Safe Community Analytics model 7.5.2 has been launched, providing thrilling new options such because the Community Visibility Module (NVM) and Zeek detections. We’re increasing our detections throughout current and new sources, and our detections engine now ingests NVM telemetry and Zeek logs, introducing 9 new alerts prominently displayed in Analytics. These alerts are additionally aligned with the widely known MITRE ATT&CK framework.
By integrating a extra numerous vary of telemetry sources, Safe Community Analytics considerably enhances community visibility and offers deeper insights into community actions. This launch and its detections symbolize a complicated strategy to broadening detection sources and capabilities. Customers using the Knowledge Retailer structure with Analytics enabled can improve to model 7.5.2 to right away entry these new capabilities.
The Safe Community Analytics model 7.5.2 software program updates could be downloaded from Cisco Software program Central.
New Community Visibility Module (NVM) Alerts
Community Visibility Module is a element of Cisco Safe Consumer that information and experiences on community exercise from an endpoint machine and ties in endpoint model data with these community particulars. If you’re used to accumulating NetFlow or IPFIX in your atmosphere, the Community Visibility Module will present the identical particulars a couple of community connection, however can even embrace issues like hostname, course of identify, consumer data, working system, interface particulars, and extra. This helps velocity up investigations and offers extra context about who and what host took an motion on the community. The detections engine processes the Community Visibility Module telemetry and alerts on 4 new detections.
You possibly can try the Community Visibility Module Configuration Information.
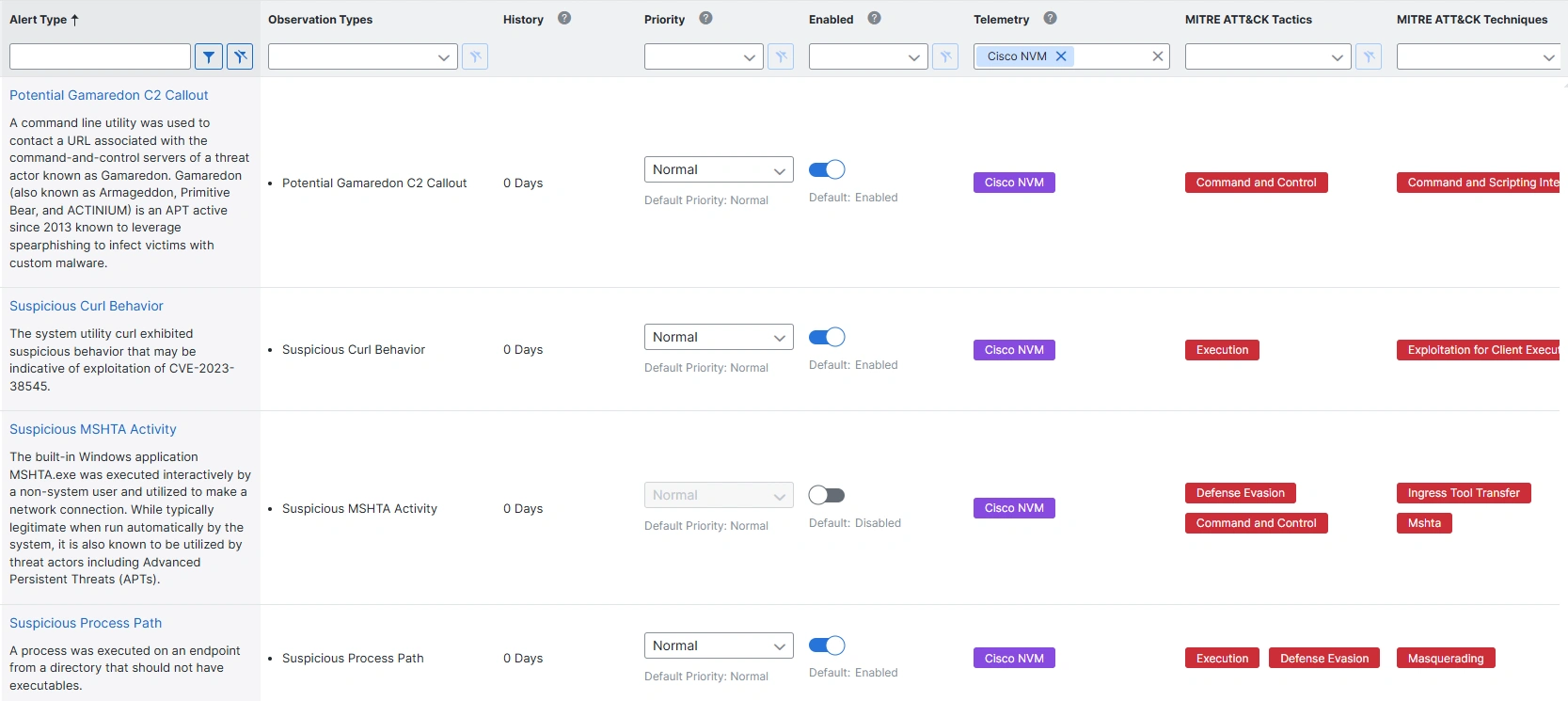
Community Visibility Module (NVM) Alert Names and Descriptions
Potential Gamaredon C2 Callout
A command line utility was used to contact a URL related to the command-and-control servers of a menace actor often called Gamaredon. Gamaredon (often known as Armageddon, Primitive Bear, and ACTINIUM) is an APT lively since 2013 recognized to leverage spearphishing to contaminate victims with customized malware.
Suspicious Curl Conduct
The system utility curl exhibited suspicious habits that could be indicative of exploitation of CVE-2023-38545.
Suspicious MSHTA Exercise
The built-in Home windows utility MSHTA.exe was executed interactively by a non-system consumer and utilized to make a community connection. Whereas sometimes respectable when run mechanically by the system, it is usually recognized to be utilized by menace actors together with Superior Persistent Threats (APTs).
Suspicious Course of Path
A course of was executed on an endpoint from a listing that ought to not have executables.
New Zeek Alerts
Zeek is a well-liked, free, and open-source community visitors evaluation device. It screens and inspects visitors and generates log information of witnessed exercise. These Zeek log information could be despatched to Safe Community Analytics as a telemetry supply. The detections engine reads the Zeek logs and alerts on 5 new detections.
Try the Zeek Configuration Information.
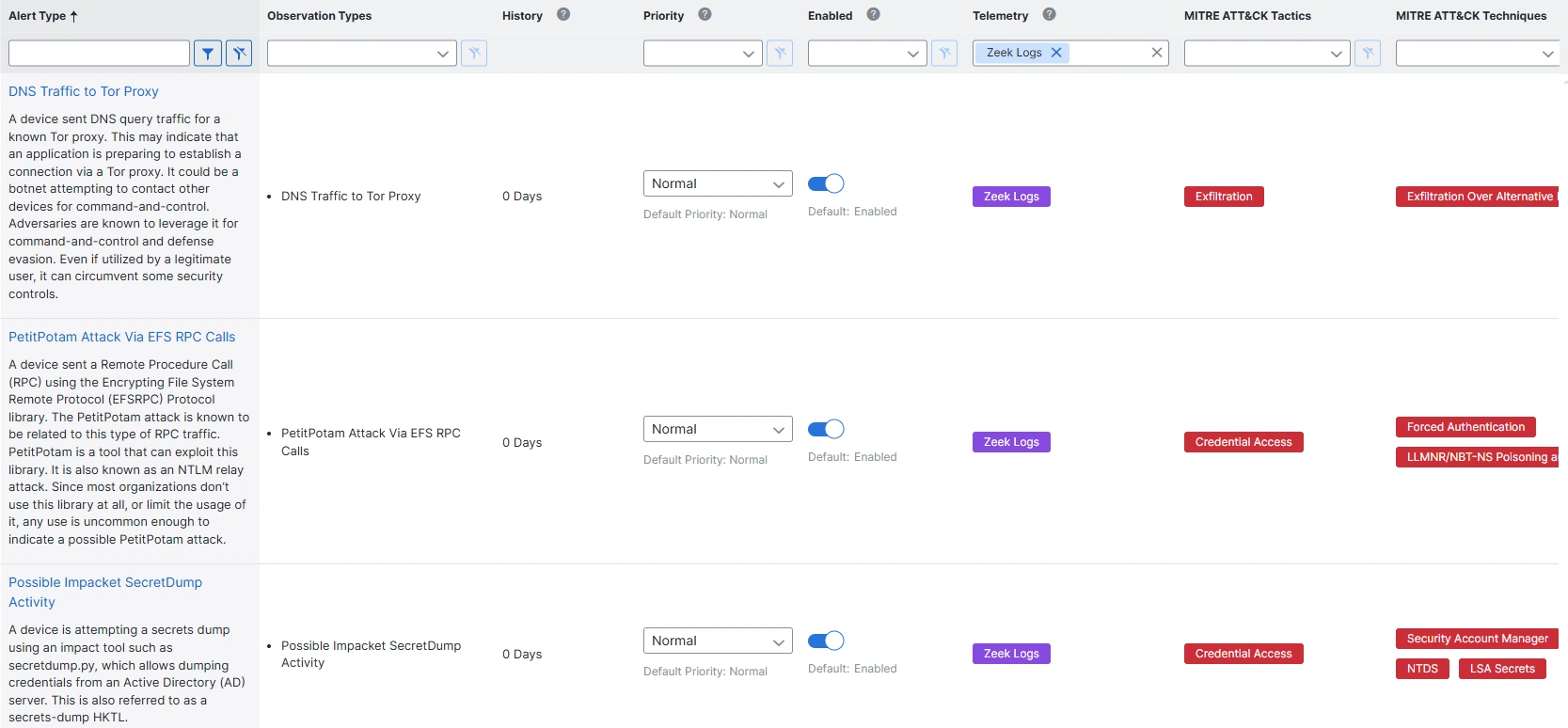
Zeek Alert Names and Descriptions
DNS Site visitors to Tor Proxy
A tool despatched DNS question visitors for a recognized Tor proxy. This will likely point out that an utility is getting ready to determine a connection by way of a Tor proxy. It may very well be a botnet trying to contact different gadgets for command-and-control. Adversaries are recognized to leverage it for command-and-control and protection evasion. Even when utilized by a respectable consumer, it may circumvent some safety controls.
PetitPotam Assault Through EFS RPC Calls
A tool despatched a Distant Process Name (RPC) utilizing the Encrypting File System Distant Protocol (EFSRPC) Protocol library. The PetitPotam assault is thought to be associated to one of these RPC visitors. PetitPotam is a device that may exploit this library. It’s also often called an NTLM relay assault. Since most organizations don’t use this library in any respect, or restrict the utilization of it, any use is unusual sufficient to point a doable PetitPotam assault.
Attainable Impacket SecretDump Exercise
A tool is trying a secrets and techniques dump utilizing an influence device resembling secretdump.py, which permits dumping credentials from an Energetic Listing (AD) server. That is additionally known as a secrets-dump HKTL.
Distant Process Creation by way of ATSVC Named Pipe
A tool is trying to create a distant job utilizing ATSVC named pipes, which may very well be a malicious try to make use of at.exe for performing job scheduling for preliminary or recurring execution of malicious code. The at.exe utility has been deprecated in present variations of Home windows in favor of schticks.
Suspicious PsExec Execution
A tool apart from a Home windows Sysinternal machine is utilizing psexec with a renamed service identify, which may point out a menace actor trying to carry out a distant execution.
Conclusion
Customers of the Safe Community Analytics Knowledge Retailer with Analytics will need to improve their occasion to model 7.5.2 to achieve entry to 9 new detections – 4 primarily based on Community Visibility Module telemetry and 5 primarily based on Zeek logs. These new detections are instantly obtainable in Analytics. Configure the sources to export and develop your detection protection in the present day.
References
We’d love to listen to what you assume. Ask a Query, Remark Under, and Keep Linked with Cisco Safe on social!
Cisco Safety Social Channels
Share:

