
Cisco has temporarily taken down its publicly accessible DevHub portal following the leak of “personal” data by an unknown threat actor, despite maintaining that there is currently no evidence to suggest its systems were compromised.
“We’ve concluded that the requested data resides within a publicly accessible DevHub environment, a Cisco resource hub that enables us to facilitate community engagement by sharing software code, scripts, and other relevant materials.” According to a statement from Cisco, the technology will be available for patrons to utilize at their discretion.
“At this point in our inquiry, we’ve concluded that a limited number of unlicensed files may have been leaked.”
Although Cisco has found no evidence of compromised sensitive information or financial data, it is still investigating the scope of potentially accessed data to ensure customer security.
Following an attack by a malicious entity commonly referred to as IntelBroker, an attempt was made to disseminate and provide access to stolen corporate intellectual property and source code.
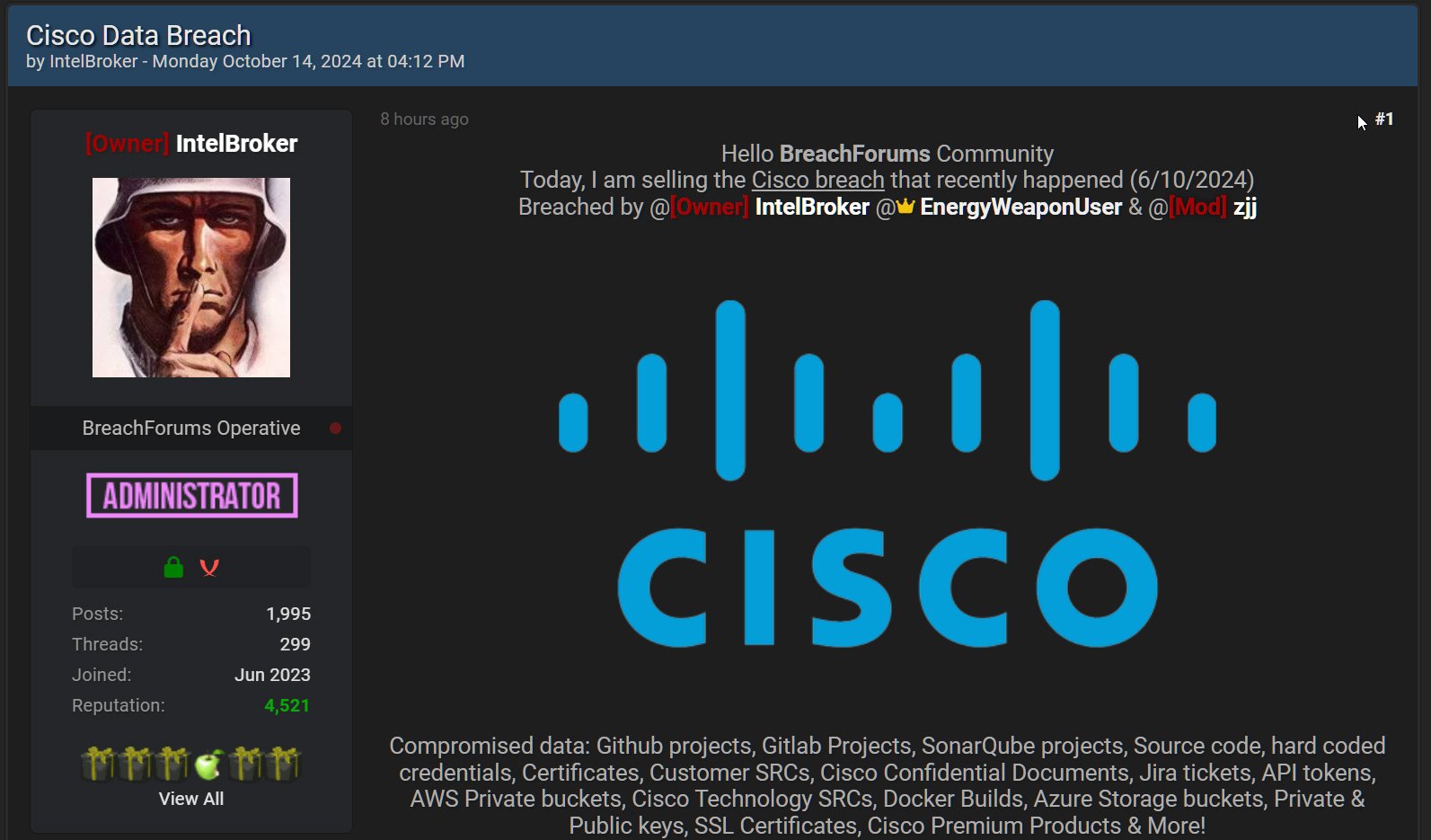
BleepingComputer interviewed IntelBroker regarding the purported breach, during which he revealed that he accessed a Cisco third-party developer environment utilizing an unsecured API token that was left exposed.
As Cisco’s inquiry into the matter progressed, IntelBroker’s frustration mounted as the corporation remained reluctant to recognize the safety incident, prompting him to share damning evidence – in the form of screenshots – with BleepingComputer, thereby demonstrating his unauthorized access to Cisco’s developer environment.
Screenshots and records data were shared with Cisco, revealing that the malicious actor gained access to nearly all information stored on this portal. This knowledge comprised supply code, configuration files containing database credentials, technical documentation, and SQL files.
The extent of buyer knowledge stored on these servers remains unknown, with no information being disclosed to us.
Following a prolonged period of exploitation, IntelBroker reportedly persisted in accessing the portal until the present moment, when Cisco allegedly took measures to block all entry points to both the compromised portal and jFrog development environment. The actor claimed that, in addition to his menacing actions, he lost access to a Maven and Docker server linked to the DevHub portal, but failed to provide evidence supporting this assertion.
When asked whether he attempted to extort Cisco from publishing the stolen information, IntelBroker claimed he didn’t try because they would likely not take him seriously and maintain their stance.
“I wouldn’t believe a malicious actor would request money to not leak my information, so I’d refuse to negotiate,” IntelBroker told BleepingComputer.
While Cisco maintains that no software has been compromised, all available evidence suggests that a third-party developer’s breach allowed attackers to pilfer sensitive information.
A request for comment from BleepingComputer to Cisco regarding the allegations was sent, but a response has yet to be obtained.

