I have to admit that I haven’t performed a thorough validation process yet. While it’s plausible to speculate that AAA/RBAC solutions receive more emphasis in Cisco certifications than other networking topics, As networking professionals progress from the Cisco Certified Network Associate (CCNA) to the professional level, they will encounter a range of authentication, authorization, and accounting protocols on their certification exams, including AAA, TACACS+, RADIUS, and Role-Based Access Control (RBAC).
Here’s a handful of examples for those who’d prefer to test it out themselves:
-
- APs can be administered using a range of entry methods, each offering unique benefits and security features. These include: Telnet, which enables remote access to the AP’s CLI, but is inherently insecure due to its reliance on plaintext passwords; SSH, a more secure alternative that encrypts both the password and data transmitted; HTTP, suitable for configuration changes, but lacking robust authentication mechanisms; HTTPS, combining the benefits of HTTP with secure encryption; console connections, providing direct physical access to the AP’s CLI; and finally, TACACS+ and RADIUS, offering centralized authentication and authorization controls.
- Authentication verifies a user’s identity by validating their credentials; it confirms who they claim to be. Authorization determines what actions the authenticated user is allowed to perform based on their role or permissions; it decides what they can do. Accounting tracks and records all interactions with a system, including successful and unsuccessful login attempts, data access, and other activities; it provides a log of events for auditing and security purposes.
-
- The organization’s IT infrastructure must ensure that all systems are properly configured and managed to prevent unauthorized access and data breaches. To achieve this goal, the team will establish and maintain a comprehensive system entry management process that includes:
Properly configuring firewalls and other network security controls
Monitoring system logs for suspicious activity
Developing and enforcing strict password policies
Implementing multi-factor authentication where feasible
Conducting regular vulnerability assessments
- The organization’s IT infrastructure must ensure that all systems are properly configured and managed to prevent unauthorized access and data breaches. To achieve this goal, the team will establish and maintain a comprehensive system entry management process that includes:
-
- Troubleshoot system safety by leveraging the powerful combination of Cisco’s built-in and external authentication, authorization, and accounting protocols, specifically TACACS+, RADIUS, and a robust native database.
-
- Implement robust system entry controls, seamlessly integrating with RADIUS and TACACS+ for comprehensive access management.
-
- Configure AAA for system and community entry mirroring TACACS+ and RADIUS configurations.
-
- 7.0 Community Entry System Administration
-
- What secure architecture for AI workloads requires robust authentication, authorization, and access control?
-
- 5.1.xb Community|Compute|Storage Safety – AAA and RBAC: Implementing Secure Access Controls
-
- Administration of aircraft safety involves various protocols and technologies to ensure a secure and controlled environment for flight operations. AAA (Accounting and Authentication Association) is a standard for securing authentication, accounting, and auditing, which prevents unauthorized access to aircraft systems. Additionally, TACACS (Terminal Access-Control Access Control System) provides an additional layer of security by controlling and monitoring user access to aircraft networks and devices.
-
- Implementing robust infrastructure safety measures requires a secure and reliable connection to TACACS (Terminal Access-Control Access-Control Server). This protocol provides authentication, authorization, and accounting services for remote access to network devices, ensuring seamless integration with existing security frameworks. By configuring TACACS on routers, switches, and firewalls, network administrators can effectively manage user privileges, track login activities, and enforce strict security policies.
Here are 10 distinct certifications spanning from Affiliate to Expert where these issues arise. You’ll also find them featured in professional-level exams, including but not limited to those administered by, , and labs. I’m skeptical that any topic would have broader protection than intellectual property law does currently. What are the aspects of my life and relationships that I’ve been neglecting?
While AAA is indeed a crucial topic, even seasoned professionals may still require clarification on its nuances. Before we dive into the specifics, let’s take a step back and examine what the “AAA” label typically connotes.
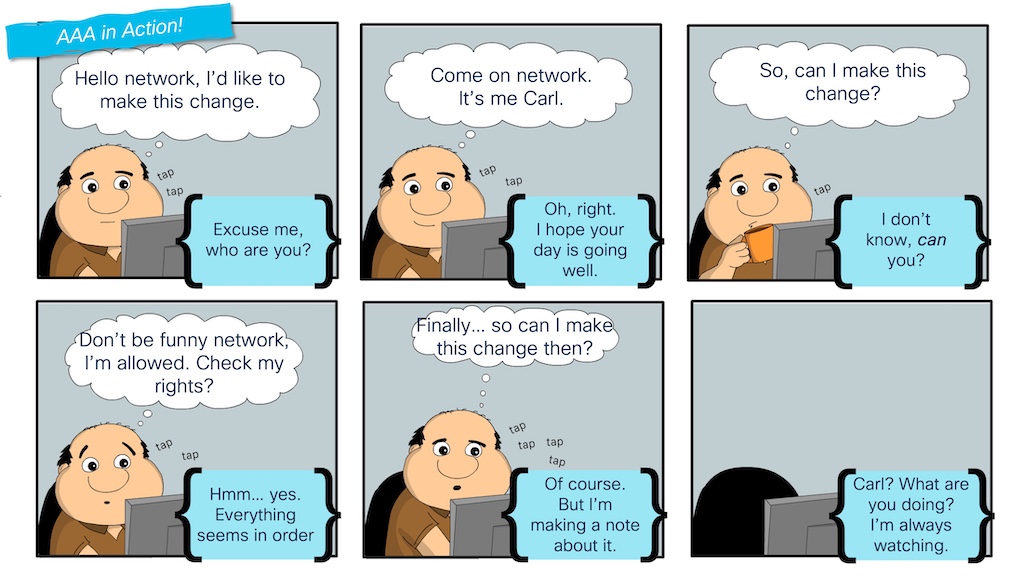
In the side-splitting “AAA in Motion!” sketch, comedian Carl embarks on a hilarious journey through the entirety of his AAA experience.
- In computing, the primary “A” stands for Application. The attempt to modify the community is thwarted as Carl’s request comes too early in his designated timeframe for making changes.
- Even after verifying Carl’s ID, his access is determined by the rights he has been assigned within the community, primarily dependent on those permissions.
- The third and final ‘A’ stands for, as Carl notices in motion when making his way into the community.
TACACS plays a crucial role in centralized administration by facilitating the management of customer accounts, roles, and logging capabilities. Its functions encompass authentication, authorization, and accounting for seamless network management. While community systems may be tailored to address regional AAA requirements, this approach does not effectively scale for large-scale enterprise environments. Communities would benefit from a unified approach, where each entity communicates seamlessly with a centralized server to facilitate streamlined interactions. TACACS is a protocol used by network devices and servers to communicate and manage each aspect of “AAA” (Authentication, Authorization, and Accounting). A TACACS server is a software application that facilitates the TACACS protocol.
With a deep understanding of the pivotal role AAA plays in a community, and its significance across various certifications, I recommend leveraging my go-to community simulation/virtualization tool, Cisco Modeling Labs (CML), to master tips on how to analyze and prepare for it. As part of my commitment to transparency and knowledge-sharing, I publicly shared several findings related to CML topology on the platform.
While some solutions cater to individual needs, another offers a Nexus 9000v swap to seamlessly integrate knowledge center platforms, thus expanding its scope of application. After mastering this blog post, you’ll easily grasp the topologies and discover new ones on your own.

What’s the best way to set up a TACACS server on Cisco Modeling Labs?
Before configuring TACACS on a switch or router, ensure that a TACACS server is accessible within your network. In a manufacturing setting, a standard TACACS server serves as a comprehensive “identity provider” engine for managing system administration, community access, wireless security, VPN access, and more.
For network professionals, Cisco ISE is an essential tool that plays a critical role in ensuring the security of their organization’s infrastructure. Now that we’ve dedicated ourselves to this cause? When incorporating Cisco ISE into a CML node library via the resources available in the CML Group, running a full-fledged ISE server within the topology might be deemed excessive when the primary objective is to merely configure TACACS for system administration purposes alone.
Fortunately, there are light-weight options. My go-to option is the open-source “tac_plus” utility, which has been available for several years. Tac is a primary Linux utility that can be easily downloaded and installed on most Linux distributions. While initial enthusiasm for the mission may have waned, its potential remains untapped and presents a valuable opportunity for addressing similar situations in the future.
Upon reviewing the image of the CML topology, one notices that the “aaa-server” is situated prominently on the left side of the diagram. Here is the rewritten text:
A common starting point for an Ubuntu node from the CML reference platforms, this installation provides a basic configuration setup to deploy tac_plus and configure it as the primary TACACS server.
To explore further details, feel free to examine the configuration within the topology file. Alternatively, here’s a concise overview of the essentials involved in building my TACACS server.
- To obtain and set up the tac_plus utility from source code, you will need to perform the following steps:
Obtain the tac_plus source code by cloning the repository or downloading it directly from GitHub.
Configure your development environment by installing the necessary dependencies such as automake, autoconf, and libssl-dev. You can do this using a package manager like apt-get on Ubuntu-based systems.
Navigate to the directory where you downloaded the tac_plus source code and run the command “./configure” to generate the configuration files for building the utility.
Compile the tac_plus source code by running the command “make” in the same directory. This will create an executable file called tac_plus.
Install the tac_plus utility by running the command “make install”. This will copy the executable file to a location on your system where it can be executed.
Verify that the tac_plus utility is installed correctly by checking its version using the command “tac_plus -v”.
Configure and test the tac_plus utility according to your specific use case.
- The tac_plus.conf file must contain the following parameters:
secret 0x82737a4e7d1a5b2c81f8c9a3e5c8c2a1b
customer 101
default-service = network
privilege-range = 1-15customer 102
default-service = exec
privilege-range = 16-31role 100
permit-network-consolerole 200
permit-telnet
deny-network-console - [Unit]
Description=TAC+ Authentication Service
After=network.target[Service]
User=tacplus
ExecStart=/usr/sbin/tac_plus -c /etc/tac_plus.conf
Restart=always[Install]
WantedBy=multi-user.target - Set up, configure, obtain, and initiate the tac_plus server functionality.
With the AAA server configured in the bottom CML topology file, Tac+Plus is now operational and ready to process requests efficiently, as the lab has commenced.
cisco@aaa-server:~$ systemctl standing tac_plus ● tac_plus.service - tac_plus Service Loaded: loaded (/and so on/systemd/system/tac_plus.service; enabled; vendor pres> Energetic: lively (operating) since Mon 2024-10-14 19:16:37 UTC; 2s in the past Foremost PID: 5982 (tac_plus) Duties: 1 (restrict: 2310) Reminiscence: 416.0K CPU: 2ms CGroup: /system.slice/tac_plus.service └─5982 /tacacs/sbin/tac_plus -G -C /and so on/tacacs/tac_plus.conf -d 8 > Oct 14 19:16:37 aaa-server systemd[1]: Began tac_plus Service. Oct 14 19:16:37 aaa-server tac_plus[5982]: Studying config Oct 14 19:16:37 aaa-server tac_plus[5982]: Model F4.0.4.28 Initialized 1 Oct 14 19:16:37 aaa-server tac_plus[5982]: tac_plus server F4.0.4.28 beginning Oct 14 19:16:37 aaa-server tac_plus[5982]: socket FD 4 AF 2 Oct 14 19:16:37 aaa-server tac_plus[5982]: socket FD 5 AF 10 Oct 14 19:16:37 aaa-server tac_plus[5982]: uid=0 euid=0 gid=0 egid=0 s=11063704>
Once our TACACS server is fully operational, we’ll proceed to configure our Cisco IOS router to leverage its functionality. Before configuring a TACACS server on an IOS device, ensure that certain preliminary steps are completed on the router. iOs has been around for years, undergoing numerous refinements in its approach to authentication and authorization mechanisms.
To begin, we need to confirm that the “New Mannequin” feature for AAA is properly enabled on our system.
aaa new-model
To ensure continued accessibility, we intend to establish a neighbourhood administrator account with the capability to access and manage the system in the event the TACACS server becomes unavailable. Consider setting up a dedicated neighborhood account for secure and seamless access to serial and console connections.
username cisco privilege 15 password cisco
In this command, the username and password are respectively set to “cisco”, not exactly the most secure option, though it’s suitable for a laboratory setting. The “privilege 15” component assigns the user the role of administrator. The root level of an iOS system, where privilege 15 grants unrestricted access, enabling the user to execute any instruction without limitations.
We are now able to configure and examine TACACS. Initially, I jump onto the server’s console to start tracking log files. I can verify and confirm the outcomes both on the server-side as well as on the consumer side.
System logs indicate the tac_plus service initiation on AAA server, with configuration study and model initialization. The server begins operation, establishing sockets for AF 2 and AF 10 protocols, with elevated privileges (uid=euid=0, gid=egid=0).
Wonderful. Now, I’ll navigate back to the router to configure the TACACS+ server and integrate it with a pool of available servers providing AAA services.
aaa-server handle IPv4 192.168.0.10 key tacacs123 aaa group server tacacs+ server identify aaa-server
As a pragmatist, I’m a proponent of testing a hypothesis or approach before moving forward. Conveniently, iOS features a “take a look at aaa” command that we’ll utilize.
The authentication attempt to AAA-TACACS using TACACS+ has been made for the user 'iosadmin' with password 'admin123', testing legacy configuration.
That appears nice! I am able to view the logs on the “aaa-server” with equal effectiveness.
October 14, 2019, 7:55:16 PM - The aaa-server's tac_plus process with ID 6473 successfully processed a join request from IP address 192.168.0.1. October 14, 2019, 7:55:17 PM - The tac_plus process with ID 6473 accepted the login question for user 'iosadmin' coming from unknown port and IP address 192.168.0.1.
With unwavering confidence, let’s complete the AAA configuration for all three A’s.
! Authentication aaa authentication login default group AAA-TACACS native? Authorization aaa authorization exec default group AAA-TACACS native aaa authentication login enable ! The following commands implement AAA (Authentication, Authorization, and Accounting) settings for a network device: Accounting default start-stop group AAA-TACACS? accounting instructions 1 default start-stop group AAA-TACACS accounting instructions 15 default start-stop group AAA-TACACS
Building on that robust foundation of self-assurance, let’s put this approach to the test. Exit the router until it’s no longer worth continuing without logging back in.
IOS-01 Con0 Now Available. Press 'Enter' to Begin. Identity Confirmation Required: Please Enter Your Username:
Attempt to log in to the router using the TACACS+ credentials for the Cisco IOS system.
Person Entry Verification Username: iosadmin Password: ios01#
Success! Examine the logs on the server to uncover insights akin to this:
I’ve highlighted the server output by distinctively colouring the authentication and authorization logs, thereby demonstrating that these processes are fundamentally separate entities.
Press Ctrl+C to stop tracking the service log and access the “Accounting Log” instead.
tail -f /var/log/tac_plus.acct October 14, 20:05:03 192.168.0.1: iosadmin logged in on tty0 using async protocol, starting task ID 12, with UTC timezone and shell service.
Router# show clock? Run the command “write memory” on your router to ensure that any configuration changes are saved to its non-volatile memory, thereby avoiding potential losses in case of a power outage or system reboot. A newly generated log message should now appear in the accounting log.
October 14, 2023, 8:10:11 PM, 192.168.0.1, iosadmin, tty0, asynchronous, task ID 13, timezone UTC, service shell, privilege level 15, command: write reminiscence
Let’s log out and wrap up our session. A brand-new message should seem effective:
Oct 14, 20:11:02, a log entry was generated from IP address 192.168.0.1 by user iosadmin. The event occurred on tty0 and the task ID is 13. The system's timezone is UTC, and the service responsible for this action is shell. Additionally, the reason for disconnection is cause 1 (unknown), with an extended reason of 9, and the pre-session time was six seconds.
All three “A”s have been thoroughly and successfully validated. Wonderful work!
Here’s a revised version: You’re in luck – the comprehensive CML topology information, which I discussed earlier and have outlined below, is now available for your immediate use. Within these documents are comprehensive lab guides that walk users through key AAA topics, including utilization of local accounts on consoles and serial lines for Cisco IOS devices, as well as configuring TACACS+ on Nexus equipment. Despite potential biases, I urge you to conduct an unbiased investigation, delving into topics within your purview.
Evaluating the impact of problems and failures is crucial for a community engineer’s proficiency, enabling them to confidently navigate unexpected events in “real-life” situations. Proactively identifying and addressing issues in a controlled laboratory setting is significantly more effective than waiting for production to experience difficulties. There’s no higher device than Cisco Model-Based Learning for that exploration.
My own AAA exploration will now begin. On this blog and lab, I have merely touched on the basics of the subject matter and provided data relevant to various certifications. RADIUS servers can serve as an alternative to TACACS+ when implementing remote access control, and similarly, they are often used in conjunction with Authentication, Authorization, and Accounting (AAA) protocols for issues such as VPN authentication, community access via 802.1x, or other platforms like ASA firewalls?
There are numerous additional opportunities awaiting discovery in future blog entries. Can we clarify what you’re referring to when you say “extra on AAA”? SKIP
Till subsequent time!
Join | Be part of the .
Useandto affix the dialog.
Share:

