
Two essential vulnerabilities affecting the open-source discussion board software program vBulletin have been found, with one confirmed to be actively exploited within the wild.
The issues, tracked underneath CVE-2025-48827 and CVE-2025-48828, and rated essential (CVSS v3 rating: 10.0 and 9.0 respectively), are an API technique invocation and a distant code execution (RCE) by way of template engine abuse flaws.
They affect vBulletin variations 5.0.0 by means of 5.7.5 and 6.0.0 by means of 6.0.3 when the platform runs on PHP 8.1 or later.
The vulnerabilities had been seemingly patched quietly final 12 months with the discharge of Patch Degree 1 for all variations of the 6.* launch department, and model 5.7.5 Patch Degree 3, however many websites remained uncovered as a consequence of not upgrading.
Public PoC and lively exploitation
The 2 points had been found on Might 23, 2025, by safety researcher Egidio Romano (EgiX), who defined exploit it by way of an in depth technical submit on his weblog.
The researcher confirmed that the flaw lies in vBulletin’s misuse of PHP’s Reflection API, which, as a consequence of behavioral modifications launched in PHP 8.1, permits protected strategies to be invoked with out express accessibility changes.
The vulnerability chain lies within the capacity to invoke protected strategies by way of crafted URLs and the misuse of template conditionals inside vBulletin’s template engine.
By injecting crafted template code utilizing the susceptible ‘replaceAdTemplate’ technique, attackers bypass “unsafe operate” filters utilizing tips like PHP variable operate calls.
This leads to totally distant, unauthenticated code execution on the underlying server — successfully granting attackers shell entry as the online server person (www-data on Linux, for instance).
On Might 26, safety researcher Ryan Dewhurst reported seeing exploitation makes an attempt on honeypot logs exhibiting requests to the susceptible ‘ajax/api/advert/replaceAdTemplate’ endpoint.
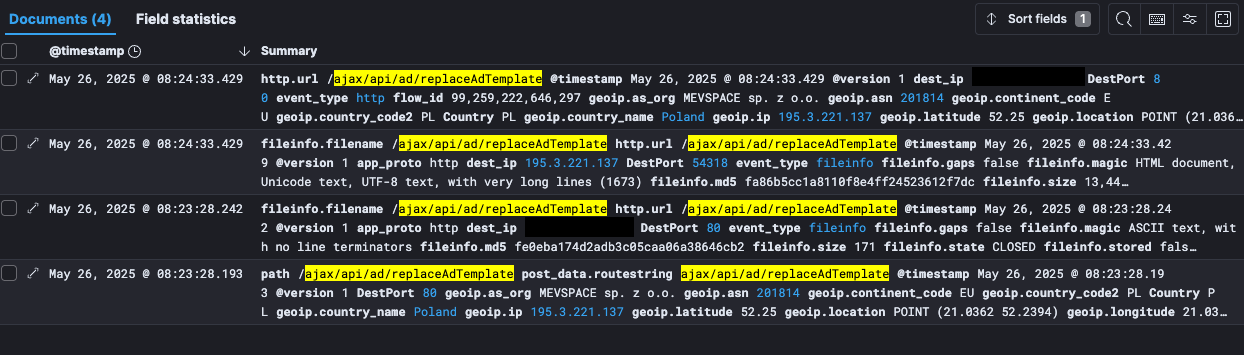
Supply: weblog.kevintel.com
Dewhurst traced one of many attackers to Poland, seeing makes an attempt to deploy PHP backdoors to execute system instructions.
The researcher famous that the assaults seem like leveraging the exploit revealed earlier by Romano, although there have been Nuclei templates accessible for the flaw since Might 24, 2025.
It is very important make clear that Dewhurst solely noticed exploitation makes an attempt for CVE-2025-48827, however no proof exists but that attackers have efficiently chained it to the total RCE, though that is extremely seemingly.
vBulletin troubles
vBulletin is likely one of the most generally used industrial PHP/MySQL-based discussion board platforms, powering 1000’s of on-line communities globally.
Its modular design, together with cell APIs and AJAX interfaces, makes it a fancy and versatile platform. Nevertheless, it additionally exposes a broad assault floor.
Up to now, hackers have leveraged extreme flaws within the platform to breach widespread boards and steal the delicate information of massive numbers of customers.
Discussion board directors are really useful to use the safety updates for his or her vBulletin set up or transfer to the newest launch, model 6.1.1, which isn’t affected by the stated flaws.


