDoS assaults. Throughout testing, validate that your providers or purposes proceed to perform as anticipated and that there’s no disruption to the consumer expertise. Establish gaps from each a expertise and course of standpoint and incorporate them into your DDoS response technique.
Making certain sturdy safety
With the excessive threat of DDoS assaults, it’s important to have a DDoS safety service like Azure DDoS Safety. This service supplies always-on visitors monitoring, automated assault mitigation upon detection, adaptive real-time tuning, and full visibility of DDoS assaults with real-time telemetry, monitoring, and alerts.
Implementing layered safety
For complete safety, arrange a multi-layered protection by deploying Azure DDoS Safety with Azure Internet Utility Firewall (WAF). Azure DDoS Safety secures the community layer (Layer 3 and 4), whereas Azure WAF safeguards the appliance layer (Layer 7). This mixture ensures safety in opposition to varied kinds of DDoS assaults.
Configuring alerts
Azure DDoS Safety can establish and mitigate assaults with out consumer intervention. Configuring alerts for energetic mitigations can maintain you knowledgeable in regards to the standing of protected public IP sources.
Formulating a response plan
Set up a DDoS response staff with clearly outlined roles and tasks. This staff ought to be adept at figuring out, mitigating, and monitoring an assault, in addition to coordinating with inside stakeholders and clients. Use simulation testing to establish any gaps in your response technique, guaranteeing your staff is ready for varied assault situations.
Searching for skilled help
Within the occasion of an assault, reaching out to technical professionals is important. Azure DDoS Safety clients have entry to the DDoS Fast Response (DRR) staff for help throughout and after assaults. Following an assault, proceed monitoring sources and conduct a retrospective evaluation. Apply learnings to enhance your DDoS response technique, guaranteeing higher preparedness for future incidents.
Name to motion
The 2024 vacation season highlighted the evolving risk panorama of DDoS assaults, with a big improve in DDoS-for-hire operations, large botnets, and politically motivated campaigns. These threats emphasize the necessity for sturdy DDoS safety and a DDoS response plan. Azure helps organizations to remain forward of those threats. Prospects ought to allow multi-layer safety by deploying Azure DDoS Safety with Azure Internet Utility Firewall (WAF). Moreover, clients ought to allow telemetry and alerting capabilities to observe and reply to energetic mitigations successfully.

