According to cybersecurity firm ESET, details have emerged about a new attack campaign targeting Android smartphone users.
A sophisticated cyberattack utilizing both a clever social engineering ruse and a newly developed Android malware enables attackers to siphon sensitive customer data, subsequently withdrawing funds from NFC-enabled ATMs by manipulating the stolen information.
The organization has successfully implemented measures to mitigate the impact of malicious activities.
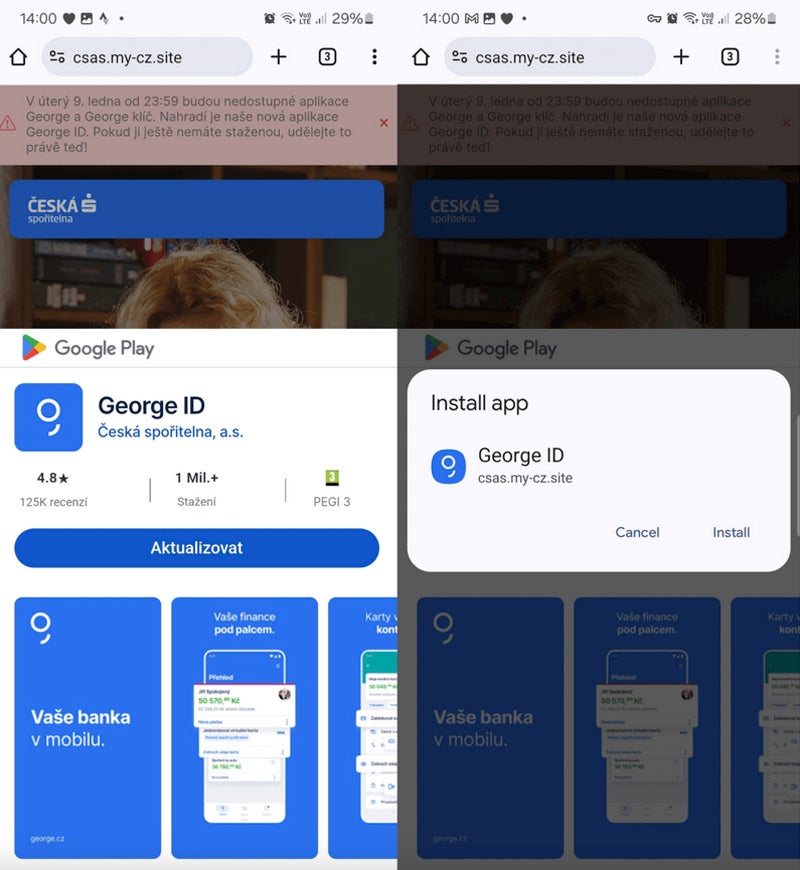
According to ESET, the malicious actor initially leveraged the capabilities of progressive internet apps, enabling them to set up an app from any website outside of the Google Play Store. This expertise is compatible with a range of popular browsers, including those based on the Chromium engine on desktop computers, as well as Firefox, Google Chrome, Microsoft Edge, Opera, Safari, Orion, and the Samsung Web Browser.
PWAs, accessible directly through browsers, boast versatility and are generally free from compatibility issues. PWAs, when installed on a device, can be recognized by their icon, which features an additional small browser icon alongside the standard app icon.

Cybercriminals leverage Progressive Web Apps (PWAs) to redirect unwitting users to fullscreen phishing websites, attempting to obtain sensitive information such as login credentials or financial data.
The key actor behind this marketing campaign shifted focus from Progressive Web Apps (PWAs) to Web Applications Packages (WebAPKs), a significantly more advanced type of PWA. While the distinction between Progressive Web Apps (PWAs) and WebAPKs may seem nuanced, it’s crucial to note that PWAs are built using web technologies, whereas WebAPKs employ a specific technology to integrate PWAs as native Android applications.
As the attacker sees it, employing WebAPKs is more discreet due to their icons no longer displaying a small browser icon, thereby evading detection.

The individual unwittingly downloads and installs a standalone application from a fraudulent website that pretends to be legitimate. Without further permission requested from users, that particular person allows access to an application from a third-party website.
Scammers often mimic legitimate Google Play Store components to create confusion, leading consumers to believe that the installation originates from the official source when in reality it stems from a fraudulent website.
NGate malware
On March 6, the same malicious infrastructure leveraged in previous phishing campaigns targeting Progressive Web Apps (PWAs) and Web Application Packages (WebAPKs) rapidly disseminated a fresh strain of malware, dubbed NGate. When downloaded and launched on the victim’s phone, the malware opens a fake website, requesting the user’s sensitive banking information, which is then transmitted to the criminal actor.
However, the malware also incorporated a legitimate application that enabled seamless NFC data transmission between devices without requiring rooting.
As soon as consumers provide banking information, they receive a prompt to enable NFC on their smartphone and place their bank card against its rear-facing camera until the app successfully detects the card details.
Full social engineering
While initial appearances might suggest that activating NFC for an app and having a fee card recognized is suspicious, the sophisticated social engineering tactics employed by malicious actors actually explain the situation.
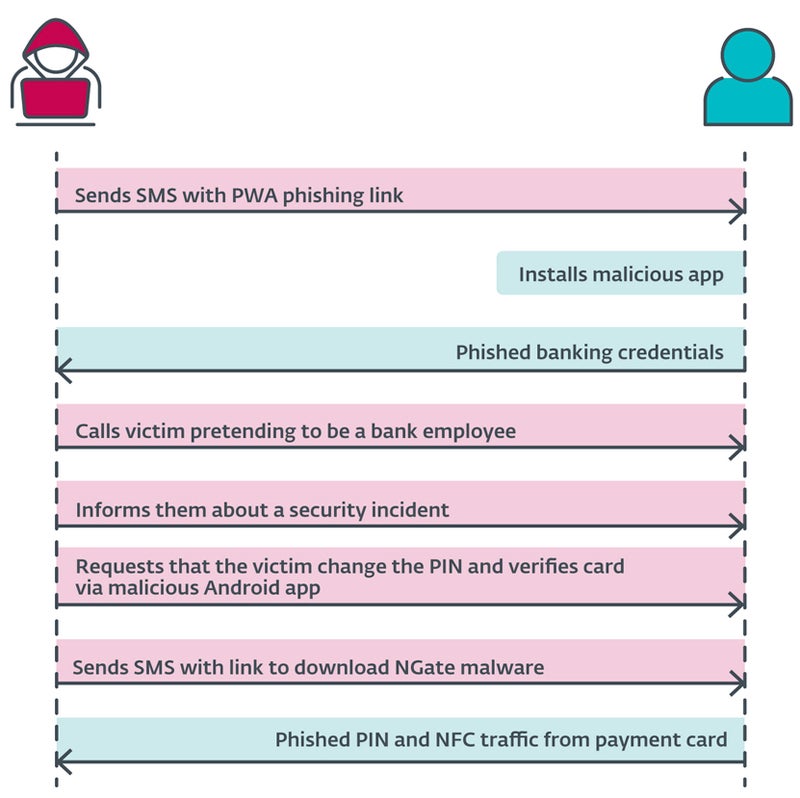
A cybercriminal transmits a suspicious SMS notification to a consumer, claiming to be related to a tax filing and accompanied by a link leading to a fake website mimicking those of financial institutions, ultimately culminating in the installation of a malicious Progressive Web App (PWA). As soon as the application is launched and executed, it promptly prompts users to provide their banking login information.
The menace actor, masquerading as a representative of the bank, makes a fraudulent phone call to the unsuspecting consumer, attempting to manipulate their trust and extract sensitive information. The individual is aware that their account has been compromised, likely due to an earlier suspicious SMS transmission. Consumers are subsequently guided to modify their Personal Identification Number (PIN) and verify banking card details through a mobile app, ensuring the security of their bank account.
The consumer subsequently receives a brand-new SMS, bearing a hyperlink that directs them to the NGate malware software.
The moment you initiate the process, the app prompts you to enable NFC functionality and authenticate your bank card by tapping it against the back of your smartphone. Real-time information is disseminated to the assailant.
Monetizing the stolen info
The stolen data enables the attacker to carry out routine fraudulent activities, including unauthorized withdrawals from bank accounts and using compromised credit card information to make online purchases.
Notwithstanding the unprecedented nature of this attack, the compromised NFC data enables cybercriminals to mimic legitimate bank cards, facilitating unauthorized withdrawals at ATMs employing NFC technology, thereby introducing a previously unknown vulnerability.
Assault scope
The cybersecurity firm ESET uncovered a spate of targeted attacks within the Czech Republic, with only local banks being targeted.
The 22-year-old suspect has been arrested in Prague. He clutched approximately six thousand euros, equivalent to around $6,500 USD. According to the Czech Police investigation, the seized funds likely stemmed from the combined total of thefts against the last three victims, implying that the perpetrator may have stolen significantly more during the entire operation.
Despite ESET researchers’ warnings, the malware’s potential to spread across various regions or countries cannot be entirely ruled out.
As NFC adoption accelerates among developers, cybercriminals are likely to employ similar tactics in the near future to pilfer funds via NFC transactions.
defend from this menace
To avoid falling prey to such cyber marketing tactics, customers should:
- Verify the provision of services procured and meticulously inspect URLs to guarantee authenticity?
- Be cautious when downloading software programs outside of authorized channels like the Google Play Store.
- Don’t share your credit card’s PIN code. No reputable banking institution will ever solicit sensitive information from unsuspecting individuals.
- Digital representations of traditional playing cards can be safely stored on the system, backed up with robust security features such as biometric authentication for added protection?
- Implement robust cybersecurity measures on mobile devices by installing a comprehensive safety software program that effectively detects and prevents malicious malware and unwanted behavior on the phone?
When not in use, customers should take the extra step of deactivating NFC functionality on their smartphones to prevent any potential data breaches. In unsuspecting moments, attackers may exploit the carelessness of leaving valuables unattended in public spaces – purses, wallets, and backpacks lying idle on benches, chairs or floors. The organisation will utilise the gathered data to facilitate minor, touch-free financial transactions. To safeguard against unwanted scrutiny, a protective circumstance will be established, fostering an environmentally conscious barrier to undesirable scanning activities.
In the event of uncertainty when contacted by a banking institution representative, it is recommended to hang up and reach out to the designated standard banking institution contact via an alternative phone number.

