This publish demonstrates find out how to construct a safe search software utilizing Amazon OpenSearch Service and JSON Net Tokens (JWTs). We talk about the fundamentals of OpenSearch Service and JWTs and find out how to implement person authentication and authorization by an current identification supplier (IdP). The main focus is on implementing fine-grained entry management based mostly on person roles and permissions.
JWT authentication and authorization to your OpenSearch Service area gives a sturdy mechanism that addresses necessities for fine-grained entry management. An IdP is a service that shops and manages person identities and their entry rights, enabling centralized person authentication throughout a number of functions. The IdP points JWTs, that are safe tokens containing claims concerning the authenticated person. Through the use of JWTs from the IdP, you possibly can:
- Implement safe, role-based entry management to look outcomes
- Validate person permissions earlier than granting entry to delicate knowledge
- Preserve a centralized authentication mechanism throughout your search software
- Make certain solely approved customers can view knowledge based mostly on their predefined roles
The JWT integration helps organizations:
- Outline granular permissions throughout the IdP
- Authenticate customers utilizing bearer tokens throughout completely different functions
- Shield delicate data by token-based entry administration
- Cut back complexity of managing a number of authentication methods
Key advantages of the answer embrace:
- Standardized token-based authentication
- Centralized permission administration
- Simplified single sign-on (SSO) expertise
- Versatile and scalable entry management mechanism
The flexibility to dynamically filter delicate data based mostly on token claims enhances knowledge safety whereas lowering the complexity of managing a number of authentication methods. This functionality is made potential by the fine-grained entry management (FGAC) function in OpenSearch Service, which enforces document- and field-level entry based mostly on person roles.
Use case overview
On this publish, we discover a person workflow with a number of roles and entry stage necessities. A analysis establishment needs to construct a safe search software with managed entry to biomedical databases particularly PubMed (a complete database of biomedical literature) and Scientific Trials (a registry of medical analysis research). Completely different analysis groups require various ranges of entry to those datasets based mostly on their roles and clearance ranges. The next hierarchical entry construction defines the person roles and their corresponding permission ranges for accessing PubMed and Scientific Trials databases:
- PubMed Admin – Full learn entry to all PubMed knowledge (for senior analysis teams)
- PubMed Restricted – Restricted entry to particular fields and paperwork (for researchers with restricted entry)
- Scientific Trials Admin – Full learn entry to all Scientific Trials knowledge (for principal investigators and senior trial managers)
- Scientific Trials Restricted – Restricted learn entry to particular trial data and aggregated knowledge (for trial researchers with restricted entry)
- Analysis Primary – Learn-only entry to particular public knowledge in PubMed and Scientific Trials (for normal analysis workers and interns)
- Analysis Full Entry – Full learn and write entry to all indices, with permissions to replace or modify knowledge
To implement this use case, we use JWTs generated by the supported IdP, which encode role-specific data. This setup makes certain OpenSearch Service can validate tokens earlier than returning search outcomes, dynamically filtering delicate knowledge based mostly on the person’s JWT claims and fine-grained entry management settings.
Answer overview
The technical workflow for utilizing JWT authorization with OpenSearch Service includes a number of key levels:
- Person authentication – Customers log in by the prevailing authentication system linked to the IdP
- JWT technology – Upon profitable authentication, the IdP generates a JWT containing particular function data
- Search question submission – Customers submit search queries to OpenSearch Service together with their JWT
- Token validation – OpenSearch Service validates and decodes the JWT to confirm person permissions
- Outcome filtering – Search outcomes are filtered based mostly on the person’s permissions outlined within the JWT
- Information retrieval – Solely approved knowledge is returned to the person, implementing compliance with privateness requirements
This workflow gives a standardized method to authentication and authorization whereas streamlining person interactions with the search software. The answer makes certain every person sees solely the data acceptable to their function, sustaining knowledge privateness and organizational safety requirements.
You will need to allow JWT authentication and authorization, and fine-grained entry management in the course of the OpenSearch Service area creation course of. For extra data, check with Configuring JWT authentication and authorization and Wonderful-grained entry management in Amazon OpenSearch Service.
The next diagram illustrates the answer structure.
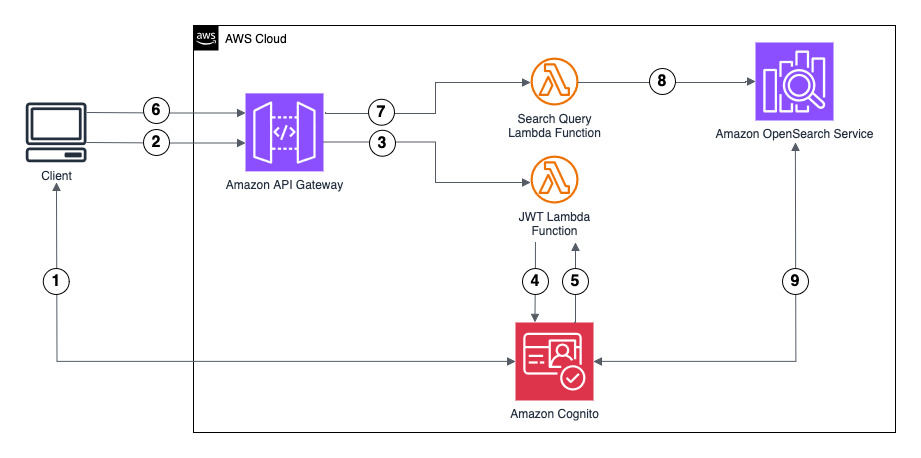
This resolution demonstrates authentication utilizing Amazon Cognito because the IdP to generate the JWT. Nevertheless, you should utilize one other supported IdP. The ID token consists of group membership data that OpenSearch Service maps to roles configured utilizing fine-grained entry management.
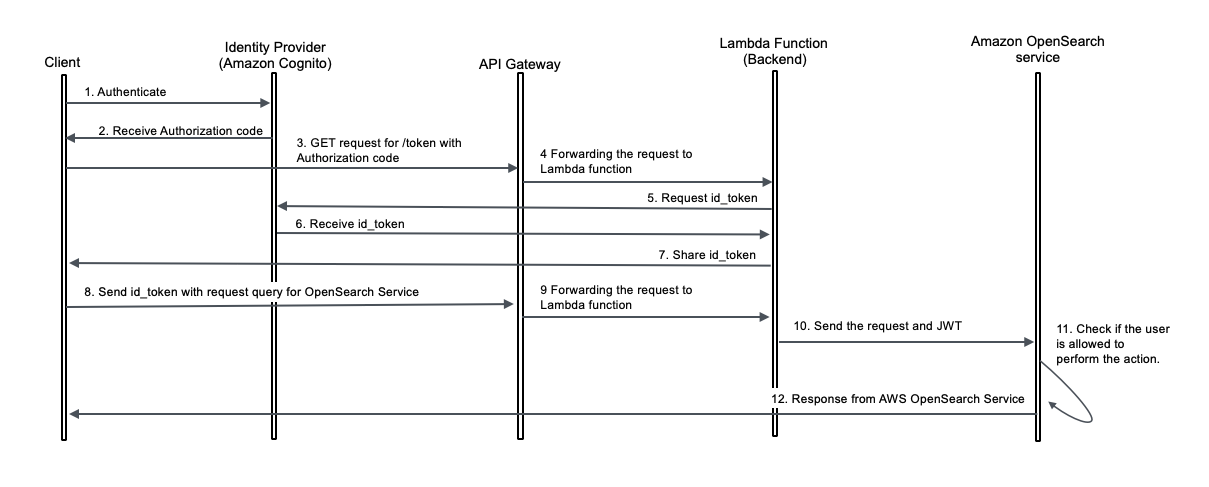
The person move consists of the next steps:
- The consumer initiates authentication by logging in with Amazon Cognito person credentials. Amazon Cognito returns an authorization code.
- The consumer sends the authorization code to an Amazon API Gateway /token endpoint for ID token trade.
- API Gateway forwards the authorization code to an AWS Lambda perform.
- The Lambda perform sends a token trade request to Amazon Cognito with the authorization code.
- The Lambda perform receives the ID token from Amazon Cognito and returns it to the consumer.
- The consumer sends an OpenSearch Service question to the API Gateway /search endpoint, together with the ID token. API Gateway validates the ID token (JWT) with Amazon Cognito.
- API Gateway forwards the request to a Lambda perform.
- The Lambda perform checks if JWT authentication and authorization is enabled for the OpenSearch Service area with the respective public key of the Amazon Cognito person pool. If not, it should allow and configure this function for the OpenSearch Service area. The Lambda perform forwards the question and ID token to OpenSearch Service.
- OpenSearch Service validates the JWT with Amazon Cognito:
- OpenSearch Service verifies person permissions in opposition to fine-grained entry management based mostly on group membership.
- OpenSearch Service returns question outcomes to the consumer if authorization succeeds.
The next diagram illustrates the request move.
Conditions
Earlier than you deploy the answer, ensure you have the next stipulations:
Deploy resolution sources
To deploy the answer sources, we use an AWS CloudFormation template. Launch the AWS CloudFormation template with the next Launch Stack button.
Enter an acceptable stack title. This title is used as a prefix for sources like OpenSearch Service domains and Lambda capabilities. Preserve the default settings, and select Create.
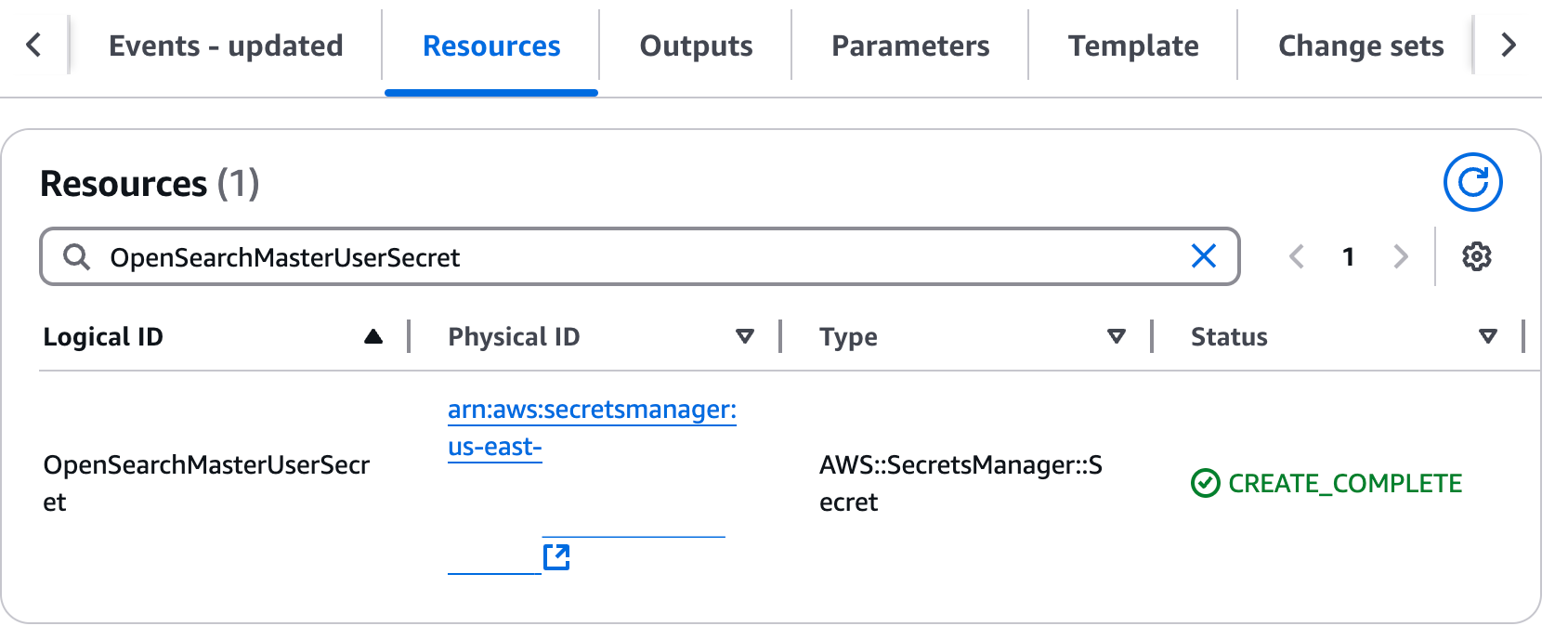
The stack deployment takes roughly 15–20 minutes. When deployment is full, the stack standing reveals as CREATE_COMPLETE.
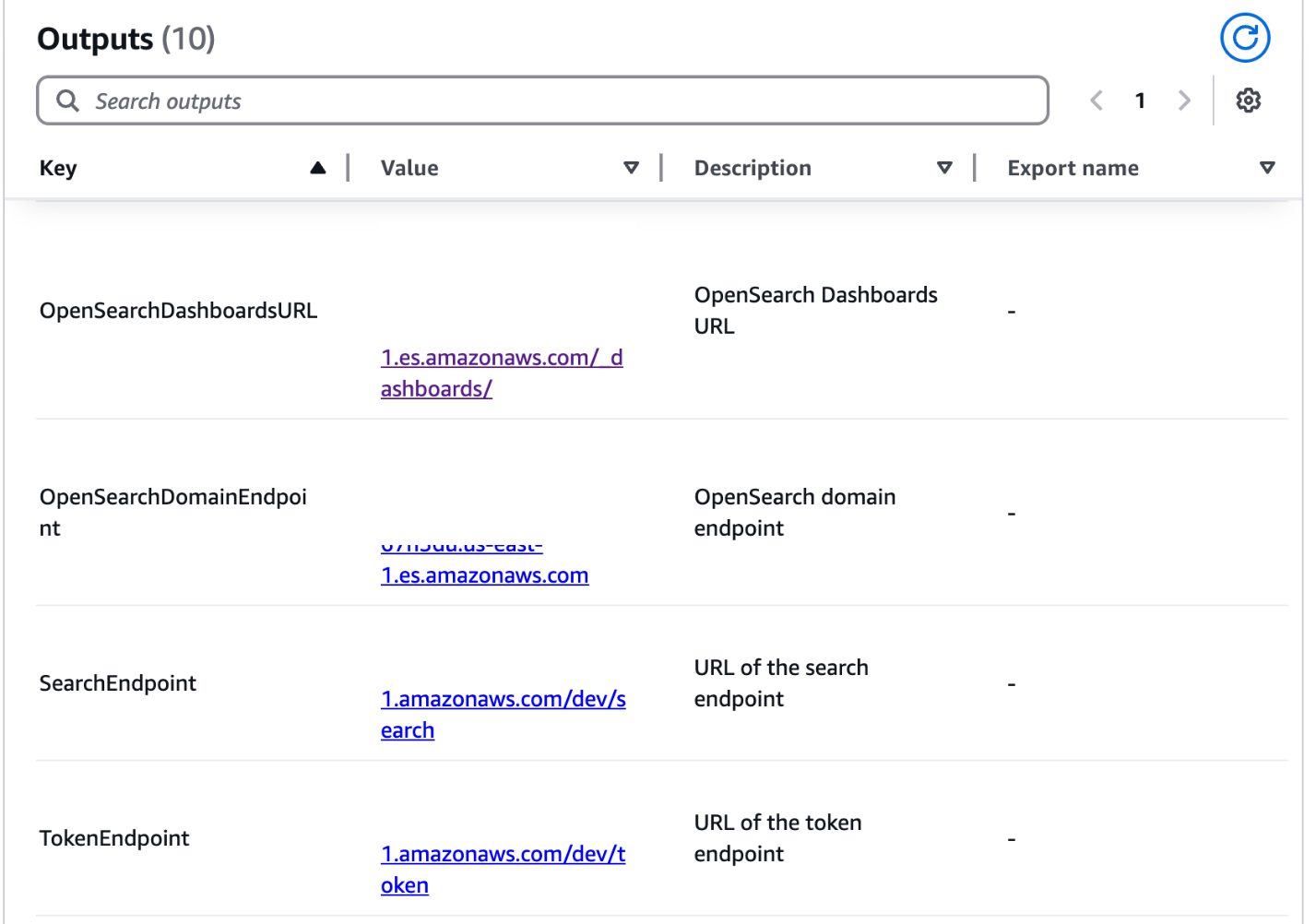
The outputs for this CloudFormation stack present essential data concerning the deployed sources. This data might be referenced all through completely different sections of this publish.
On the Outputs tab, notice the next values:
- OpenSearchDashboardURL
- SharedLambdaRoleArn
On the Sources tab, find the next data:
- OpenSearchMasterUserSecret: Select the Bodily ID hyperlink, then select Retrieve Secret Worth. Be aware the person title and password required for OpenSearch Service area login.
- IngestDataAndCreateBackendRoles: Select the Bodily ID hyperlink to open the Lambda perform, wanted in later steps.
- UserPool: Select the Bodily ID hyperlink to open the Amazon Cognito person pool, wanted in later steps.
- RestAPI: Select the Bodily ID hyperlink to open the API Gateway endpoint, wanted in later sections.
In a separate browser tab, log in to the OpenSearch dashboard utilizing OpenSearchDashboardsURL and person credentials famous beforehand.
Assign permissions to the IAM function related to the Lambda perform
Full the next steps to map your IAM function to each the all_access and security_manager roles in OpenSearch Service:
- In OpenSearch Dashboards, select Safety within the navigation pane, then select Roles.
- Open the all_access function.
- Within the Mapped customers part, select Handle mapping.
- For Backend function, enter the IAM function Amazon Useful resource title (ARN). That is the worth you copied from the CloudFormation stack output for
SharedLambdaRoleArn. - Select Map to substantiate.
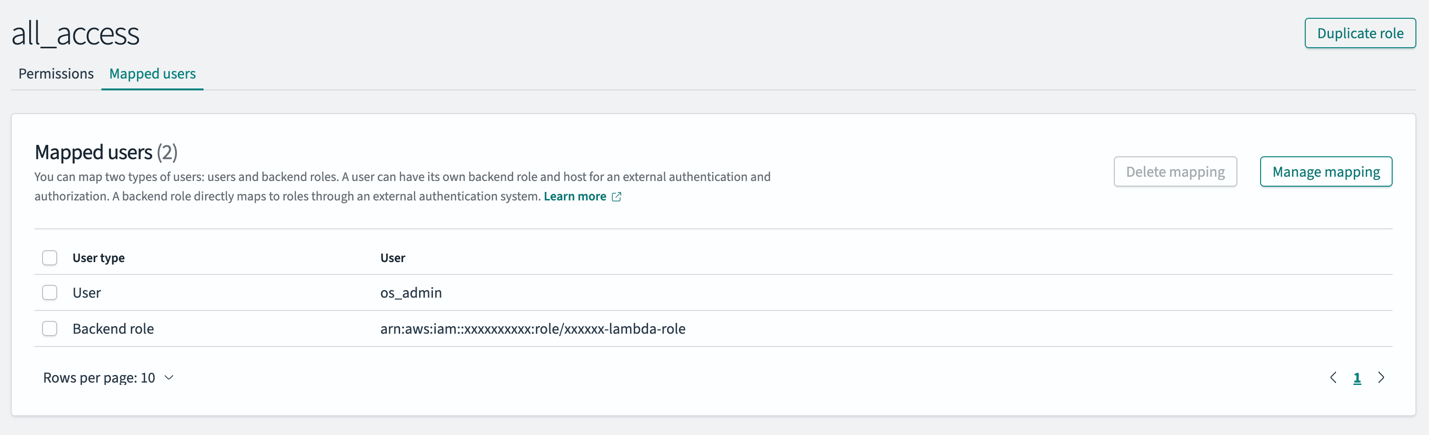
- On the Roles web page, open the security_manager function.
- Within the Mapped customers part, select Handle mapping.
- For Backend function, enter the identical IAM function ARN.
- Select Map to substantiate the modifications.
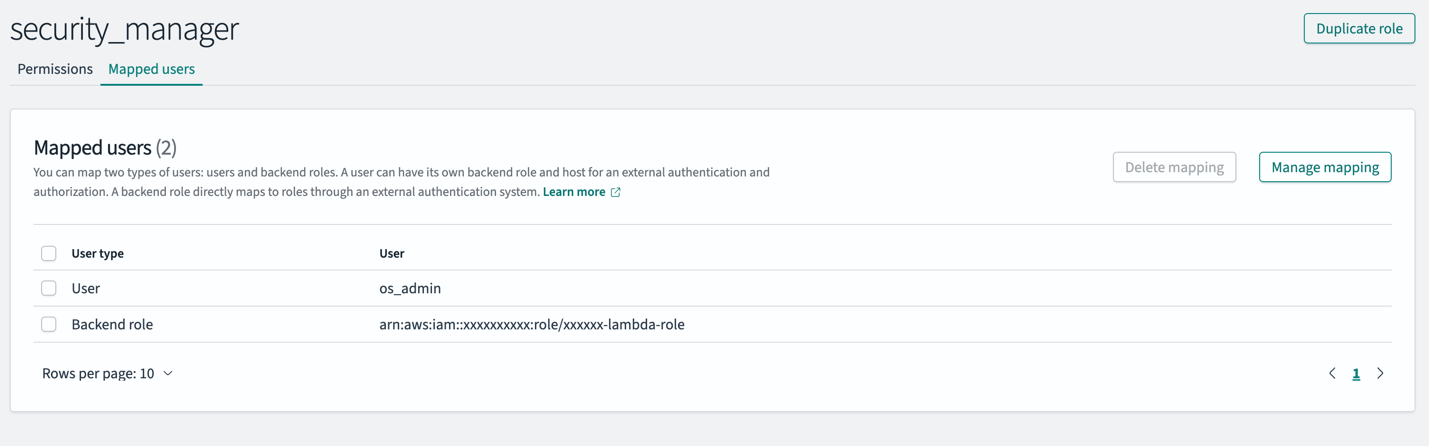
These steps make sure the IAM function connected to the Lambda perform has the mandatory permissions to ingest knowledge (all_access) and create roles (security_manager) throughout the OpenSearch Service area.
On this pattern setup, the Lambda perform handles bulk ingestion and function creation with out granting any direct entry to customers, and all_access is supplied to the Lambda function solely to allow ingestion. FGAC in OpenSearch gives in-depth entry management, permitting you to additional tighten the Lambda function permissions by granting solely the mandatory CRUD operations, slightly than full entry for ingestion. For extra particulars, check with Defining customers and roles and Wonderful-grained entry management in OpenSearch.
Run the Lambda perform to ingest knowledge into the OpenSearch Service area
On the CloudFormation stack’s Sources tab, find the IngestDataAndCreateBackendRoles Lambda perform. Open the Lambda perform, select Take a look at, and execute it. You may verify the perform’s profitable execution by checking Amazon CloudWatch Logs.
This Lambda perform is designed to carry out bulk ingestion and function creation within the OpenSearch Service area. It ingests pattern medical analysis knowledge into OpenSearch Service, creating two indexes (pubmed and clinical_trials), and units up required OpenSearch Service roles. We discover these roles intimately within the subsequent part.
Map roles and customers in OpenSearch Service
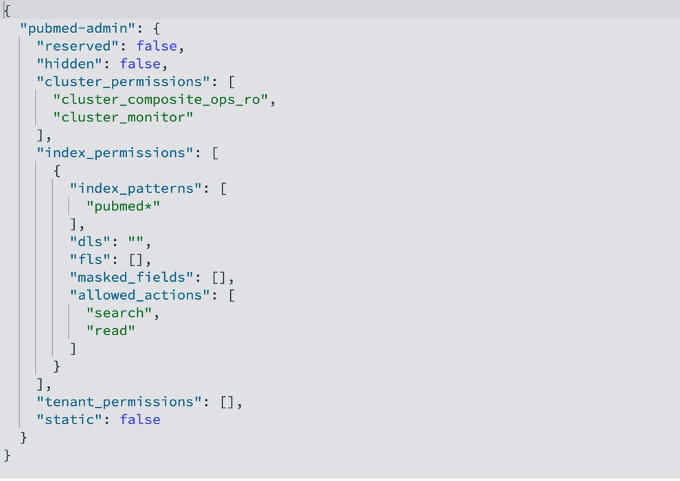
On this step, we outline two key OpenSearch Service roles:
- pubmed-admin – Grants full learn entry to the PubMed index containing biomedical literature and analysis abstracts, meant for senior analysis teams
- pubmed-limited – Offers restricted learn entry to solely particular fields (journal, title, and summary, the place journal is a masked subject), meant for researchers with restricted knowledge entry
We have now already created these roles by working the Lambda perform within the earlier part. The next code is the pubmed-admin OpenSearch Service function description:
The next code is the pubmed-limited OpenSearch Service function description:

The pubmed-admin and pubmed-limited roles serve completely different functions, and their primary distinction lies in how they management knowledge visibility. Doc-level safety (DLS) allows you to prohibit a job to a subset of paperwork in an index, whereas field-level safety (FLS) allows you to management which doc fields a person can see. The restricted function is configured with FLS to show solely the journal, title, and summary fields, whereas masked fields anonymize delicate knowledge comparable to journal. On high of those, you possibly can apply DLS to cover particular data, for instance, to forestall customers from viewing paperwork from sure journals or publication years. In your use circumstances, use DLS and FLS to manage doc and subject visibility for various customers. These roles are totally configurable; you possibly can add, take away, or replace doc and subject entry at any time to match evolving safety or enterprise necessities.
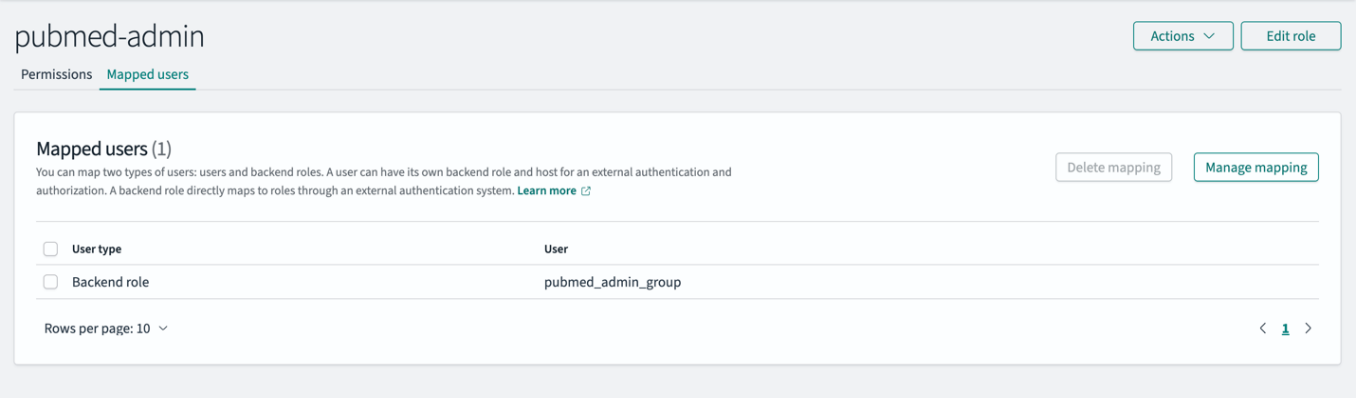
To implement entry management, customers must be mapped to acceptable OpenSearch Service roles on OpenSearch Dashboards. Full the next steps to map customers to the OpenSearch Service roles:
- On OpenSearch Dashboards, select Safety within the navigation pane, then select Roles.
- Open the
pubmed-adminfunction. - Within the Mapped customers part, select Handle mapping.
- For Backend function, enter
pubmed_admin_group. - Select Map to substantiate the mapping.
- On the Roles web page, open the pubmed-limited function.
- Within the Mapped customers part, select Handle mapping.
- For Backend function, enter pubmed_limited_group.
- Select Map to substantiate the mapping.
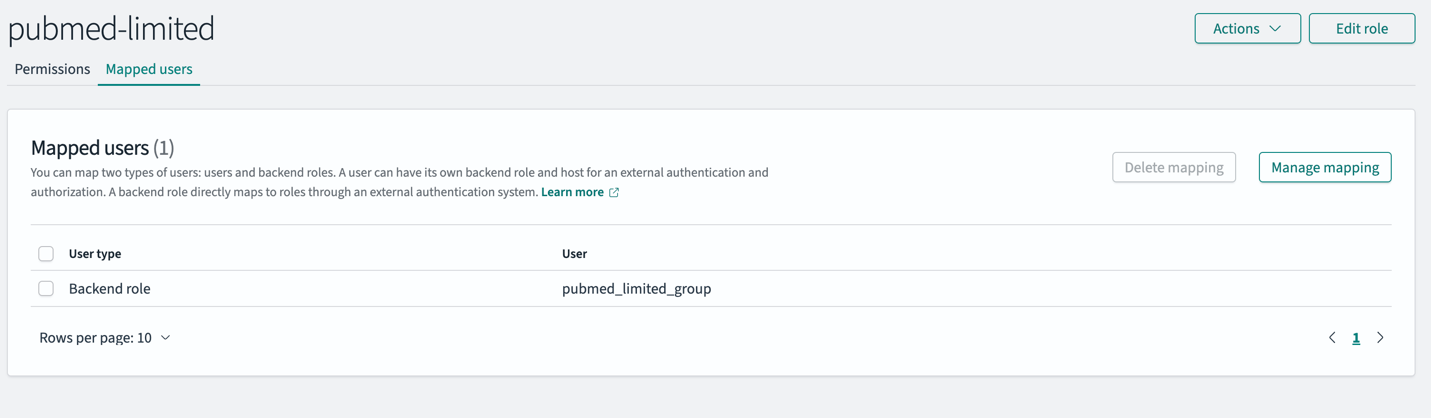
Backend roles simplify entry administration in OpenSearch Service. As a substitute of mapping particular person customers to OpenSearch service roles, you possibly can map roles to backend roles that customers share. This method allows you to map IdP teams on to the OpenSearch service roles. OpenSearch Service gives choices when configuring your OpenSearch Service area to map JWT claims to OpenSearch Service roles utilizing the roles key.
On this resolution, the JWT accommodates a subject referred to as cognito:teams that might be mapped because the roles key. In each JWT, this subject has a price for the suitable group the person belongs to. Primarily based on the sector worth within the JWT and the mapping outlined within the earlier step for various analysis teams, OpenSearch Service area dynamically assigns permissions:
- If the JWT accommodates “cognito:teams”: [“pubmed_admin_group”], the person is granted pubmed_admin entry
- If the JWT accommodates “cognito:teams”: [“pubmed_limited_group”], the person is granted pubmed_limited entry
Check out the examples beneath to know what a JWT header and payload seem like.
Pattern JWT header:
Pattern JWT payload:
Create customers in Amazon Cognito
On this part, we create the next Amazon Cognito customers:
The e-mail tackle required for every person needs to be distinctive. In case your e mail area helps e mail alias, you possibly can add a suffix to your personal e mail tackle by utilizing +pubmedadminuser@area.com. The next screenshot reveals our customers.
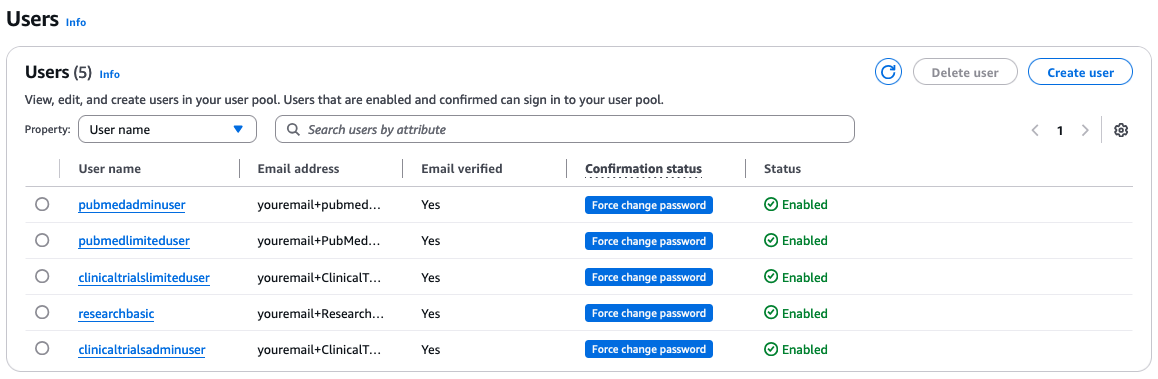
On the CloudFormation stack’s Sources tab, find the UserPool Amazon Cognito person pool that you simply famous earlier. Open the person pool in a brand new browser tab.
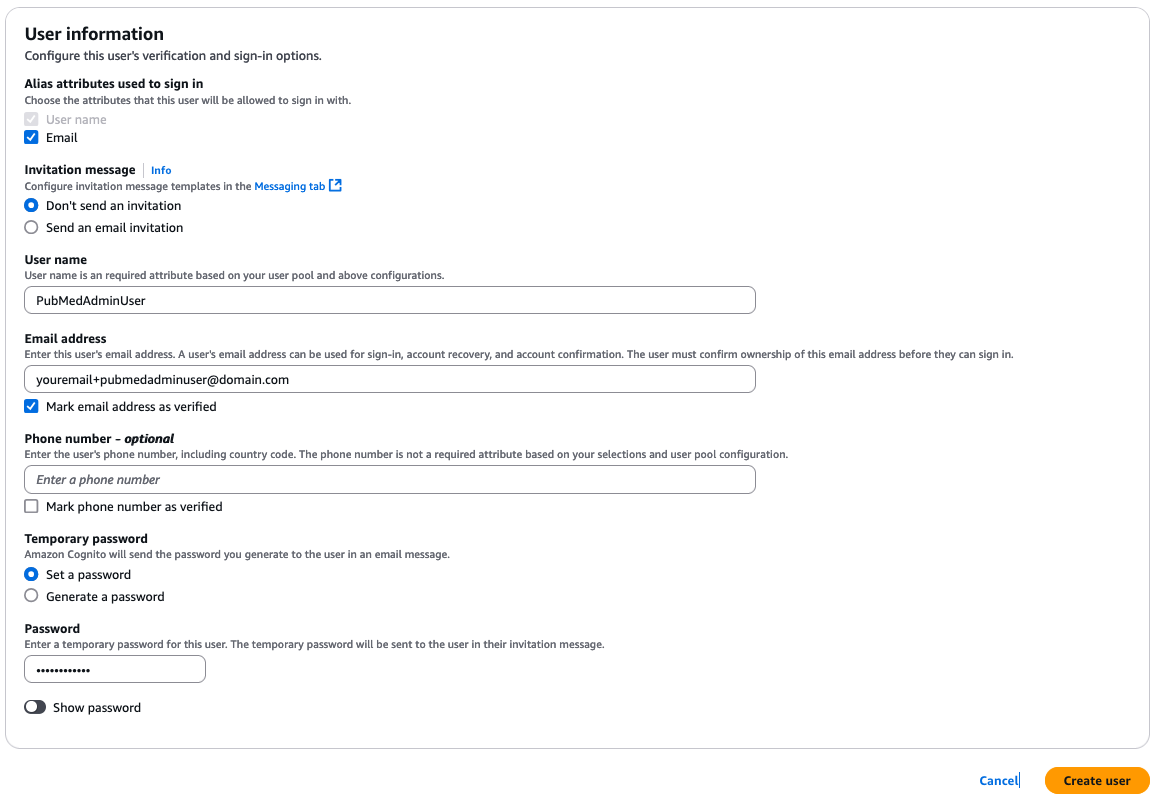
To create the Amazon Cognito customers, full the next steps for every person:
- On the Amazon Cognito console, select Customers within the navigation pane.
- Select Create person.
- For Alias attributes used to register, choose E-mail.
- For Person title, enter a singular person title.
- For E-mail tackle, enter a singular e mail tackle for every person.
- Choose Mark e mail tackle as verified.
- Select Create Person.
Create teams in Amazon Cognito
We create the next teams in Amazon Cognito:
The next screenshot reveals created teams.
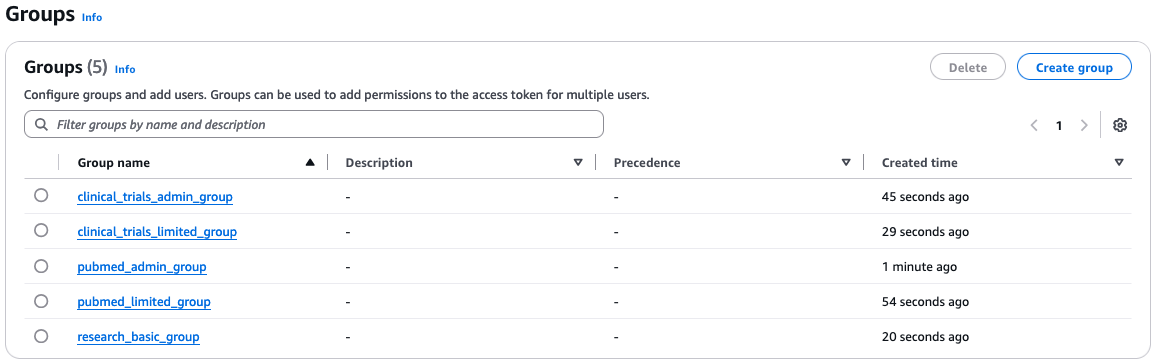
To create the Amazon Cognito teams, full the next steps for every group:
- On the Amazon Cognito console, select Teams within the navigation pane.
- Select Create group.
- For Group title, enter a singular title.
- Select Create group.
Add Amazon Cognito customers to teams
The customers needs to be added to the teams as follows:
- Add
PubMedAdminUserto thepubmed_admin_groupgroup - Add
PubMedLimitedUserto thepubmed_limited_groupgroup - Add
ClinicalTrialsAdminUserto theclinical_trials_admin_groupgroup - Add
ClinicalTrialsLimitedUserto theclinical_trials_limited_groupgroup - Add
ResearchBasicUserto theresearch_basic_groupgroup
So as to add customers to their respective group, full the next steps for every group:
- On the Amazon Cognito console, select Teams within the navigation pane.
- Select the group to which you wish to add a person.
- Select Add person to group.
- Select the person and select Add.
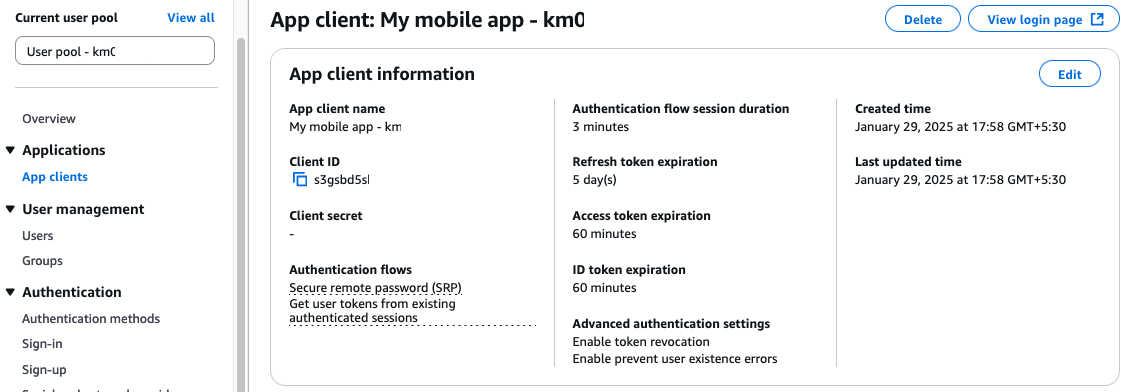
Log in to generate a JWT
Earlier than working the check queries within the subsequent part, you could receive the id_token (JWT) for the desired customers. The tokens will expire in 60 minutes. If the token is expired for a person, you could log in once more to get a recent token. To log in together with your person to get the id_token, full the next steps:
- On the Amazon Cognito console, open your person pool.
- Select App shoppers within the navigation pane.
- Select the app consumer.
- Select View login web page.
- Enter the person title that you simply used when creating the person.
- Enter the non permanent password that you simply set when creating the person.
- For first-time logins, you’ll be prompted to create a brand new password. Enter a brand new password that meets the next necessities:
- No less than 8 characters
- Incorporates uppercase and lowercase letters
- Incorporates a minimum of one quantity
- Incorporates a minimum of one particular character
- Copy the id_token worth you generated (with out citation marks).
Question knowledge in OpenSearch Service
This instance demonstrates how OpenSearch Service filters search outcomes based mostly on person permissions. We check searches utilizing JWTs for 2 completely different customers to confirm entry controls. Every person’s search outcomes are restricted to the indexes and paperwork allowed by their assigned roles.
On the CloudFormation stack’s Sources tab, find the RestAPI worth that you simply famous earlier. Open the API gateway in a brand new browser tab.
Full the next steps to check the search API for every of the eventualities talked about on this part:
- On the API Gateway console, select Sources within the navigation pane.
- Select the /search useful resource.
- Select the POST methodology.
- Select Take a look at.
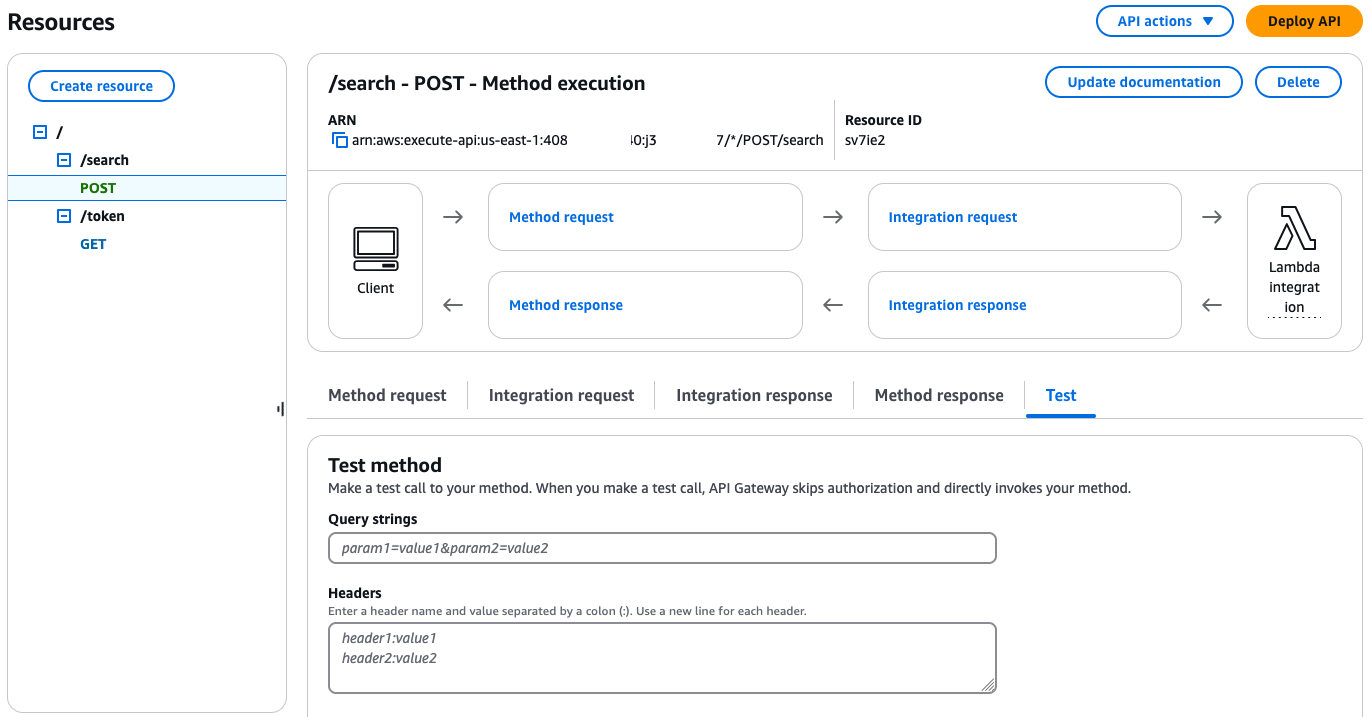
When submitting queries to OpenSearch Service, make sure that all double citation marks are escaped to forestall syntax errors. Moreover, ensure you full your question earlier than your JWT expires, or you will have to generate a brand new token. In the event you try to make use of an expired token, it should lead to an error.
For Eventualities 1 and a pair of, log in together with your PubMedAdmin person, and for Eventualities 3 and 4, log in together with your PubMedLimitedUser to acquire the required id_token.
Situation 1
On this first question, we question the pubmed index with the credentials of person PubMedAdminUser, which is a part of pubmed_admin_group:
Add the next values to the respective enter fields:
- For Question strings, enter question=
"{"question":{"match_all":{}}}"&index=pubmed - For Headers, enter id_token:
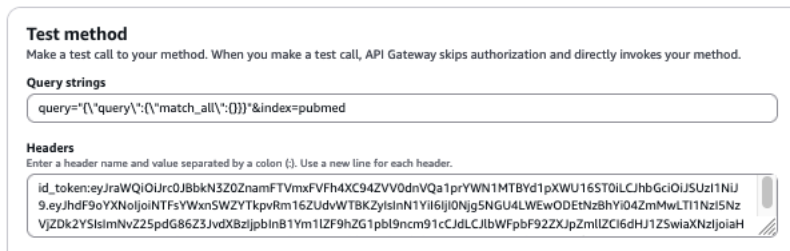
The next screenshot reveals our question outcomes.
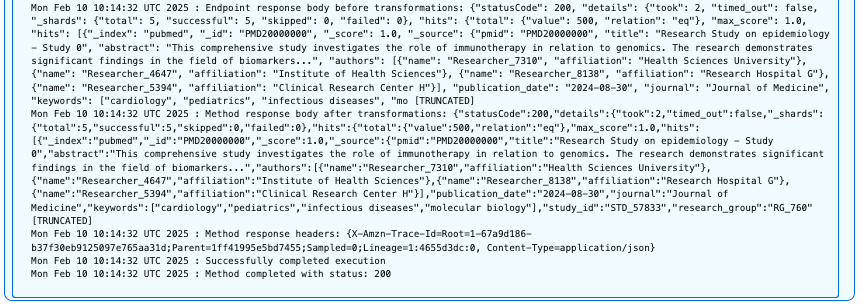
Customers with the pubmed_admin function have full entry to the PubMed index and may carry out unrestricted searches throughout all fields and doc varieties. This question efficiently returns paperwork with the HTTP 200 standing code as a result of the person has full learn permissions on this index.
Situation 2
Subsequent, we question the clinical-trials index with the credentials of person PubMedAdminUser, who’s a part of pubmed_admin_group:
Add the next values to the respective enter fields:
- For Question strings, enter question=
"{"question":{"match_all":{}}}"&index=clinical-trials - For Headers, enter
id_token:
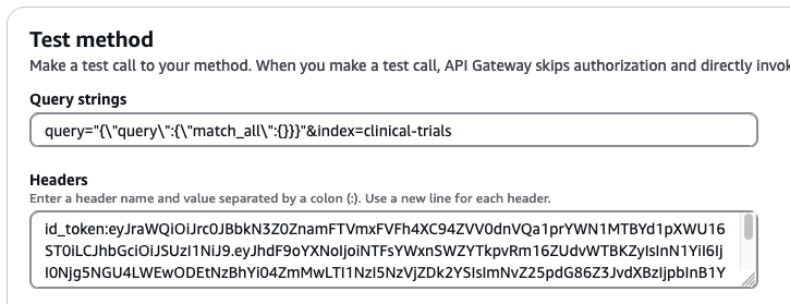
The next screenshot reveals our question outcomes.
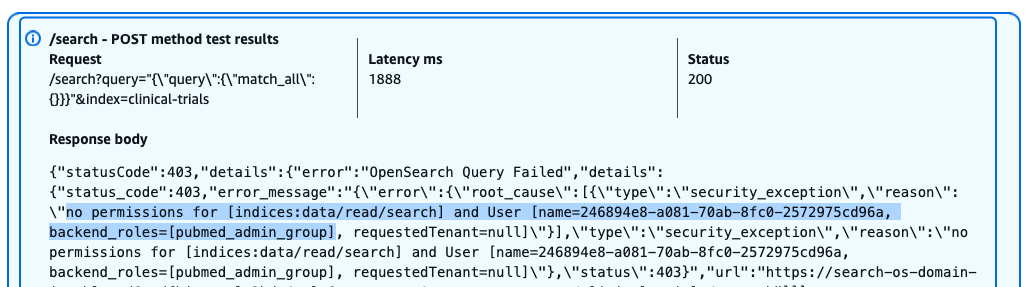
Regardless of having admin privileges for PubMed knowledge, this person receives a 403 Forbidden response when making an attempt to entry the clinical-trials index. The error message signifies the dearth of mandatory permissions for performing search operations on this index.
Situation 3
Now we question allowed fields within the pubmed index with the credentials of person PubMedLimitedUser, which is a part of pubmed_limited_group:
Add the next values to the respective enter fields:
- For Question strings, enter question=
"{"question":{"match":{"title": "molecular biology"}}}"&index=pubmed - For Headers, enter
id_token:
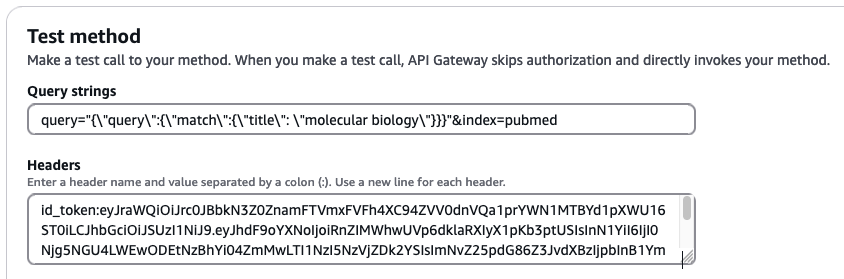
The next screenshot reveals our question outcomes.
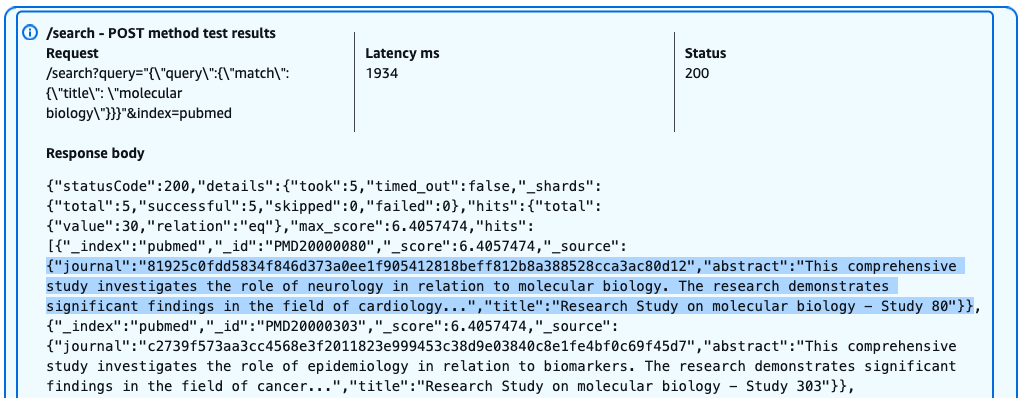
Customers with the pubmed_limited function can efficiently question particular fields like title, however with restricted entry to delicate data. The question returns outcomes with the HTTP 200 standing code, however the journal subject is anonymized resulting from field-level safety insurance policies. Customers can search and examine sure fields whereas having delicate knowledge mechanically masked or excluded from their outcomes.
Situation 4
Lastly, we question unauthorized fields within the pubmed index with the credentials of person PubMedLimitedUser, which is a part of pubmed_limited_group:
Add the next values to the respective enter fields:
- For Question strings, enter question=
"{"question":{"match":{"research_group":"RG_345"}}}"&index=pubmed - For Headers, enter
id_token:
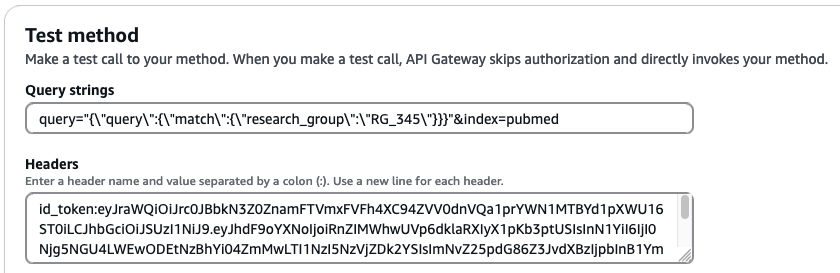
The next screenshot reveals our question outcomes.
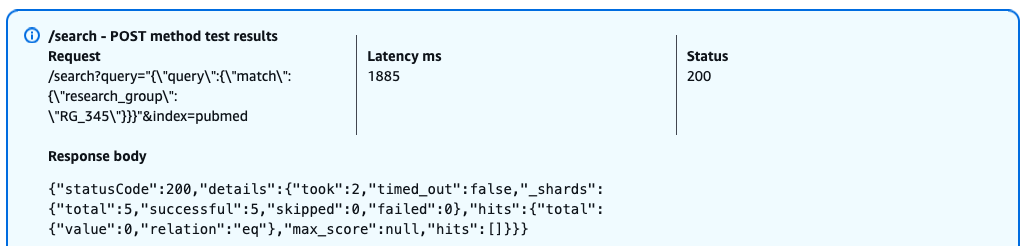
When a person with the pubmed_limited function makes an attempt to question the restricted research_group subject, OpenSearch returns a profitable response (HTTP 200) however with empty outcomes. This conduct happens as a result of field-level safety is implementing entry controls as an alternative of returning a HTTP 403 error, it silently filters out the restricted subject from each the question and outcomes. This security-by-obscurity method signifies that customers can’t decide whether or not their question failed resulting from lack of permissions or real absence of matching paperwork.
Clear up
To keep away from incurring additional AWS utilization fees, delete the sources created on this publish by deleting the CloudFormation stack. This step will take away all sources besides Lambda layers. To delete the Lambda layers, navigate to the Layers web page on the Lambda console, and delete the layers named
Conclusion
On this publish, we mentioned how JWTs present a sturdy and scalable authentication mechanism that may be built-in with current IdPs. We additionally demonstrated find out how to seamlessly combine fine-grained entry management throughout search functions. Organizations can outline granular permissions inside their IdP, ensuring delicate data stays protected. The JWT integration with OpenSearch Service permits safe, environment friendly entry management, so customers can solely entry role-appropriate data whereas simplifying compliance and entry administration.
When you’ve got suggestions about this publish, depart them within the feedback part. When you’ve got questions on this publish, begin a brand new thread on AWS Safety, Id, and Compliance re:Put up or contact AWS Assist.
In regards to the authors
 Ramya Bhat is a Information Analytics Guide at AWS, specializing within the design and implementation of cloud-based knowledge platforms. She builds enterprise-grade options throughout search, knowledge warehousing, and ETL that allow organizations to modernize knowledge ecosystems and derive insights by scalable analytics. She has delivered buyer engagements throughout healthcare, insurance coverage, fintech, and media sectors.
Ramya Bhat is a Information Analytics Guide at AWS, specializing within the design and implementation of cloud-based knowledge platforms. She builds enterprise-grade options throughout search, knowledge warehousing, and ETL that allow organizations to modernize knowledge ecosystems and derive insights by scalable analytics. She has delivered buyer engagements throughout healthcare, insurance coverage, fintech, and media sectors.
 Shubhansu Sawaria is a Sr. Supply Guide – SRC at AWS, based mostly in Bangalore, India. He focuses on designing and implementing complete AWS Cloud safety options. He has developed safety options for startups, banks, and healthcare organizations. His experience helps organizations elevate their cloud safety infrastructures, obtain compliance aims, and supply strong knowledge safety.
Shubhansu Sawaria is a Sr. Supply Guide – SRC at AWS, based mostly in Bangalore, India. He focuses on designing and implementing complete AWS Cloud safety options. He has developed safety options for startups, banks, and healthcare organizations. His experience helps organizations elevate their cloud safety infrastructures, obtain compliance aims, and supply strong knowledge safety.
 Soujanya Konka is a Sr. Options Architect and Analytics Specialist at AWS, centered on serving to prospects construct their concepts within the cloud. She has experience in designing and implementing enterprise search options and superior knowledge analytics at scale.
Soujanya Konka is a Sr. Options Architect and Analytics Specialist at AWS, centered on serving to prospects construct their concepts within the cloud. She has experience in designing and implementing enterprise search options and superior knowledge analytics at scale.

