ESET Analysis analyzes Gamaredon’s up to date cyberespionage toolset, new stealth-focused methods, and aggressive spearphishing operations noticed all through 2024
02 Jul 2025
•
,
6 min. learn
Since Russia’s full-scale invasion of Ukraine in February 2022, cyberespionage has performed an important function within the broader threatscape. Russia-aligned superior persistent risk (APT) teams have relentlessly focused Ukrainian entities, using cyberattacks alongside disinformation campaigns. ESET Analysis has carefully monitored these actions, often documenting cyber-operations carried out by numerous risk actors, together with the extremely lively Gamaredon group.
Key factors of this blogpost:
- Gamaredon refocused completely on focusing on Ukrainian governmental establishments in 2024, abandoning prior makes an attempt in opposition to NATO international locations.
- The group considerably elevated the size and frequency of spearphishing campaigns, using new supply strategies akin to malicious hyperlinks and LNK information executing PowerShell from Cloudflare-hosted domains.
- Gamaredon launched six new malware instruments, leveraging PowerShell and VBScript, designed primarily for stealth, persistence, and lateral motion.
- Present instruments acquired main upgrades, together with enhanced obfuscation, improved stealth techniques, and complicated strategies for lateral motion and information exfiltration.
- Gamaredon operators managed to cover nearly their whole C&C infrastructure behind Cloudflare tunnels.
- Gamaredon more and more relied on third-party companies (Telegram, Telegraph, Cloudflare, Dropbox) and DNS-over-HTTPS (DoH) for safeguarding its C&C infrastructure.
In our earlier blogpost, Cyberespionage the Gamaredon method: Evaluation of toolset used to spy on Ukraine in 2022 and 2023, we described Gamaredon’s aggressive cyberespionage actions in opposition to Ukrainian governmental establishments. As a part of our continued investigation, we’ve carried out an intensive technical evaluation of Gamaredon’s operations all through 2024. The detailed outcomes and technical insights can be found in our newest white paper.
Our analysis exhibits that the group stays extremely lively, constantly focusing on Ukraine, however has notably tailored its techniques and instruments.
Focusing on Ukraine completely
Gamaredon, attributed by the Safety Service of Ukraine (SSU) to the 18th Middle of Info Safety of Russia’s Federal Safety Service (FSB), has focused Ukrainian governmental establishments since not less than 2013. Whereas earlier years noticed occasional makes an attempt in opposition to targets in different NATO international locations, throughout 2024 Gamaredon operators returned their focus completely to Ukrainian establishments.
This strongly aligns with the group’s historic goal as a cyberespionage actor aligned with Russian geopolitical pursuits. Given the continued battle and geopolitical tensions, we anticipate Gamaredon’s focusing on of Ukraine to proceed unchanged within the foreseeable future.
Spearphishing campaigns develop bigger and extra frequent
Gamaredon’s spearphishing actions considerably intensified throughout the second half of 2024. Campaigns usually lasted one to 5 consecutive days, with emails containing malicious archives (RAR, ZIP, 7z) or XHTML information using HTML smuggling methods. These information delivered malicious HTA or LNK information that executed embedded VBScript downloaders akin to PteroSand. Determine 1 depicts the variety of distinctive samples of these HTA and LNK information delivered monthly in Gamaredon spearphishing campaigns in 2024.
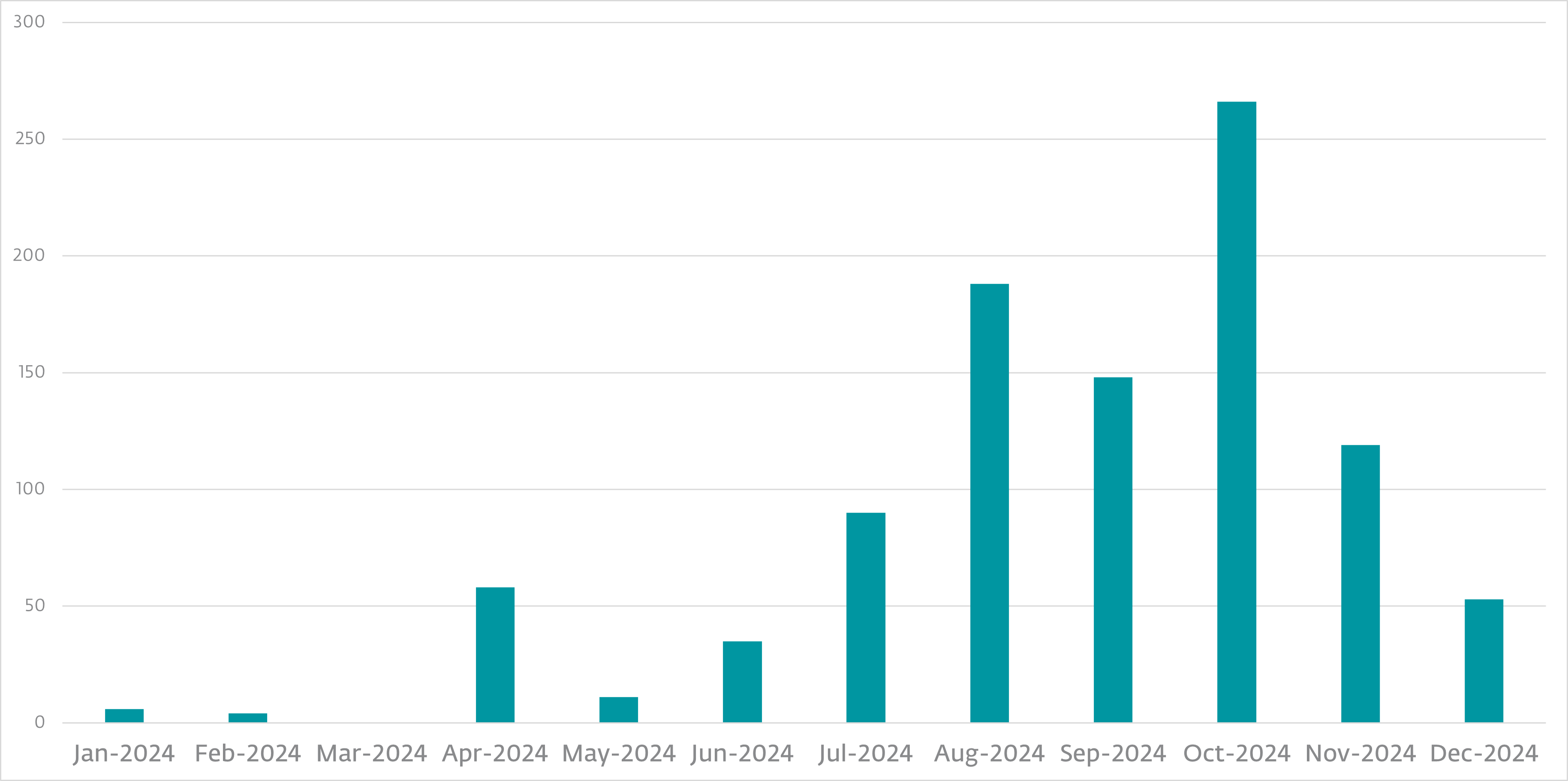
Surprisingly, in October 2024, we noticed a uncommon case the place spearphishing emails included malicious hyperlinks reasonably than attachments – a deviation from Gamaredon’s regular techniques. Moreover, Gamaredon launched one other novel approach: utilizing malicious LNK information to execute PowerShell instructions straight from Cloudflare-generated domains, bypassing some conventional detection mechanisms.
Toolset evolution: New instruments and important enhancements
Gamaredon’s toolset underwent notable updates. Whereas fewer new instruments had been launched (six in comparison with eight in 2022 and 9 in 2023), substantial sources went into updating and bettering present instruments:
New instruments launched in 2024 embody:
- PteroDespair: A brief-lived PowerShell reconnaissance device found in January 2024, developed to gather diagnostic information on beforehand deployed malware.
- PteroTickle: A PowerShell weaponizer found in March 2024, focusing on Python purposes transformed into executables on fastened and detachable drives, facilitating lateral motion. It weaponizes Tcl scripts usually present in Python GUI apps utilizing Tkinter and constructed with PyInstaller.
- PteroGraphin: Found in August 2024, this PowerShell device initially used an unusual persistence technique involving Microsoft Excel add-ins. It creates an encrypted communication channel for payload supply, by way of the Telegraph API. Later variations simplified persistence by utilizing scheduled duties as an alternative.
- PteroStew: A brand new general-purpose VBScript downloader found in October 2024, just like beforehand identified downloaders (e.g., PteroSand, PteroRisk), however that notably shops its code in alternate information streams related to benign information on the sufferer’s system.
- PteroQuark: One other VBScript downloader found in October 2024, launched as a brand new element throughout the VBScript model of the PteroLNK weaponizer.
- PteroBox: A PowerShell file stealer found in November 2024, carefully resembling PteroPSDoor however exfiltrating stolen information to Dropbox. It leverages WMI occasion subscriptions to detect newly inserted USB drives and exfiltrates chosen information utilizing the Dropbox API. The stolen information are meticulously tracked to keep away from redundant uploads, highlighting Gamaredon’s growing consideration to stealth and effectivity.
Main updates to present instruments in 2024
Along with new instruments, Gamaredon operators considerably upgraded present instruments of their arsenal:
- PteroPSDoor: A serious improve launched superior stealth methods, akin to monitoring file adjustments by way of the IO.FileSystemWatcher object reasonably than constantly scanning directories, considerably decreasing visibility. It additionally carried out WMI occasion subscriptions to detect new USB insertions, making file exfiltration extra focused and stealthier. Moreover, the newest variations retailer code completely in registry keys as an alternative of in information, additional complicating detection.
- PteroLNK (VBScript model): This device was enhanced in early 2024 to weaponize not solely USB drives but additionally mapped community drives, increasing its lateral motion capabilities. All through the second half of 2024, it acquired a number of incremental updates, together with improved obfuscation, extra complicated strategies for LNK file creation, and registry-based methods to cover information and file extensions from victims. This weaponizer has change into considered one of Gamaredon’s most regularly up to date and actively maintained instruments.
- PteroVDoor: This VBScript file stealer continued for use in two variants (obfuscated and unobfuscated). All through 2024, Gamaredon operators repeatedly up to date the device, introducing new exterior platforms akin to Codeberg repositories to dynamically distribute command and management (C&C) server data, complicating defensive measures.
- PteroPSLoad: Gamaredon notably transitioned again to utilizing Cloudflare tunnels as an alternative of ngrok for its C&C infrastructure. This marked the start of Gamaredon hiding nearly its whole C&C infrastructure behind Cloudflare-generated domains, considerably enhancing its operational safety.
Uncommon payloads: Russian propaganda by way of malware?
A very intriguing discovering was the invention in July 2024 of a singular advert hoc VBScript payload, delivered by Gamaredon downloaders. This payload had no espionage performance; reasonably, its sole goal was to robotically open a Telegram propaganda channel named Guardians of Odessa, which spreads pro-Russian messaging focusing on the Odessa area. Whereas uncommon for Gamaredon’s typical operations, we attribute this payload to Gamaredon with excessive confidence.
Community infrastructure and evasion methods
All through 2024, Gamaredon confirmed persistent dedication to evading network-based defenses:
- The group continued, albeit at a diminished scale, to leverage fast-flux DNS methods, regularly rotating IP addresses behind its domains. Nevertheless, the variety of domains that it registered declined notably from over 500 in 2023 to about 200 in 2024.
- Gamaredon more and more relied on third-party companies akin to Telegram, Telegraph, Codeberg, and Cloudflare tunnels to obfuscate and dynamically distribute its C&C infrastructure. Cloudflare-generated subdomains grew to become the group’s major communication endpoints, with conventional domains relegated largely to fallback use.
- A number of DoH companies (Google and Cloudflare) and third-party resolver web sites (akin to nslookup.io, who.is, dnswatch.data, and check-host.web) had been often leveraged to bypass domain-based blocking.
- Gamaredon additionally launched new methods akin to dropping embedded HTA and VBScript information into momentary directories and executing them individually to resolve C&C domains, additional complicating automated detection efforts.
Regardless of observable capability limitations and abandoning older instruments, Gamaredon stays a major risk actor resulting from its steady innovation, aggressive spearphishing campaigns, and chronic efforts to evade detections. So long as the Russia’s battle in opposition to Ukraine continues, we anticipate Gamaredon will persistently evolve its techniques and intensify its cyberespionage operations in opposition to Ukrainian establishments.
For an in depth technical breakdown of Gamaredon’s 2024 actions, updates, and malware analyses, learn our full white paper.
A complete listing of indicators of compromise (IoCs) may be present in our GitHub repository and the Gamaredon white paper.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at [email protected].ESET Analysis presents personal APT intelligence stories and information feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.

