ESET Analysis, Risk Studies
APT groups investigated and analyzed by ESET in Q2 and Q3 2024: An Overview
ESET Advanced Persistent Threat (APT) Exercise Report: Q2 2024-Q3 2024 provides a comprehensive summary of significant activities by selected APT groups, as tracked by ESET’s research team between April and September 2024. The highlighted operations serve as a microcosm of the comprehensive landscape of threats we scrutinized during this period, showcasing pivotal characteristics and advancements, and represent merely a small subset of the comprehensive cybersecurity intelligence data provided to clients of ESET’s private APT reports.
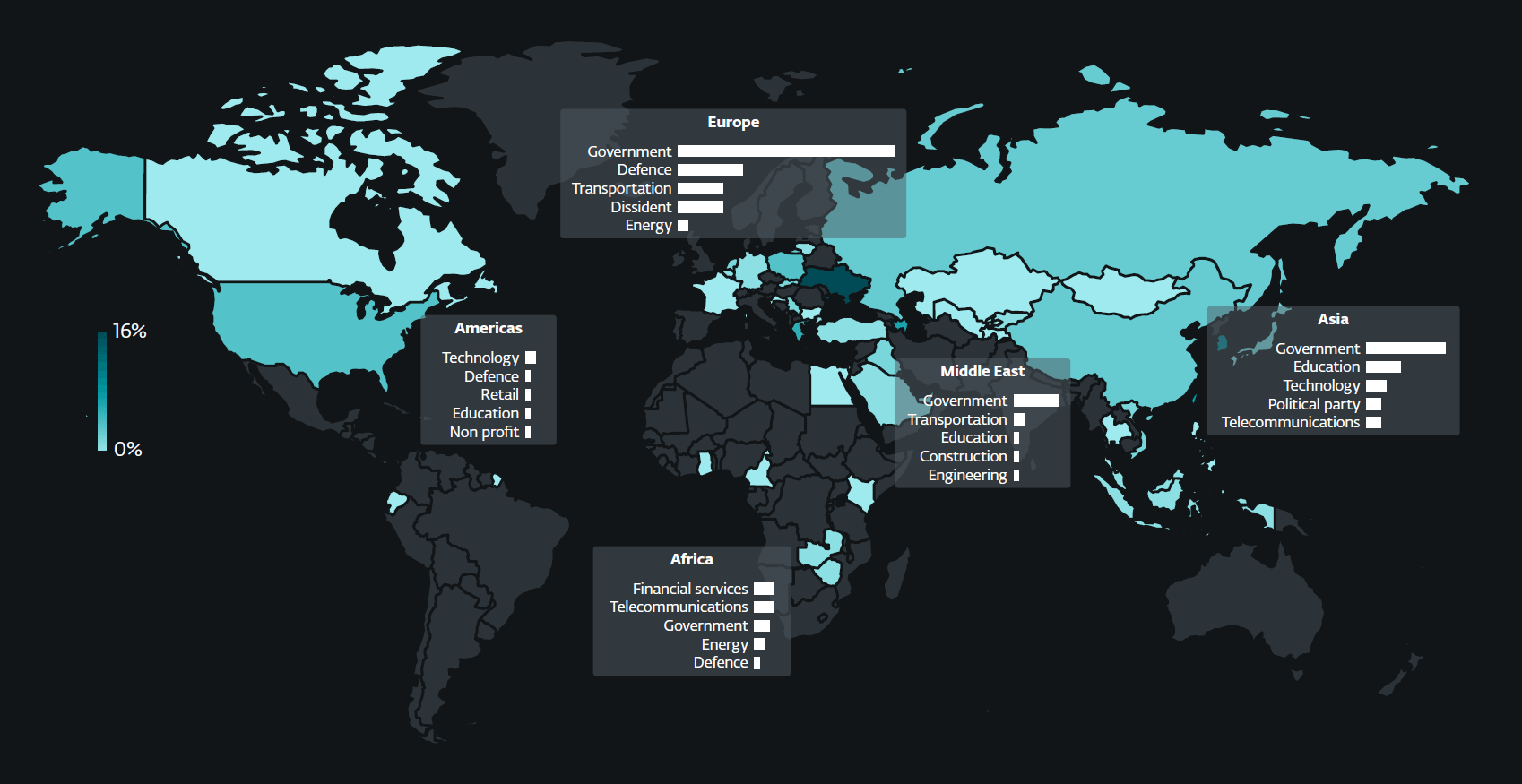
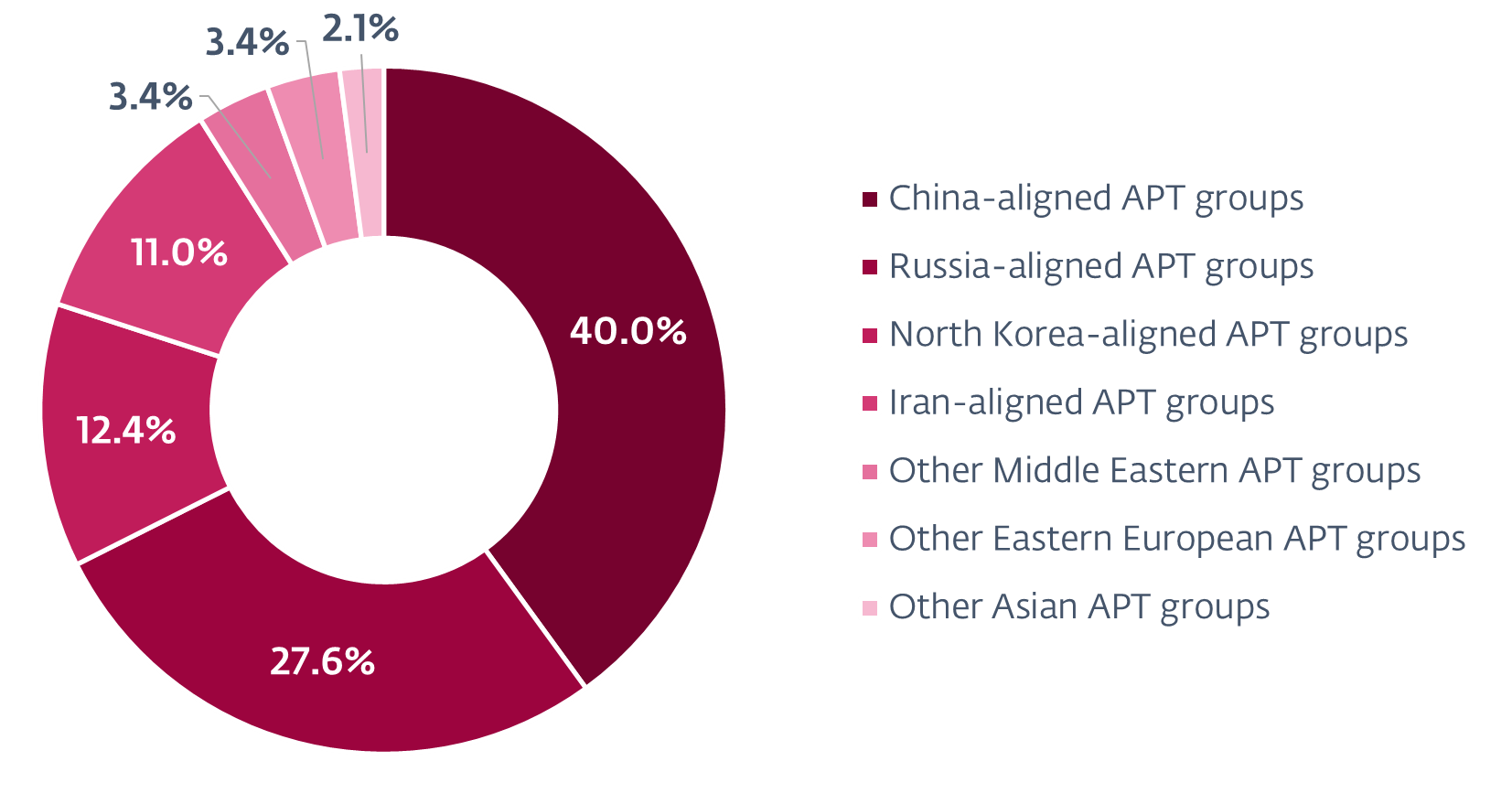
During the monitored period, a significant surge was observed in attention dedicated to China-linked MirrorFace. As it focused primarily on Japanese entities, the organization extended its scope to establish a diplomatic arm within the European Union (EU) for the first time, while maintaining its core Japanese objectives. Notably, China-linked advanced persistent threat (APT) groups are increasingly leveraging the open-source and platform-agnostic SoftEther VPN to maintain unauthorized access to targets’ networks. Intensive exploitation of SoftEther VPN was identified as being conducted by Flax Hurricane, with Webworm switching from its full-featured backdoor to utilizing SoftEther VPN Bridge on machines belonging to governmental organizations within the EU. Additionally, GALLIUM deployed SoftEther VPN servers at telecommunications operators in Africa.
We have also detected signs that Iran-backed entities may be utilizing their cyber assets to facilitate diplomatic espionage and potentially support kinetic operations. A sophisticated network of hackers targeted several financial institutions in Africa, a region of strategic importance to Iran, conducted cyber-attacks on Iraqi and Azerbaijani infrastructure, neighbours with whom Iran enjoys close ties, and demonstrated interest in Israel’s transportation sector. Despite its narrow territorial scope, Iranian-backed groups pursued a global strategy, cultivating diplomatic ties in France and scholarly connections in the US.
North Korean-aligned cybercriminals persistently pursued objectives aligned with their regime, which has faced accusations from the United Nations and South Korea of siphoning funds in both traditional currencies and cryptocurrencies to support its weapons of mass destruction programs. The teams persisted in launching attacks against defense and aerospace companies in both Europe and the US, as well as targeting cryptocurrency developers, tank manufacturers, and non-governmental organizations (NGOs). The North Korean-backed hacking group, KimSuKy, has exploited vulnerabilities in Microsoft’s Administration Console to gain unauthorized access and execute arbitrary Windows commands, potentially compromising critical systems managed by IT administrators. North Korean-backed teams have persistently exploited the vulnerabilities of major cloud-based services, including Google Drive, Microsoft OneDrive, Dropbox, Yandex Disk, pCloud, GitHub, and Bitbucket. For the first time, a sophisticated APT group known as ScarCruft was observed exploiting vulnerabilities in Zoho’s cloud services.
Russian-backed cyber operatives persistently target webmail platforms like Roundcube and Zimbra through persistent spear phishing campaigns that exploit known cross-site scripting (XSS) vulnerabilities in email systems. Besides targeting government, tutorial, and defense institutions globally, our research identified another Russia-linked group, dubbed GreenCube, exploiting cross-site scripting (XSS) flaws in Roundcube to pilfer email communications. Russian-backed groups persisted in targeting Ukraine, with Gamaredon orchestrating sprawling spear-phishing operations that leveraged and exploited vulnerabilities within popular messaging platforms like Telegram and Signal. Sandworm, leveraging its novel Windows backdoor, dubbed WrongSens, as well as its sophisticated Linux malware, comprising LOADGRIP and BIASBOAT, exploited vulnerabilities to wreak havoc. Furthermore, our analysis revealed the existence of Operation Texonto, a sophisticated disinformation campaign targeting Ukrainian morale while also sowing discord among Russian dissenters.
We also analyzed the public hack-and-leak of the Polish Anti-Doping Agency, which we suspect was compromised by an initial access broker who then shared credentials with Belarus-aligned FrostyNeighbor Advanced Persistent Threat (APT) group, known for cyber-enabled disinformation campaigns targeting the North Atlantic Alliance. Ultimately, following an analysis of a discovered exploit in the wild, our team uncovered a remote code execution vulnerability affecting WPS Workplace on Windows. The attack, which leveraged an identified exploit, is attributed to the South Korea-aligned Advanced Persistent Threat (APT)-C-60 group.
Malicious activities detailed in the ESET APT Exercise Report for Q2 2024-Q3 2024 have been identified through ESET’s product offerings, with primary insights derived from proprietary ESET telemetry data and validated by ESET’s research team.