
Microsoft and the Justice Department have jointly seized more than 240 domains used by customers of ONNX, a phishing-as-a-service platform that has targeted businesses and individuals across America and globally since at least 2017.
According to records, ONNX, previously referred to as Caffeine, emerged as the top Adversary in the Middle (AitM) phishing service in terms of the volume of phishing messages during the first half of 2024. Each month, Microsoft 365 faces an onslaught of tens of millions of phishing emails targeting its customers, as well as those of various other tech companies.
Microsoft reports that “do-it-yourself” kits account for a substantial portion, estimated in the tens to hundreds of millions, of phishing messages it detects each month, with the fraudulent ONNX operation ranking as one of the top five providers during the first half of 2024.
The fraudulent ONNX operation reportedly distributed sophisticated phishing kits, targeting numerous organizations across various sectors, including tech giants like Google, Dropbox, Rackspace, and Microsoft.
The ONNX platform advertised and acquired phishing kits available on Telegram via various subscription tiers (Basic, Professional, and Enterprise) priced between $150 and $550 per month.
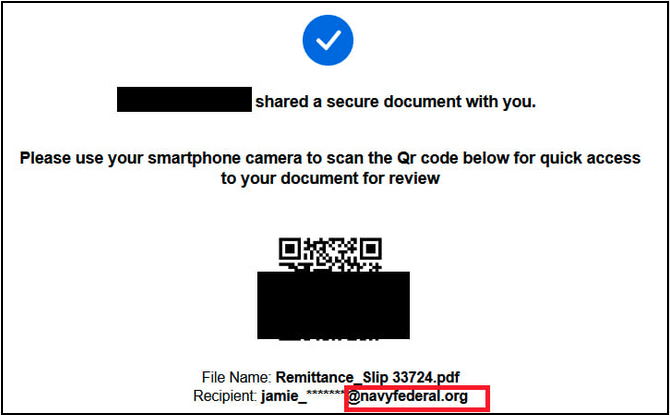
The cyberattacks, enabled by Telegram bots and featuring integrated mechanisms to circumvent two-factor authentication, targeted financial institution employees, credit union representatives, and private investment professionals using QR code-based phishing tactics.
The emails contained PDF attachments featuring malicious QR codes that masqueraded as authentic Microsoft 365 login pages, attempting to deceive recipients into providing their login credentials?
“Threat actors exploit vulnerabilities in victims’ personal mobile devices by tricking them into scanning QR codes on their own phones, which may also be used for business purposes through Bring Your Own Device (BYOD) programs.” The Financial Industry Regulatory Authority (FINRA) also cautioned that. As a result, attacks of this nature are notoriously challenging for standard endpoint detection tools.
Cybercriminals leveraging Open Neural Network Exchange (ONNX) have demonstrated remarkable efficacy in completing attacks, as phishing kits enable them to circumvent two-factor authentication (2FA) by intercepting and manipulating 2FA requests.
They employ bulletproof internet hosting companies, which deliberately slow down the takedown process for suspected phishing domains, as well as utilizing encrypted JavaScript code that self-decrypts during page load, incorporating an extra layer of obfuscation to evade detection by anti-phishing scanners.
“These unprecedented attacks pose a novel challenge for cybersecurity providers, rendering them an imperceptible threat to traditional security and scanning tools,” said Steven Masada, Assistant General Counsel at Microsoft’s Digital Crimes Unit.
ONNX operations unexpectedly ceased in June following the disclosure of its owner’s identity, Abanoub Nady, by Darkish Atlas security researchers under his online alias MRxC0DER.
Through a recent court order unsealed in the Eastern District of Virginia, this motion redirects malicious technical infrastructure to Microsoft, effectively severing access for threat actors, including the fraudulent ONNX operation and its cybercrime clients, thereby completely halting their use of these domains in future phishing attacks.
Our goal in every situation is to protect our clients by cutting off malicious actors from the resources they need to operate, thereby significantly increasing the barriers to entry and the cost of conducting illicit activities.
We are pleased to have Co-Plaintiff LF (Linux Foundation) Tasks, LLC, the trademark owner and proprietor of the registered ‘ONNX’ mark and logo.
In October, Microsoft collaborated with the Department of Justice to seize more than 100 domains used in spear-phishing attacks against US interests. Authorities’ staff and Russian non-profit organizations.
In late December, Microsoft’s Digital Crimes Unit detected a massive scheme, code-named Storm-1152, which created over 750 million fake email addresses and generated tens of millions of dollars by selling these compromised credentials to other cybercriminals.

