If you’re responsible for cybersecurity at a U.S. government agency, you’re likely well-versed with Memorandum M-22-09, “Improving Cybersecurity Across the U.S. Government,” issued by the U.S. Office of Management and Budget (OMB) in January 2022. The following revised memo sets a September 30, 2024, deadline for assembling “specific cybersecurity requirements and objectives” to implement a Zero Trust architecture in compliance with relevant regulations:
(Note: I’ve made some minor changes to improve clarity and readability)
Microsoft has adopted a Zero Trust approach, implementing this security philosophy across our products and within our own corporate environment for maximum protection. We have successfully assisted numerous global organizations, including military branches and civilian companies, in their transformation to a Zero Trust security model, supporting the secure evolution of hundreds of enterprises.
For the past three years, we have closely collaborated with our US authorities clients, enabling us to develop innovative, high-value safety features that help them comply with the requirements outlined in the Government Order, and then deploy these solutions effectively. Here are the developments that embody certificate-based authentication within the cloud, conditional entry authentication capabilities, cross-tenant entry settings, FIDO2 provisioning application programming interfaces (APIs), Azure Digital Desktop assistance for passwordless authentication, and device-bound passkeys.
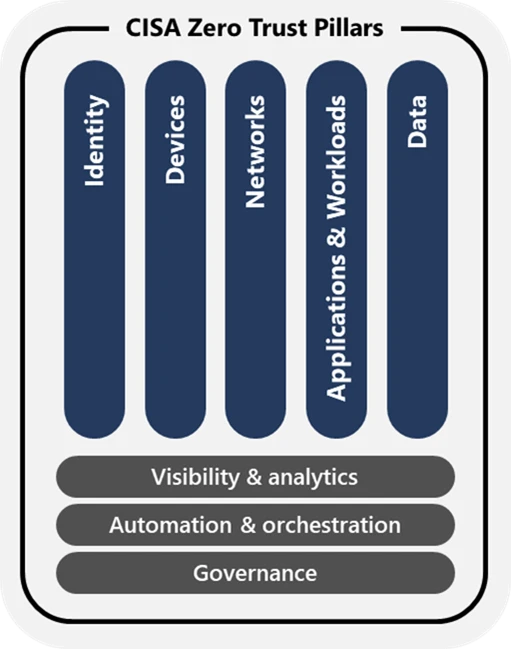
The illustration below illustrates the framework adopted by the US Cybersecurity and Infrastructure Safety Agency (CISA).
As the memo’s deadline nears, it is essential that we capitalize on the progress our clients have achieved by leveraging the capabilities not only to meet requirements for the Id pillar, but also to simplify processes and elevate the user experience for their employees and partners.
Microsoft Entra Identity helps US government customers comply with the M-22-09 requirements for identity verification.
US authorities are mandating that businesses adopt Microsoft Entra ID to streamline identity management, simplify operations, and increase transparency across customer bases, as dictated by a formal memo. With Microsoft Entra Identity, businesses can implement advanced identity and access management capabilities at the utility stage for enhanced, fine-grained control. By introducing phishing-resistant authentication methods for all stakeholders – including employees, contractors, and companions – they will significantly bolster safety measures. Furthermore, the system will scrutinize machine information before granting access to sensitive resources, thereby ensuring an additional layer of security.
:
Company employees utilize enterprise-managed identities to access and utilize the functions they need for their work. Multifactor authentication, designed to thwart sophisticated phishing attacks, safeguards personnel from stealthy online threats.
:
- Firms offering bespoke solutions for corporate clients that can be seamlessly integrated into existing functions and standardized platforms.
- Organizations should implement comprehensive multifactor authentication across their entire enterprise to ensure robust security and protect against potential threats.
- As a supplementary framework to the community layer.
- As a token of appreciation for the hard work and dedication of our valued employees, contractors, and companions,
- For public customers, .
- Password insurance policies .
- Upon authenticating customers and granting them access to sources, companies collect and store relevant information about the verified individual.
Many of our U.S. government authorities, both civilian and military, require consistent solutions across various operational environments. Because it’s accessible within secure and highly classified Microsoft Azure Authority clouds, businesses can standardize on Microsoft Entra ID to safeguard consumer identities, configure granular access permissions in a single location, and provide seamless, simplified, and secure sign-in experiences for employees to utilize across their work functions.
Microsoft Entra ID
Establish robust Zero Trust authentication protocols to secure entry points, prevent identity-based attacks, and manage access to sensitive data and applications.

Microsoft Entra Identity serves as a unified identity management platform.
Individuals familiar with managing multiple identification methods recognize the significant expense and inefficiency involved in doing so? Clients of authorities who have selected Microsoft Entra ID as their primary identity provider (IdP) now enjoy a comprehensive understanding of all users and their corresponding access rights, as mandated by the relevant memo. Additionally, they acquired a centralized entry coverage engine that consolidates alerts from multiple sources, including identities and units, to identify unusual customer behavior, quantify risk, and make instant entry decisions aligned with.
Microsoft Entra ID enables seamless single sign-on (SSO) access to a vast array of sources and applications, including those from Microsoft and hundreds of other providers, regardless of their deployment location – be it on-premises, within Microsoft’s business cloud, or in government clouds. Deployed as a central company identity provider, Microsoft Entra ID further reinforces access to cloud-based resources from Amazon, Google, and Oracle, ensuring seamless integration and enhanced security measures.
Authorities clients facilitate seamless cooperation among disparate entities by leveraging B2B collaboration, thereby enabling secure cross-cloud access scenarios. Their clients can access the necessary functions and documentation without requiring separate credentials, thereby minimizing the attack surface and protecting customers from managing multiple sets of credentials across various identification methods.
Microsoft’s Entra ID enables seamless collaboration across organizations by streamlining identity and access management.
When configuring cross-tenant entry in Microsoft Azure Active Directory (Azure AD), you may need to utilize the Microsoft Entra Exterior ID. This ID is used for authentication purposes and enables seamless collaboration between tenants. To set up this feature, follow these steps:
1. Sign-in to your Azure portal account.
2. Navigate to Azure Active Directory > Properties > Configure cross-tenant entry.
3. In the Tenant details section, select the “Use Microsoft Entra Exterior ID” option.
4. Click Save changes.
By following these steps, you can successfully configure cross-tenant entry with Microsoft Entra Exterior ID in your Azure AD tenant, enabling secure collaboration and streamlined access control for all users involved.
One of our esteemed authority clients, along with its partner organization, implemented cross-tenant access configurations to trust multifactor authentication assertions from each user’s home tenant. Their affiliated entity can now confidently deploy secure, phishing-immune authentication solutions for customer shoppers, without requiring repetitive sign-ups or multiple registrations. The accompanying company explicitly enforces, through its coverage, that customers of the shopper must register using either a Personal Identification Verification (PIV) card or a Common Access Card (CAC) prior to accessing the system.
Configure cross-tenant entry settings to enable seamless B2B collaboration by allowing users from different organizations to securely access and share resources. To get started, navigate to the Microsoft 365 admin center and select “Settings” under “Organization.” Then, click on “Tenant settings” and finally, choose “Cross-tenant entry settings.” Here, you can specify the domains that are allowed to access your organization’s resources, as well as set up authentication and authorization protocols.
Several external authorities buyers sought to provide employees from distinct organizations within the same company access to shared corporate functions, such as human resources systems. Companies leveraged Microsoft’s Enterprise ID to facilitate secure, cloud-agnostic collaboration among employees, outside authorities entities, and partners. To mitigate security risks, they implemented a multi-layered approach by leveraging coverage and cross-tenant entry settings to mandate the use of phishing-resistant authentication before granting access to shared resources for workers. Whether a house tenant belongs to an employee working within an Azure business or government cloud, this method ensures its effectiveness. By facilitating integration with non-Microsoft identity providers, organizations can also collaborate seamlessly with companies utilizing SAML 2.0 or WS-Fed protocols, thereby further enhancing their overall identity management capabilities.
Utilize Azure Active Directory (Azure AD) to streamline the lifecycle management of visitor accounts within your tenant, thereby granting authorized visitors access only to the resources they require, for a duration that is limited by design. Begin right here:
Enabling robust multifactor authentication
By standardising on Microsoft Entra ID, our authority clients have gained the ability to implement phishing-resistant authentication methods seamlessly. In a remarkable collaboration spanning 18 months, we have successfully scaled up the adoption of phishing-resistant multifactor authentication for our US government clients, achieving a staggering 1,900% increase in partnership with Microsoft Entra.
Clients subsequently configure Conditional Entry insurance policies, necessitating stringent, phishing-resistant authentication protocols to access functional areas and data resources, in strict compliance with the memorandum’s stipulations. With Conditional Entry’s authentication capabilities, they can implement insurance policies that mandate more robust authentication protocols dependent on the sensitivity of the device or resource being accessed, as well as the specific operation being attempted.
Microsoft Entra enables robust, phishing-resistant forms of authentication.
- Certificate-based authentication utilizing private identification cards (PIV) or common access cards (CAC).
- Machine-bound passkeys
- FIDO2 safety keys
- Microsoft recently introduced a new feature called passkeys within their Authenticator app. Passkeys are essentially a type of password that replaces traditional username and password combinations for online authentication. They work by generating a unique cryptographic key pair, comprising a private key stored on your device and a public key visible to the application or website you’re trying to access.
- Windows for Business
- The platform now supports seamless single sign-on access to macOS devices in preview mode.
Explore the definitive guide to phishing-resistant authentication in Microsoft Entra through an engaging video series.
While Microsoft Entra ID eliminates the need for frequent password use, detects compromised passwords, and enables self-service password reset, many authorities clients demand the most robust forms of authentication, such as public key infrastructure (PKI)-based good cards with x.509 certificates and passkeys, which eliminate passwords altogether. This enhanced sign-in process enhances safety, streamlines user experience, and minimizes administrative complexity.
Phishing attacks on multifactor authentication (MFA) methods have become increasingly sophisticated, making it imperative to leverage phishing-resistant MFA strategies that ensure the integrity of your organization’s security posture. Microsoft Entra ID is a powerful tool for implementing robust and effective MFA solutions.
To start, organizations should focus on using passwordless MFA approaches such as biometric authentication or smart cards. This eliminates the reliance on vulnerable passwords and reduces the attack surface for attackers. Additionally, utilizing MFA methods that employ advanced security features like behavioral analysis and machine learning can significantly enhance the effectiveness of your MFA strategy.
Another crucial aspect is implementing a layered approach to MFA, combining multiple factors such as something you know (password), something you have (token), and something you are (biometric). This multi-layered approach makes it much more difficult for attackers to bypass the security measures in place.
As we move towards a more modern and secure identity management system, implementing cloud-based authentication is crucial. To ensure a seamless transition, I recommend utilizing a staged rollout strategy. This approach will allow us to test the new system in small increments, gradually introducing changes to our infrastructure while minimizing disruptions to users. By adopting this staged rollout, we can effectively manage risks and identify potential issues early on, ensuring a successful migration to cloud authentication.
One organization aimed to simplify and reduce costs associated with maintaining a traditional, on-premises authentication framework that leverages Active Directory Federation Services (AD FS) for employee PIV card authentication by adopting certificate-based authentication (CBA) within Microsoft’s Entra Identity solution. To ensure a seamless transition, the team employed Staged Rollout, meticulously tracking the threat exercise through Microsoft Entra ID Security dashboards and Graph API logs, which were then exported to their security information and event management (SIEM) system for real-time monitoring. Within just three months, they successfully transitioned all customers to cloud-based CBA within Microsoft Entra, then carefully monitored the environment before confidently decommissioning their AD FS servers altogether.
Microsoft announces public preview of Entra ID FIDO2 provisioning APIs.
The area authority’s division opted for a phishing-resistant authentication approach, migrating employees and distributors through an opt-in process. Consumers seeking password reset assistance from our team also gained access to onboarding guidance for Windows Hello on Business. The company further provided FIDO2 keys to all administrators and implemented a Conditional Entry authentication mechanism, mandating that all resellers perform phishing-resistant authentication. Here is the rewritten text:
The next logical step will be to introduce device-bound passkeys, which will be securely stored in the Microsoft Authenticator app, with Conditional Access utilizing them for seamless authentication. This feature could potentially eliminate the need for separate physical keys, allowing customers to leverage their familiarity with secure authentication on their mobile devices.
Azure Digital Desktop (formerly known as Windows Virtual Desktop) provides a range of supported identities and authentication strategies to ensure secure access to your virtual desktops and applications. The following are the supported identities and authentication strategies:
Single sign-on (SSO) with Azure Active Directory (AAD): This is the default authentication strategy, which leverages your existing AAD infrastructure to provide seamless SSO experiences for users.
Azure Active Directory (AAD) B2B collaboration: This feature enables organizations to securely collaborate with external partners or suppliers by granting them access to specific resources without sharing credentials.
Multi-Factor Authentication (MFA): Azure Digital Desktop supports MFA to add an extra layer of security, requiring users to provide a second form of verification in addition to their username and password.
RADIUS authentication: This protocol-based authentication method allows for integration with third-party RADIUS servers for added flexibility and customization.
LDAP authentication: Leveraging Lightweight Directory Access Protocol (LDAP), Azure Digital Desktop enables organizations to authenticate users against their existing on-premises directory services.
One-time passcode (OTP) authentication: Users can receive a one-time passcode via SMS, voice call, or authenticator app for added security when logging in.
SKIP
By providing customers with access to a range of functions and sources through Azure Digital Desktop, a major corporation can significantly reduce its overhead costs associated with maintaining and supporting individual units and the software operating on them. Additionally, they safeguard their atmosphere by protecting it from undoubtedly unhealthy, misconfigured, or stolen devices. Regardless of whether employees utilise Windows, macOS, iOS, or Android operating systems, they access the same digital desktop image and register, adhering to required protocols using phishing-resistant, passwordless authentication.
Configure Conditional Entry authentication capabilities to deliver robust, phishing-resistant access control for sensitive data and applications. Begin right here: .
Utilizing conditional entry insurance policies to facilitate access to restricted data.
By leveraging Conditional Entry, authorities clients have tailored access controls in place, taking into account a range of factors including user information, device specifications, geographic location, and real-time threat assessments, thereby determining which applications and resources users can access under specific conditions.
To meet the memo’s third criterion, these clients incorporate device-based notifications into their insurance policy authorizations. Microsoft Entra ID Safety can identify the security posture of a tool’s origin by assessing its geographic location, IP address range, and anonymity indicators such as Tor. Prior to granting access, Conditional Entry can leverage alerts from Microsoft Intune or other mobile device management methods to verify that a device is properly managed and compliant. It could also potentially consider integrating machine threat alerts from Microsoft Defender for Endpoint.
Microsoft has expanded its Entra product suite by introducing conditional entry risk-based insurance policies. This innovative feature empowers organizations to mitigate risks more effectively by leveraging machine learning algorithms and real-time data insights. With conditional entry, administrators can now define custom rules based on user behavior, location, device type, and other factors to automatically trigger insurance coverage for specific actions or events. For instance, a company might set up a policy that provides coverage when an employee uses a personal device for business purposes, ensuring they are protected in case of data breaches or equipment loss.
Authorities divisions have implemented risk-based Conditional Entry insurance policies across their operations, mandating enhanced security protocols tied to user and login threat assessments. Consumers assessed as “no-risk” should consistently implement multi-factor authentication, while those classified as “low-medium risk” must enroll using phishing-resistant multi-factor authentication; individuals considered “high-risk” should register with a unique certificate issued specifically to them by the relevant authority. The client has further specified that coverage should ensure compliance with unit requirements, permit tokenized security measures, and detail signin frequency parameters. To enhance threat detection and automated incident response, organizations send their sign-in and other relevant Microsoft 365 logs to Microsoft Sentinel for analysis.
Configure risk-based conditional entry insurance policies using Microsoft Intune. Begin right here: .
Subsequent steps
On July 10, 2024, the White House issued Memorandum M-21-14, titled “Implementing Executive Order on Improving Critical Infrastructure Security.” Within 120 days of the memo’s issuance, companies are required to furnish a comprehensive, up-to-date implementation plan to the Office of Administration and Finance. By September 30, 2026, companies within the Division of Protection are required to deploy Zero Trust security protocols, one year ahead of the previously announced deadline.
To support your digital transformation, Microsoft can assist in rearchitecting your environment to effectively deploy a Zero Trust approach, thereby enabling your organization to seamlessly adapt to each milestone of the Government Order. We’ve published guidelines and tutorials to help federal businesses utilize Microsoft Entra ID to meet their identification requirements. We have also printed and met all Division of Defense Zero Trust requirements utilizing Microsoft Entra ID.
In the coming weeks and months, you can expect updates on our efforts to streamline your Zero Trust implementation, building upon recent milestones such as the final release of Microsoft Authenticator features and enhancements that enable multifactor authentication by default for US government clients.
As we move forward together, we’re committed to empowering your ongoing Zero Trust initiatives.
- Utilize Microsoft Entra ID as a centralized identity provider to securely manage identities and safeguard access to your applications and resources. Begin right here:
- To ensure seamless interorganizational collaboration, configure cross-tenant entry settings and conditional entry policies to mandate the use of phishing-resistant authentication for all users accessing shared resources upon sign-up. Begin right here: .
- To seamlessly integrate Cloud-Based Authentication (CBA) with Active Directory Federation Services (AD FS), consider migrating to a cloud-based CBA solution using a staged rollout approach, thereby phasing out reliance on on-premises federation servers. Begin right here: .
- Eliminate passwords entirely by empowering secure, phishing-resistant login experiences through the adoption of Certificate-Based Authentication (CBA), Windows Hello for Business, device-bound passkeys (such as FIDO2 security keys or those managed in the Microsoft Authenticator app), and Platform Single Sign-On for macOS. Begin right here: .
- Can governments implement risk-based conditional entry insurance policies that adjust entry requirements in real-time based on evolving pandemic conditions? Begin right here: .
To stay ahead of the curve in Microsoft’s cutting-edge security features, visit our website and bookmark the page dedicated to keeping you informed about the latest developments in cybersecurity. Follow us on LinkedIn () and X () for the latest insights and updates on cybersecurity.

