More than one million domains, including those owned by Fortune 100 companies and prominent security firms, remain vulnerable to takeover by hackers due to authentication flaws at several major hosting providers and domain registrars, according to a newly published study.
Picture: Shutterstock.
Your internet browser knows how to locate a website such as instance.com thanks to the Domain Name System (DNS), a global directory that functions like a digital phonebook, translating human-readable website names (instance.com) into numerical IP addresses.
When registering a website domain, registrars typically provide two essential DNS (Domain Name System) components that require assignment by the client. As a result, these details are crucial because they enable internet browsers to locate the web address of the hosting provider serving that domain.
Potential issues arise when a website’s DNS information is “lame,” meaning the authoritative name server lacks sufficient data, impeding query resolution. A website can become unresponsive in several ways, for instance, if it’s not assigned a domain name or due to misconfigured or absent title servers in the area’s authoritative document.
The issue with lame domains lies in the fact that numerous Internet hosting and DNS providers allow users to exercise control over a website, which can lead to unwanted consequences.
If this risk sounds familiar, it’s because it’s hardly unprecedented. In 2019, KrebsOnSecurity reported on a sophisticated scheme in which criminals exploited a vulnerability to seize control of hundreds of domains registered with GoDaddy. The web hosting giant reportedly addressed this weakness shortly after the incident was publicized.
In the 2019 marketing campaign, spammers exploited vulnerabilities in domain registration, capitalizing on the ease with which they could create accounts on GoDaddy and seize control of weak domains by assigning themselves the same DNS servers as those of the compromised site.
Three years prior, security expert Bob Smith published a blog post detailing a widespread vulnerability, demonstrating how hackers could exploit DNS weaknesses at several major web hosting companies.
Recent research from safety experts at [Institution 1] and [Institution 2] has revealed that the same authentication vulnerability remains prevalent across several prominent internet hosting and DNS service providers, collectively unveiled today.
According to John Smith, principal risk researcher at Infoblox, the vulnerability is straightforward to exploit, yet challenging to identify, making it entirely preventable. Companies that operate for free simplify large-scale exploitation. The vast majority of those are concentrated at a few major DNS providers.
SITTING DUCKS
Discovered, in fact, is the widespread exploitation by cybercriminal syndicates of compromised domain names as a global “traffic redirection infrastructure,” enabling the masking of genuine origin or destination traffic, and facilitating the rerouting of unsuspecting internet users to malevolent or phishing websites.
Thieves can commandeer domains in this manner, permitting them to impersonate reputable manufacturers and exploit the trust associated with those companies by sending emails that appear to originate from the hijacked domains – a tactic we observed being used in the 2019 GoDaddy attacks.
“Hijacked domains have been swiftly leveraged in phishing attacks and scams, alongside large-scale spam campaigns,” states the Infoblox report, which designates lame domains as “. There exists evidence that certain domains were utilized for Cobalt Strike and other malware command and control (C2) purposes. Different types of assaults have leveraged hijacked domains in targeted phishing attacks by crafting convincing lookalike subdomains. Actors are reported to have secretly amassed hijacked domain names, sparking concerns about their mysterious intentions.
Researchers at Eclypsium estimate that approximately one million Sitting Duck domains exist, with a staggering 30,000 of those having fallen prey to malicious activity since 2019?
“As of this writing, several DNS providers permit this vulnerability by lacking robust domain ownership verification for registered accounts,”
Companies specializing in online safety revealed that many compromised “Sitting Duck” domains were originally registered by model safety firms, which focus on proactive domain registration strategies to pre-emptively secure lookalike domains for well-known brands, thereby preventing potential scams and trademark infringement.
Infoblox uncovered cybercriminal groups exploiting a vulnerable zone, dubbed “Sitting Duck,” located on CBS Interactive’s servers. Initially registered in 2009 through GoDaddy. The .com domain name was upgraded to DNSMadeEasy.com servers in 2010; two years later, in 2012, control of the domain was transferred.
The APWG, a prominent non-profit cybersecurity organization, registered another hijacked domain, “Sitting Duck”, in 2003 as part of its efforts to monitor and combat phishing attacks.
Researchers discovered numerous instances where Sitting Duck domains were set to automatically renew through their registrar, yet the corresponding authoritative DNS or hosting services failed to be renewed.
Researchers assert that Sitting Duck domains invariably exhibit three characteristics rendering them susceptible to takeover.
The area leverages or assigns authoritative DNS services to a separate provider from the area registrar.
The authoritative title servers for the region lack information about the web address that should be delegated.
the authoritative DNS supplier is considered vulnerable and exploitable due to its potential susceptibility to cyber attacks. An attacker can declaratively designate a specific domain space on the supplier and orchestrate DNS configurations without requiring direct access to the legitimate domain owner’s account at the area registrar.
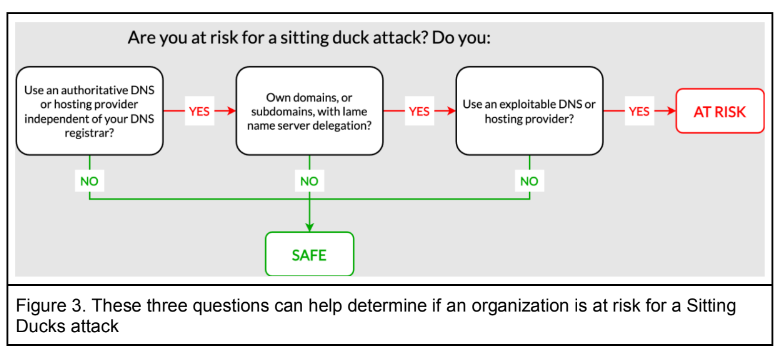
Picture: Infoblox.
To identify potential vulnerabilities in a DNS supplier’s infrastructure, consider conducting a thorough risk assessment by examining their publicly available information. This may involve reviewing the supplier’s documentation, such as security bulletins and whitepapers, to gain insight into their security posture. Additionally, it’s essential to research any reported exploits or vulnerabilities related to the supplier’s services, which can be found through online platforms like vulnerability databases or bug tracking systems. Here is the rewritten text:
A frequently updated list, known as “,” has been tracking instances of exploitable DNS provider vulnerabilities over several years. The list provides illustrations for each designated Domain Name System (DNS) provider.
Within the Sitting Duck case, clickermediacorp[.]com initially belonged to an unknown entity, but was subsequently seized by scammers who claimed ownership through a hosting agency affiliated with DigiCert, one of the world’s leading SSL/TLS certificate issuers?
According to an interview with KrebsOnSecurity, Paul Rosenzweig, founder and senior vice chairman of DNSMadeEasy, argued that the issue at hand is not his company’s responsibility to resolve, pointing out that DNS suppliers who are also not area registrars lack the capability to verify whether a given customer genuinely owns the domain being claimed.
“We take swift action to terminate abusive accounts as soon as they are identified,” Job said. Notwithstanding this, I firmly believe that the primary responsibility lies with domain registrants themselves? When considering purchasing something that needs to be installed or deployed in an area where you lack control, we can’t intervene.
According to Infoblox, Eclypsium, and the DNS wiki, GitHub itemizes Bluehost as one of the many weak internet hosting companies, with large hosting being a significant issue. In response to inquiries, DigitalOcean indicated that it is investigating potential measures to mitigate such issues.
In a statement to clarify, DigitalOcean emphasized that its DNS service should not be considered authoritative, nor is it intended to register websites. When a website owner authoritatively delegates control over their domain name system (DNS) records to our infrastructure through their registrar, but subsequently allows the associated DNS record ownership to expire within our system, it results in a “lame delegation” scenario under this hijacking model? We attribute the foundation trigger to lax administration of area title configurations by property owners, akin to carelessly leaving keys in an unlocked car. We collaborate closely with analysis teams to identify additional mitigation strategies.
According to a press release issued to KrebsOnSecurity, the internet hosting provider and registrar revealed that they have been actively working on implementing a solution to prevent “lame duck” attacks in the forthcoming weeks.
“We are actively working on deploying a Service-Oriented Architecture (SOA)-based area verification system,” Hostinger stated. To verify ownership of the desired domain name, customized nameservers should be implemented along with an authoritative SOA document that confirms the specific domain’s jurisdiction and proprietorship belongs solely to the client. We aim to successfully launch our user-friendly solution by the end of August. The ultimate step is to deprecate preview domains, a feature typically exploited by malicious actors seeking to perpetuate harmful activities. All preview domains will be deprecated by the end of September. Respected customers will have the ability to utilize randomly generated short-term subdomains as a convenient alternative.
Prior to the advent of modern solutions, DNS providers that faced authentication hurdles employed manual workarounds, such as using IP address-based whitelisting or relying on third-party services for validation. These makeshift measures often resulted in complexity, added latency, and decreased scalability. To successfully deploy a domain, top-tier registrars assigned random title servers to account holders, necessitating a modification at the registrar level prior to the domains going live. Moreover, they found that the top-performing DNS providers employed distinct strategies to guarantee that newly designated name servers did not coincide with previous domain name assignments.
Infoblox noted that numerous hijacked domains were hosted by , a massive web host that emerged just two weeks prior to Russia’s invasion of Ukraine, and has since flourished.
Without additional collaboration and reduced blame-shifting from all parties involved in the global DNS, attacks on vulnerable domains are likely to continue escalating, leaving domain registrants and ordinary internet users caught in the crossfire?
“Authorities, regulatory bodies, and industry standards must consider long-term strategies to mitigate vulnerabilities in the DNS infrastructure attack surface,” the Infoblox report advises.

