Cybercriminals lure content material creators with guarantees of cutting-edge AI wizardry, solely to try to steal their information or hijack their gadgets as a substitute
17 Apr 2025
•
,
3 min. learn

The craze round generative AI instruments isn’t simply reshaping industries – it additionally gives fertile floor for cybercriminals, who’re all the time fast to piggyback on the attract of the most recent large factor in tech. So what if, as a substitute of downloading an AI‑generated video from CapCut or one other related device, you had your information stolen or gave management of your pc to a stranger?
The risk isn’t hypothetical – safety researchers have beforehand noticed campaigns that exploited CapCut’s recognition to distribute a number of infostealers and different malware. Let’s now look briefly at one other marketing campaign that’s concentrating on folks concerned about AI-powered content material by promising premium variations of standard software program akin to CapCut, Adobe Specific and Canva.
The artwork of the lure
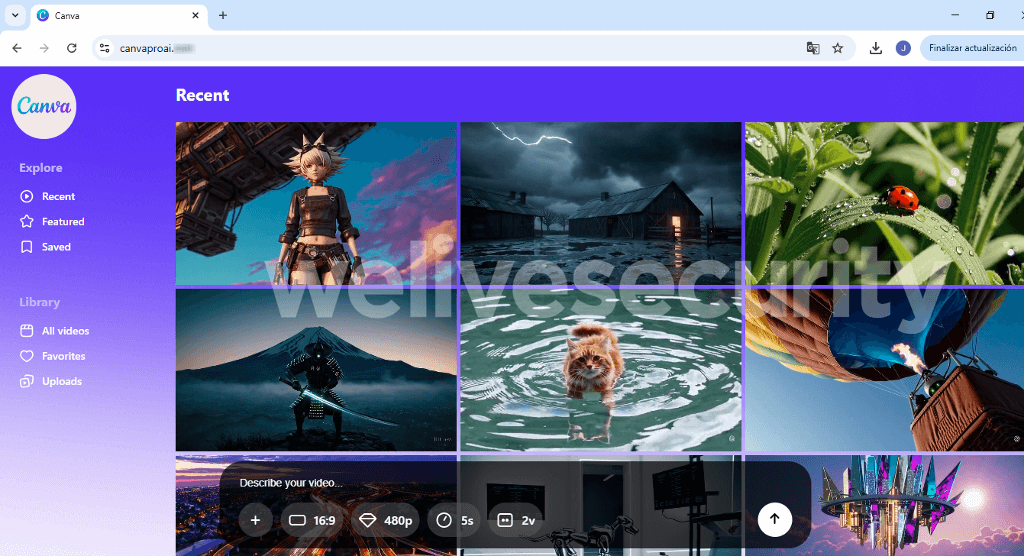
The instance beneath, noticed by X person g0njxa, reveals a web site that impersonates CapCut, a device usually utilized by TikTok creators, and purports to be CapCut’s premium model. (Be aware that the precise premium model is named “CapCut Professional” or referred to easily as “Professional” on the web site, not “CapCutProAI” as within the screenshot.)
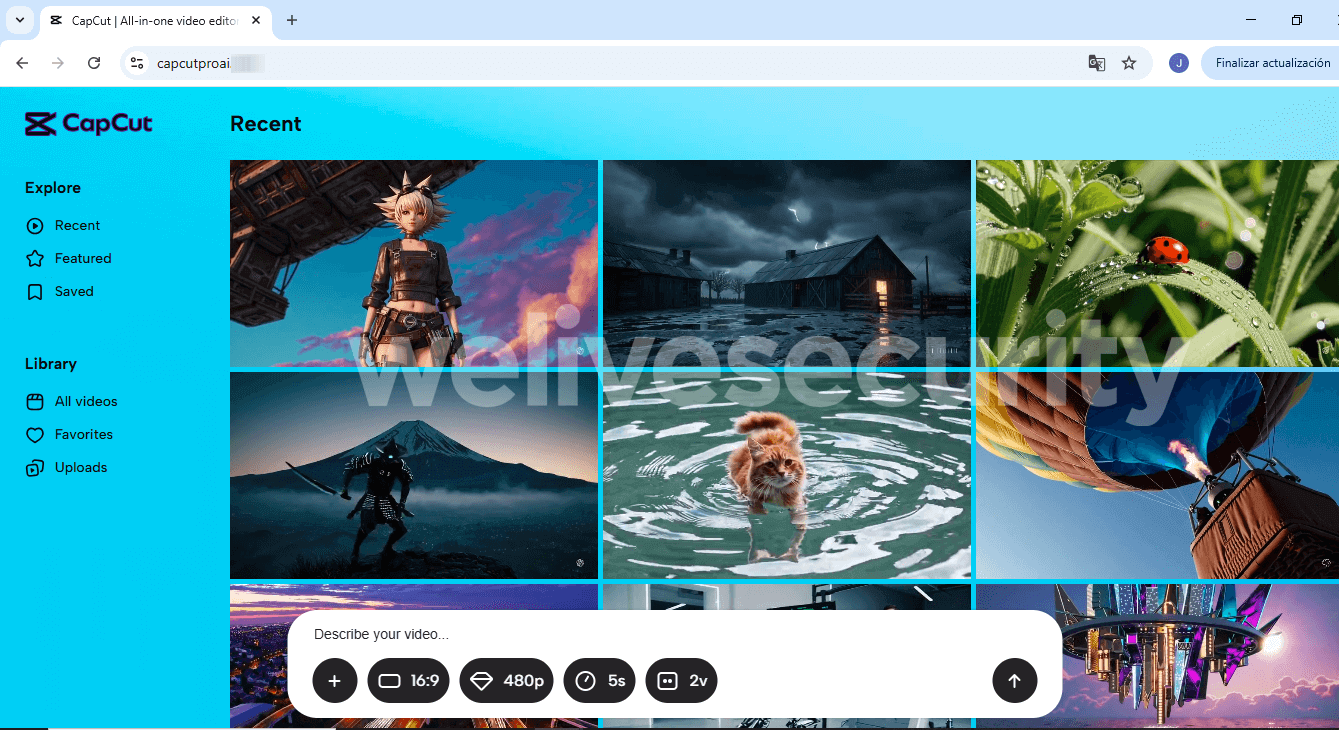
After you land on the faux website, you’re requested to enter a immediate or add a reference file. When you comply, the location will mimic processing the request.
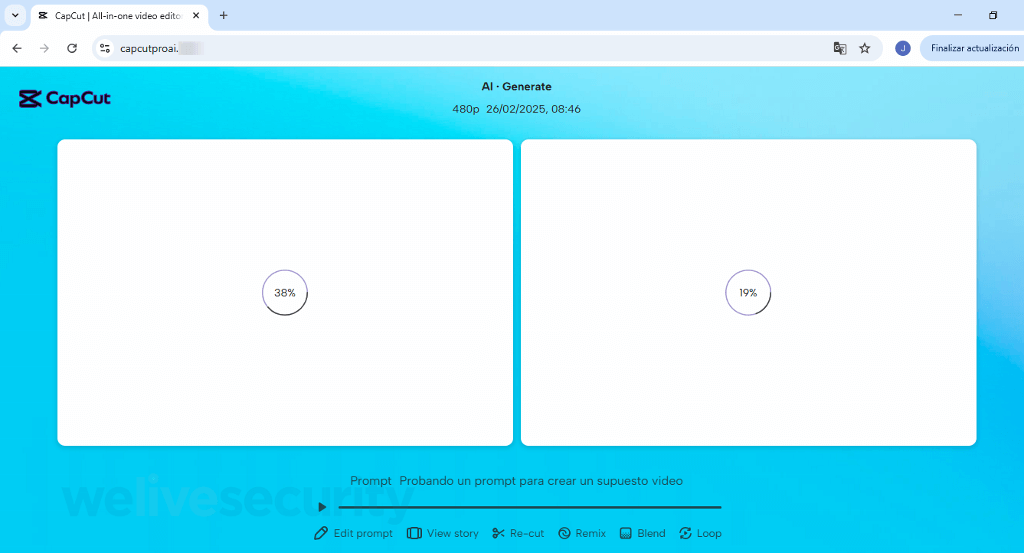
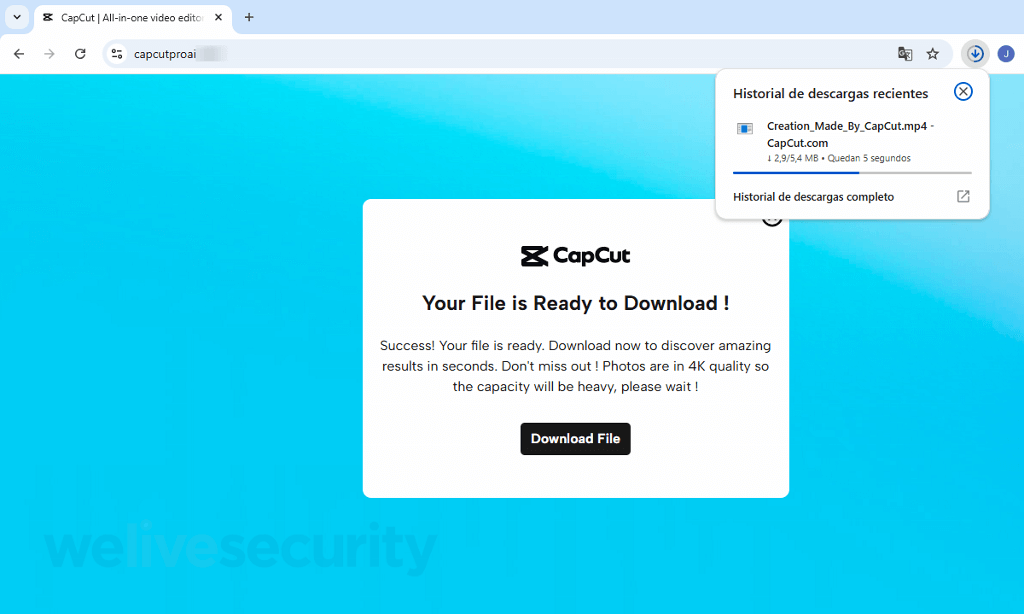
As soon as the anticipation is constructed and the entice is sprung, you’re prompted to obtain your shiny new “creation”. Needles to say, the file, referred to as Creation_Made_By_CapCut.mp4 – CapCut.com, is much from what it purports to be. In actuality, it’s an executable for distant entry software program. Quick ahead a number of clicks and, except different safeguards kick in, you could be surrendering management of your system to crooks.
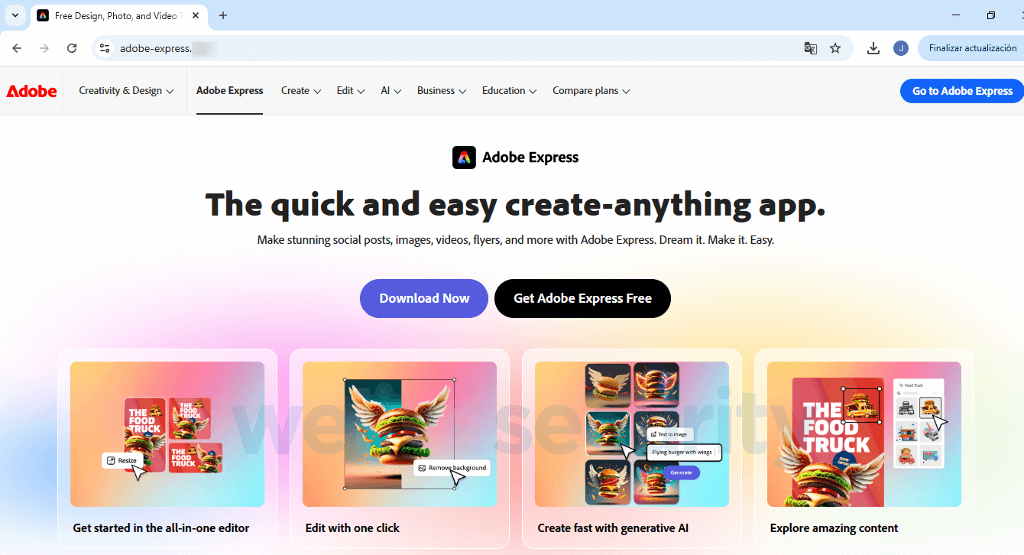
Listed here are two extra websites that masquerade as the actual deal and are a part of the identical marketing campaign:
Faraway, so shut
For context, whereas respectable distant entry instruments, akin to ConnectWise ScreenConnect, TeamViewer and AnyDesk, are invaluable for IT professionals offering technical help, within the mistaken arms they are often misused to take over management of your pc for malicious ends. These embrace information theft, set up of ransomware or different malware, and utilizing the compromised machine as a launch pad for assaults at different gadgets.
These sorts of threats additionally loom giant on company networks, as risk actors can, for instance, distribute moveable, self-contained executables for respectable distant monitoring and administration (RMM) software program that circumvents admin privileges and obviates the necessity for full software program set up.
“Most distant management purposes include the choice to generate a preconfigured executable to connect with a particular IP tackle or person. That is helpful for distant help, but in addition for attackers. The sufferer merely has to open the file, and in a few clicks, they could unwittingly give management of their pc to a cybercriminal,” says Martina López, a safety researcher with ESET’s lab in Latin America.
Phrase to the smart
A few easy steps will go a good distance towards conserving you secure:
- When downloading new software program, be certain to get it from the respectable supply, usually the writer’s official web site
- Keep away from clicking on unsolicited hyperlinks in e-mail or social media messages that always declare to result in such web sites – the messages could also be faux
- The identical goes for adverts – you’re higher off navigating to the web site immediately by typing it in your browser or looking for it (with a essential eye, although) in your search engine of selection
- Examine the web site’s URL – software program makers don’t usually sport numerous oddball extensions in URLs or sneaky “alternate” variations (assume “CapCutProAI”)
- Ensure your working system, browser, and different software program are updated to guard towards identified vulnerabilities
- Use multi-layered safety software program, in addition to follow different fundamental cybersecurity hygiene practices, akin to robust and distinctive passwords and enabling two-factor authentication on all of your on-line accounts
Evidently, that is neither the primary nor final time CapCut customers have been focused by cybercriminals, and these examples simply present that cybercriminals are all the time keen to use belief and the most recent large factor in tech.
The excellent news is that that whereas these ploys are sometimes slick, they’re not invincible. Your vigilance is your finest protect towards scammers’ ways.



