Right here’s a short dive into the murky waters of shape-shifting assaults that leverage devoted phishing kits to auto-generate personalized login pages on the fly
09 Could 2025
•
,
4 min. learn
Phishing stays a very cussed risk within the cybersecurity panorama. It sticks round partly as a result of though the unhealthy guys are at all times after the identical prize – individuals’s login credentials and different delicate info – they by no means stop to evolve and adapt their techniques.
One approach that has gained traction in recent times is the usage of dynamically generated phishing pages. Utilizing devoted phishing-as-a-service (PhaaS) toolkits, attackers can spin up authentic-looking phishing pages on the spot, all whereas customizing them for whoever they’re concentrating on.
As an alternative of laboriously cloning a goal web site, even much less tech-savvy attackers can get the toolkits to do the heavy lifting for them – and in actual time and on a mass scale at that. One well-known instance of such a toolset, referred to as LogoKit, first made headlines in 2021 and apparently it hasn’t gone wherever since.
A distinct kettle of fish
So, how do these methods really play out?
Considerably predictably, the lure usually begins with an electronic mail that’s aimed to create a way of urgency or curiosity – one thing designed to make you click on shortly with out considering twice.
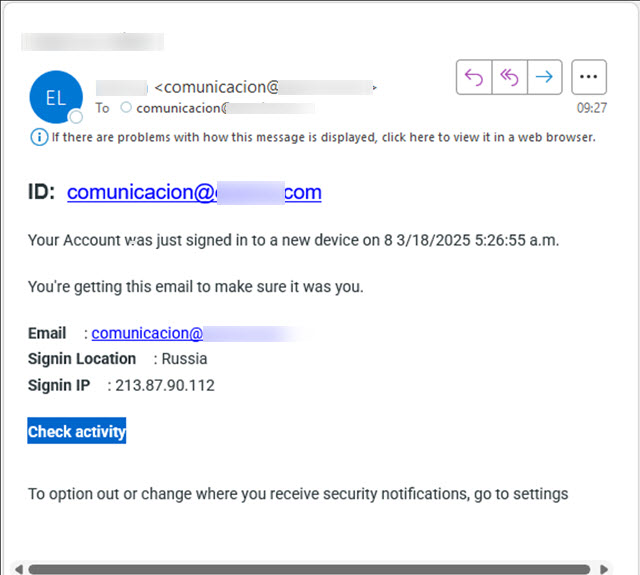
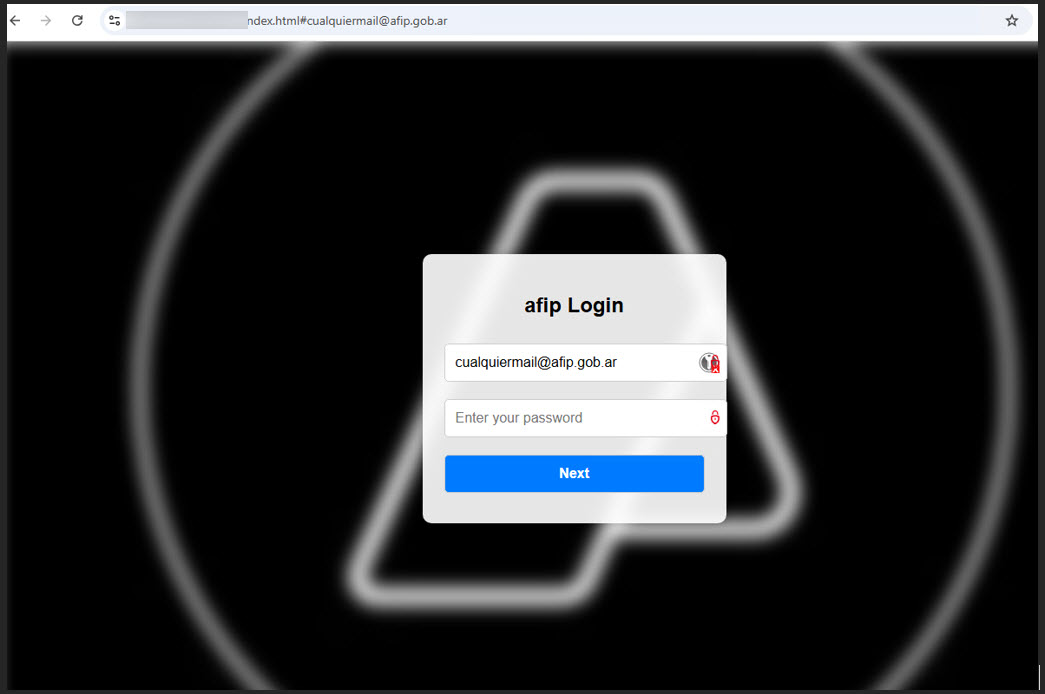
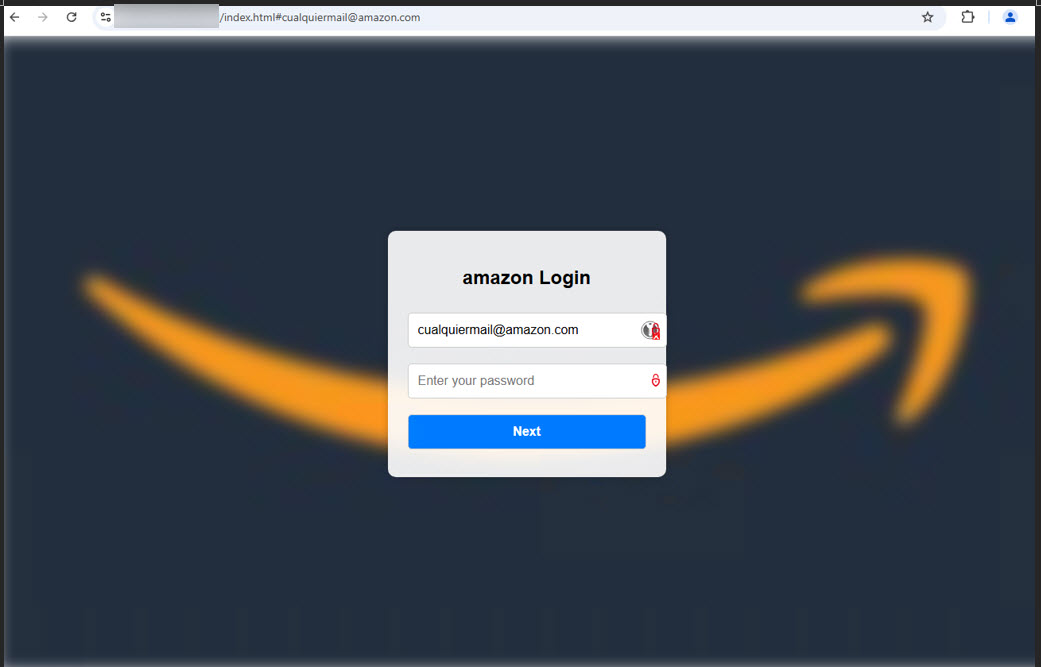
Clicking the hyperlink takes you to an internet site that may robotically retrieve the brand of the corporate that’s being impersonated, all whereas misusing the API (Utility Programming Interface) of a official third-party advertising and marketing service equivalent to Clearbit.
In different phrases, the credential-harvesting web page queries sources equivalent to enterprise knowledge aggregators and easy favicon lookup providers to fetch the brand and different branding parts of the corporate being impersonated, typically even including delicate visible cues or contextual particulars that additional increase the ploy’s aura of authenticity.
Including to the deception, attackers can even pre-fill your title or electronic mail tackle, making it appear to be you’ve visited the positioning earlier than.
The login particulars are despatched in actual time to the attackers by way of an AJAX POST request. The web page finally redirects you to the precise official web site you supposed to go to all alongside, leaving you none the wiser till it could be too late.
Loads of phish within the sea
It’s in all probability apparent by now, however the approach is a boon for attackers for a number of causes:
- Actual-time customization: Attackers can tailor the web page’s look immediately for any goal, sourcing logos and different branding parts from public providers on the fly.
- Enhanced evasion: Masking assaults with official visible parts helps evade detection by many individuals and a few spam filters.
- Scalable and agile deployment: Assault infrastructure is usually light-weight and simply deployed on cloud platforms equivalent to Firebase, Oracle Cloud, GitHub, and so forth. This makes these campaigns straightforward to scale and more durable for defenders to establish and dismantle shortly.
- Lowered boundaries to entry: Toolkits like LogoKit are available on underground boards, offering even much less tech-savvy people with the instruments wanted to launch assaults.
Staying off the hook
Defending in opposition to evolving phishing techniques requires a mix of ongoing private consciousness and strong technical controls. Nonetheless, a couple of tried-and-true guidelines will go a protracted technique to holding you secure.
If an electronic mail, textual content, or name asks you to click on a hyperlink, obtain a file, or present info, pause and confirm it independently. Don’t click on hyperlinks straight in suspicious messages. As an alternative, navigate to the official web site or contact the group by a trusted, identified telephone quantity or electronic mail tackle.
Crucially, use a robust and distinctive password or passphrase on all of your on-line accounts, particularly the dear ones. Complementing this with two-factor authentication (2FA) wherever accessible can be a non-negotiable line of protection. 2FA provides a important second layer of safety that may stop attackers from accessing your accounts even when they handle to steal your password or supply it from knowledge leaks. Ideally, search for and use app-based or {hardware} token 2FA choices, that are usually safer than SMS codes.
Additionally, use strong, multi-layered safety options with superior anti-phishing protections on all of your gadgets.
The underside line
Whereas the purpose – stealing individuals’s delicate info – is often the identical, the techniques utilized by cybercriminals are something however static. The form-shifting strategy proven above exemplifies the power of cybercriminals to repurpose even official applied sciences for nefarious ends.
The rise of AI-aided scams and different threats muddies the waters much more. With AI instruments within the fingers of criminals, phishing emails can evolve past templated gibberish and grow to be hyper-personalized. Combining vigilant consciousness with robust technical defenses will go a good distance towards holding the ever-morphing phish at bay..

