In May 2023, I penned a thought-provoking blog post serving as a clarion call, sounding the alarm about the perils of utilizing software developed from ostensibly trusted yet dubious “pirate” sources. Ultimately, this data had been purporting to be trustworthy yet secretly harbored malicious software, including notorious types like ransomware or infostealers, which specifically targeted that age group. By raising awareness of the risks associated with these apps, I hoped that the general public would learn how to identify and avoid them, subsequently seeking safer alternatives.
Within the year and a half since our initial blog post, the situation has not shown significant improvement: According to the ESET Risk Report for 2023, we’ve witnessed a notable surge in the detection of information stealers. Unlike before, the counterfeiters no longer appear to be merely embedded in pirated Windows video game copies, cracks, or illicit tools, but are also masquerading as authentic generative AI applications. Not exclusively are they limited to home windows, either. The notorious GoldDigger malware, which targets Android operating systems, has spent over a decade siphoning sensitive data, including bank card information, cryptocurrencies, and SSH credentials from UNIX-like platforms.
Infostealer detections consistently demonstrated high energy levels throughout the 24-month period spanning August 2022 to August 2024, with notable declines occurring around December and January each year.
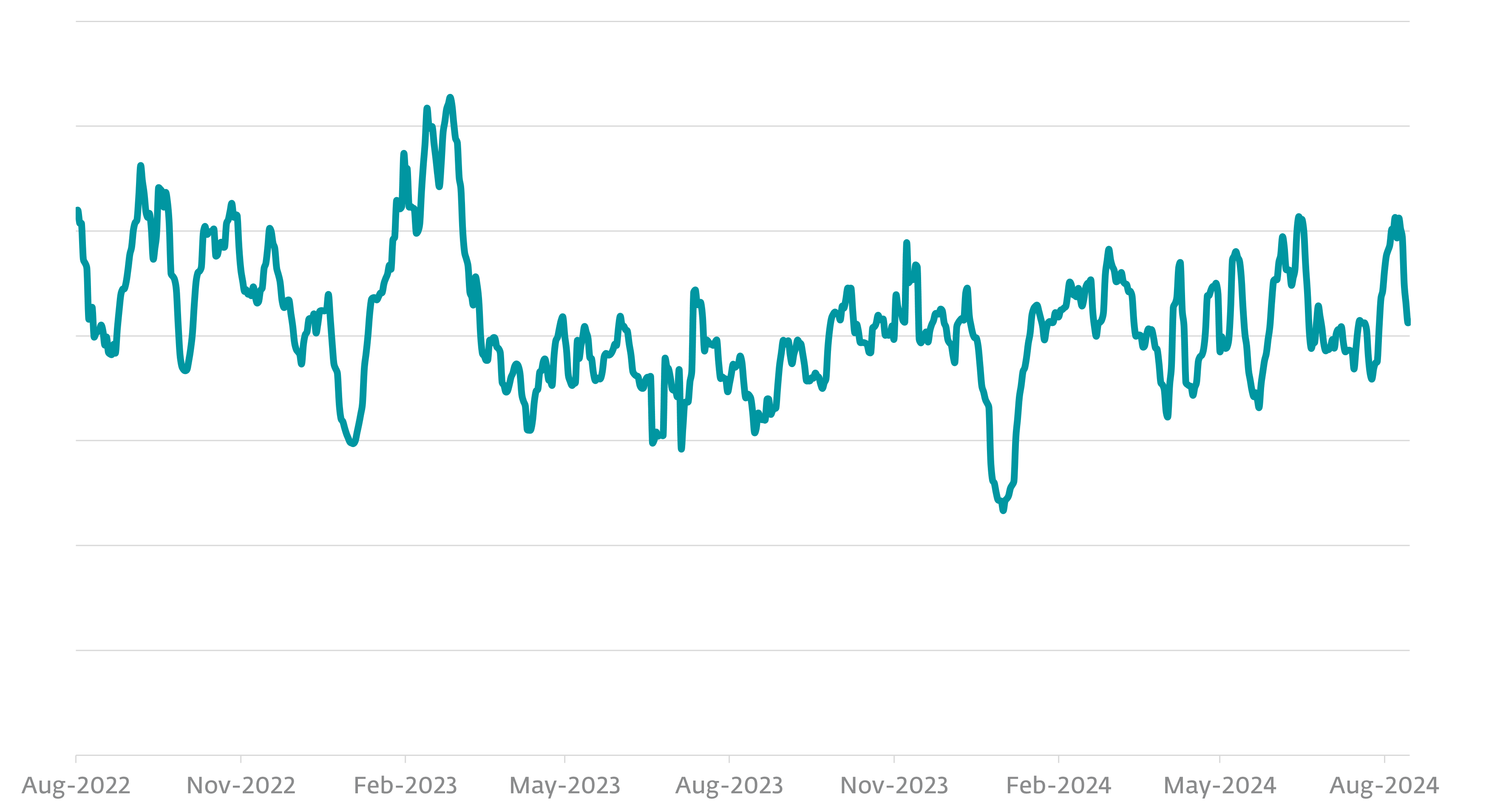
The sudden downturn in activity may stem from a decline in laptop usage among both victims and perpetrators, potentially attributed to the holiday season’s widespread adoption of downtime by individual criminal hackers who have evolved into more structured criminal organizations, akin to businesses taking a break.
While ESET identifies numerous families of infostealers, the top ten account for more than 56% of those detected, led by a single entity claiming 16.2% share?
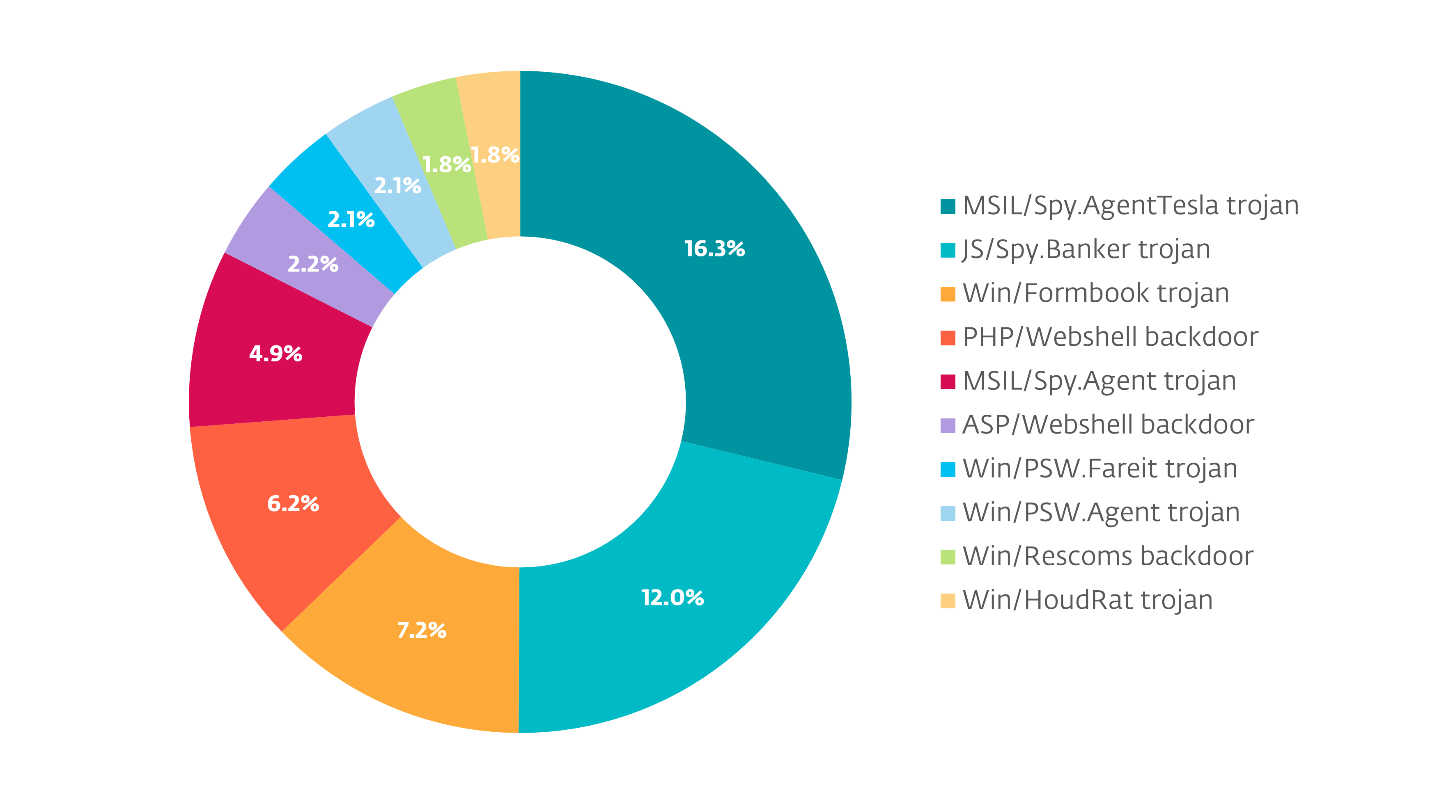
While many detected threats target Windows-based malware, it’s essential to note that information-stealing variants can be web-based as well. Although reducing encounter charges is a potential benefit, it’s plausible that these actors might have been able to effectively pilfer sensitive information from individuals not utilizing ESET software, thus expanding their influence.
While relying on ESET telemetry data, it’s plausible that other security firms’ findings could yield disparate results. Despite not being a hierarchical comparison, these distinctions arise from categorizing threats in alternative ways, serving distinct customer bases with diverse threat profiles, operating under varying circumstances, and more.
It appears that we’re capable of submitting distinct incident reports detailing varying costs associated with various types of malware, including information-stealing varieties.
Among the various topics that piqued my interest was the question of whether ESET’s data mirrored that of other security companies. Sandbox vendor ANY.RUN has reported a notable shift in the threat landscape, with info stealer gangs plummeting from the top spot in the first quarter to fourth place in the second quarter of 2024. Now, this does not suggest that there is any difference in information quality between ESET and ANY.RUN. The diverse landscape of safety instruments available presents inevitable discrepancies in reporting practices, as each company’s tools are often employed in various ways.
Cybercriminals increasingly engage in info theft for financial gain rather than mere enjoyment.
ESET categorizes information-stealing malware beneath its own distinct threat classification. As the number of apps involved in information-stealing activities increased, it became logical to group these variants under a distinct moniker, distinct from generic labels like Agent or Trojan, thereby acknowledging their unique characteristics and scope. Some developers of safety software may categorize these threats more generally as remote access trojans or adware, a classification that is also reasonable. The primary objective of detecting malware is to prevent its initial execution and minimize the potential damage caused by a successful infection. While the classification of malicious entities may hold significance within academic or marketing contexts during crises like the WannaCryptor incident, it tends to lose relevance outside these specific situations.
So, with all that in mind, what exactly is an info stealer, and what happens when you execute one?
As the title suggests, a type of malware known as an infostealer is capable of stealing sensitive information from a compromised laptop if deemed valuable by its operator. This collection comprises not only usernames and passwords for multiple websites accessed through the online browsers installed on your PC, but also those for various system functions. Recreational accounts can be compromised, plundered of irreplaceable artifacts, exploited for spontaneous purchases, or entirely resold on the black market. Streaming media, email, and social media accounts are increasingly being resold. As a perverse added value, the malware can exploit the compromised account to recruit online acquaintances into installing and operating the knowledge thief, thereby creating a never-ending cycle of fresh targets for it to manipulate, perpetuating its nefarious activities ad infinitum?
Sensitive data isn’t just limited to usernames and passwords; both are compromised. Given the rapid growth of cryptocurrencies, wallets designed to secure and manage these digital assets could prove highly lucrative, alongside session tokens that facilitate seamless access to online accounts. The knowledge stealer may also capture a screenshot of the desktop at the point of execution, allowing its operator to distribute the image and send threatening email demands to other victims.
When encountering the term “session token,” you may wonder what it entails. Some websites and applications offer a “remember me” feature, allowing users to access the service without needing to re-authenticate or enter their login credentials anew. To maintain continuity and allow for subsequent interactions without requiring re-authentication, a session token is stored locally on your device.
A session cookie, essentially a specialized form of internet browser cookie, serves as a digital authentication token, verifying a user’s identity to grant access to a website or mobile application after efficient authentication has taken place. Cybercriminals seek out and exploit vulnerabilities that allow unauthorized access, circumventing traditional security measures by permitting illicit login attempts. As long as the service is accessed from a previously licensed machine, it appears to function normally.
The enterprise of knowledge stealing
Information-stealing malware is often marketed as a customized solution, allowing cybercriminals to tailor its behavior to specific goals. While operating on a target computer, the malware’s activities will vary depending on the buyer’s instructions, potentially targeting sensitive data such as login credentials, financial information, or confidential communications. Usually, individuals erase their digital footprints once they’ve obtained sensitive information, aiming to conceal any trace of their activities and protect their anonymity for as long as possible. When individuals experience an unprecedented invasion of their privacy, the sheer magnitude of the breach can leave them paralyzed, hesitating to take swift action, which inadvertently prolongs the criminals’ window to exploit or monetize the pilfered data.
Since info-stealing malware is often crimeware-as-a-service, it’s plausible that this malicious software was leveraged to introduce additional malware on the system with the aim of preserving access to it, in anticipation that criminals might return to the computer at a later time to exploit any newly acquired vulnerabilities and steal further sensitive information.
Restoration from an information-stealing assault
Prior to preserving the PC’s drives as evidence, the most logical initial step would be to securely erase the hard drive contents, followed by a clean installation of the operating system. Since the PC’s drives are assumed to be empty, wiping them clean of data and deleting any stored information poses no significant issue, as redundant backups exist elsewhere. If that’s not the case, consider preserving invaluable data stored on the PC by removing its drives, replacing them with blank ones, and performing a thorough setup of the operating system on the new drives. It will be crucial to acquire an external enclosure for the drive at a later stage to recover any unbacked-up data.
After reinstalling Windows, installing security software, and ensuring everything is up-to-date, you can proceed to update online accounts by using the PC to reset passwords and re-authenticate access across all previously used platforms.
To ensure optimal security, each password should be uniquely crafted and distinct from others, without being overly complex. One potential attack vector would be for a malicious actor to merely substitute commas for spaces, or vice versa, thereby bypassing even the most basic password security measures. If an attacker’s approach is misguided or speculative, they won’t be able to make informed guesses about potential corresponding passwords. Some ESET subscription tiers feature a built-in password manager, while others may integrate with your existing web browser’s password management capabilities. ESET additionally provides a .
Implementing multi-factor authentication across all accounts significantly enhances their security, making it exponentially more challenging for attackers to breach, even if they possess the login credentials.
When changing passwords, it is crucial that they be significantly different from any previously used passwords: if the new passwords are similar enough to the old ones, a criminal with access to the previous passwords will likely be able to make informed guesses about what the new passwords might be for various services. Be cautious not to use previous or similarly sounding passwords when cycling through options.
While discussing security measures previously, we emphasized the importance of updating not just passwords but also session tokens to maintain optimal protection. These licenses are compromised by information-stealing malware, allowing criminals to impersonate you by hijacking one of your previously authorized sessions. While some websites and applications offer the flexibility to track various energetic sessions or devices on which they were accessed, it is also crucial to be able to sign off or disconnect from these distinct active periods seamlessly. Try this as properly.
While sounding repetitive may be a concern, it’s crucial to emphasize the importance of this approach for every online service individually. Even those that may no longer be regularly employed. Strong passwords are essential for securing online presence, including websites, online stores, social media profiles, and email accounts, as these are prime targets for cybercriminals. When attackers discover reused passwords or common patterns among compromised credentials, they will likely engage in a mass attack campaign against multiple retailers, financial institutions, and service providers.
When recovering from an information-stealing attack that has compromised sensitive data, two often-overlooked yet crucial steps are: firstly, filing a comprehensive report with local law enforcement agencies to initiate an official investigation and potentially recover stolen assets; and secondly, promptly notifying all relevant financial institutions and credit monitoring services to alert them of the security breach and prevent fraudulent activities. Notifying law enforcement promptly that a crime has been committed may facilitate the recovery of compromised accounts. Having a police report on hand when dealing with financial institutions can significantly increase the likelihood of recovering stolen funds by providing concrete evidence of theft and supporting your claims. Although you may not reside in the United States, filing an Internet Crime Complaint with IC3 can facilitate law enforcement agencies worldwide in identifying and tracking data-thieving perpetrators.
Defensive methods
The recovery process from an information thief’s attack can be a grueling and distressing ordeal that may linger for days, weeks, or even months. While educating individuals on the essential steps to recover from such attacks, it’s crucial to acknowledge that information thieves are not the sole or most pervasive means by which one’s accounts can be compromised. The fundamental security mechanisms governing our online personas rely on a combination of usernames – often equivalent to email addresses – and passwords, with their use becoming increasingly pervasive.
Determining digital theft safeguards can significantly reduce the most severe consequences of such violations, much like maintaining insurance coverage or backing up data on a laptop – measures that are often overlooked until it’s too late.
Discovering whether your email address has been involved in an information breach is made easier by Have I Been Pwned (HIBP), a website that consistently updates details about data breaches worldwide and notifies you if your email address has been found in any of them. While this breach does not necessarily pose a direct threat to the security of your email account itself, it may suggest that the account is associated with the compromised service or platform from which the data was stolen. The Have I Been Pwned? (HIBP) service is available at no cost to individuals.
Data breaches can be difficult to avoid, as they often stem from vulnerabilities in systems and processes involving third-party providers. Cybercriminals often emerge from engaging in reckless online practices, exemplifying the unintended consequences of compromising digital security. To quickly recover from attacks of this nature, consider implementing the following strategies:
- Utilize distinct, complex passwords tailored to each individual website and application to safeguard against potential security breaches. With a password manager, you’ll experience immense relief from this complex process.
- Enable two-factor authentication as an optional security measure for all providers that support this feature. Hardware tokens or smartphone apps provide a more secure method of authentication compared to email or SMS notifications, as they offer an additional layer of protection against potential attackers who may gain access to your email or phone.
- Certain service providers grant users visibility into the devices connected to their accounts. Regularly assessing these tools, disable those that remain inactive or unresponsive over an extended period of time.
- Utilize a reputable information breach monitoring or identity theft protection service to receive alerts about potentially compromised accounts, ensuring timely notification and swift action to mitigate any potential damage.
- Never utilize pirated software programs, cracks, keygens, or other illicit tools, no matter how trustworthy they may seem to be, as it is illegal and can put your digital identity at risk. It’s astonishingly easy for fraudsters to convincingly portray these accounts as secure and trustworthy once they’ve compromised the login credentials.
- Keep your working system and functions current with the latest fully patched versions.
- Employ cutting-edge safety software solutions from reputable, well-established suppliers to ensure seamless integration and optimal performance.
- Stay informed about the latest safety trends, pointers, and insights from your favorite information safety sources.
By implementing these measures, you can significantly reduce your chances of becoming infected or help recover more quickly if you do contract the illness.
