| On July 19, 2024, a notable interruption affected certain Windows-based computers due to a straightforward issue linked to a CrowdStrike update. According to reviews, the root of the difficulty stemmed from a kernel-stage driver employed by CrowdStrike to integrate its software with Windows-based PCs and servers. CrowdStrike clarifies that the reported issue is not a security incident or cyberattack, and corrective measures have already been implemented to resolve the matter. Reports emerged that a recent update caused widespread Windows crashes, manifesting as the infamous Blue Screen of Death (BSOD), across various global computer systems. The outage has thus far impacted primary operations at major airlines, emergency responders, and various businesses among others. Learn more details about TechRepublic’s in-depth technology news article. |
As businesses increasingly adopt hybrid work models, securing and safeguarding company endpoints against emerging threats and malicious actors has become a pressing necessity. Whether companies own the devices or the data stored on them, adopting a proactive approach to securing endpoints is crucial for safeguarding against costly cyberattacks and data breaches.
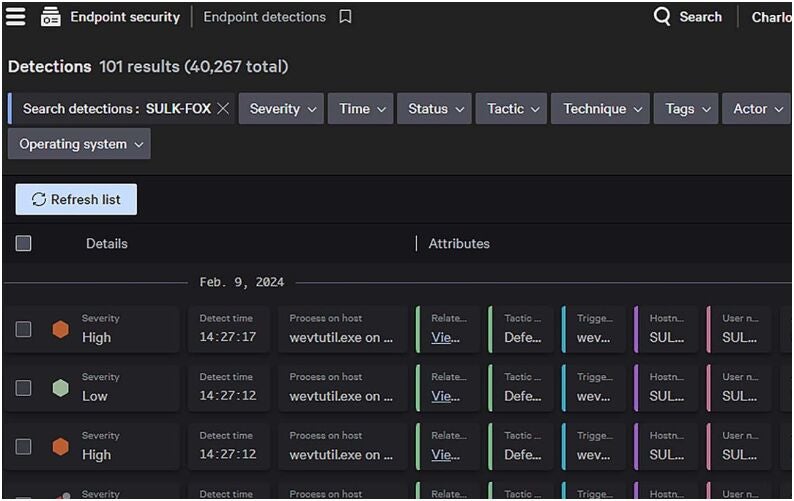
Today’s market offers a diverse array of solutions specifically designed for monitoring individual entities, detecting various threats, and providing robust remediation and response capabilities to effectively counteract these risks.
Here is the rewritten text:
In this article, we examine the top-performing endpoint detection and response software currently available on the market.
What’s the most effective endpoint detection and response (EDR) software solution for your organization? We’ve compiled a side-by-side comparison of the top EDR solutions to help you make an informed decision.
Endpoint Detection & Response (EDR) Solutions:
* **Carbon Black**: Leverages AI-powered threat hunting, real-time visibility, and automated incident response.
+ Pros: Scalable, user-friendly interface, comprehensive threat detection
+ Cons: Pricier than competitors, limited integration options
| Chief | 4.7 out of 5 | Free trial upon request | $184.99 per gadget per yr | ||
| Sturdy Performer | 4.8 out of 5 | Demo upon request | $79.99 per gadget per yr | ||
| Chief | 4.3 out of 5 Ease of deployment | Free trial obtainable | $54.75 per person, monthly (Microsoft 365 E5 subscription package) | ||
| Chief | 4.5 out of 5 Ease of deployment: The tool offers straightforward installation instructions and a user-friendly interface for effortless setup. | Demo upon request | Contact Pattern Micro for pricing | ||
| Chief | 4.6 out of 5 | Free trial upon request | $199.49 per year for a 10-unit subscription. |
CrowdStrike Falcon Perception XDR: The Ultimate Total Endpoint Detection and Response Solution for Businesses

Here is the rewritten text:
As a trusted authority in the Endpoint Detection and Response (EDR) space, I highly recommend CrowdStrike’s Falcon Insight platform as a top choice for many organizations. The solution offers cutting-edge AI-driven threat detection, a streamlined and centralized agent, and the capability to automate complex business processes, resulting in enhanced efficiency and security.
In 2023, CrowdStrike earned the prestigious title of Leader in the Gartner Magic Quadrant for Endpoint Protection Platforms and secured the top position in both the Gartner Magic Quadrant and the Forrester Wave reports, among 15 notable competitors. CrowdStrike’s EDR solution stands out as the industry leader in terms of product evolution, technological advancements, and customer following?
Customers have praised the CrowdStrike platform for its gentle asset management and extremely low false positive rates.
Why I picked CrowdStrike Falcon
I chose CrowdStrike Falcon as the greatest overall solution due to its industry-leading features and performance, further bolstered by its overwhelmingly positive customer reviews. While CrowdStrike excels in unbiased evaluations, it also garners widespread acclaim from its user base and is commonly regarded as the go-to endpoint detection and response (EDR) software provider today.
While numerous software solutions boast extensive feature sets, I firmly believe that the ultimate test lies in the number of satisfied clients who enthusiastically recommend the product to other businesses. Despite a higher price point, CrowdStrike excels in this area.
Pricing
CrowdStrike’s Falcon Endpoint Detection and Response (EDR) capability is accessible via subscription to Falcon Enterprise or Falcon Elite plans.
Below is a swift summary of pricing and options for each:
- $199.95 per device; boasts cutting-edge features such as Enhanced Data Recovery (EDR), Extreme Data Response (XDR) technology, and top-tier next-generation antivirus capabilities.
- Obtain pricing information from our gross sales team; this solution encompasses advanced features such as Enhanced Data Response (EDR), Extended Detection and Response (XDR), and robust IT hygiene and identity-based security capabilities.
Options
- AI-powered detection system.
- Risk Intelligence: A Comprehensive Framework for Understanding and Mitigating Threats from Over 230 Adversaries
- Actual-time response to threats.
Professionals
- Very dependable detection.
- Light-weight; not resource-intensive.
- Intuitive person interface.
Cons
Is SentinelOne’s Singularity Endpoint the ultimate solution for small businesses?

For small businesses, I recommend implementing SentinelOne’s Singularity Endpoint solution to safeguard their digital assets and data from potential cyber threats. While SentinelOne may not match the strength of CrowdStrike, its relatively affordable pricing structure still delivers top-notch detection and response capabilities. The solution features advanced threat detection, proactive response capabilities, and streamlined remediation processes, thereby simplifying the task of keeping infrastructure and endpoint assets secure for IT and security teams.
I’m particularly fond of SentinelOne’s Storyline feature, which seamlessly correlates and contextualises all software events in real-time, delivering a comprehensive understanding of emerging threats.
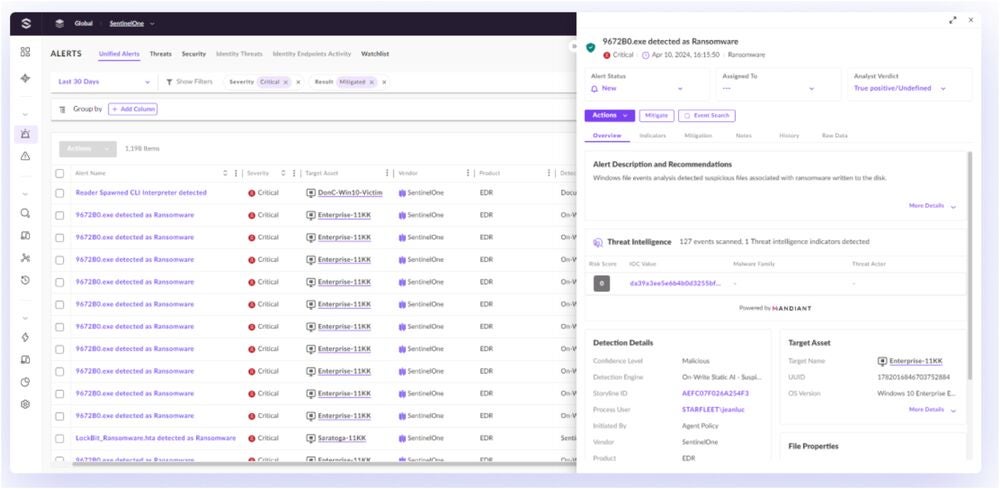
Why I picked SentinelOne Singularity
SentinelOne stands out on this list as a trusted alternative to CrowdStrike, especially for smaller businesses without the deep pockets to invest in robust cybersecurity solutions like EDR.
Similar to CrowdStrike, SentinelOne Singularity Endpoint also earns praise from the group. Notably, clients praised SentinelOne Singularity’s user-friendly console and affordable overall cost.
Pricing
SentinelOne offers its Endpoint Detection and Response (EDR) solution across four subscription tiers, each designed to meet the unique needs and size requirements of various enterprises, with distinct feature sets included.
A concise breakdown of each tier is provided below, featuring its respective pricing and offering various options.
- Offering $79.99 per endpoint, this package includes Enhanced Detection and Response (EDR), role-based entry management for streamlined access control, and multi-tenant administration for effortless deployment and monitoring across various environments.
- $159.99 per endpoint; includes comprehensive management options, extended detection and response capabilities, and a 14-day knowledge retention feature.
- What’s included is a comprehensive suite of features for $209.99 per endpoint: full capabilities combined with a 30-day knowledge retention period, threat hunting functionality, and real-time risk detection and response capabilities.
- Offer customized pricing packages, encompassing industrial-grade solutions, community management, vulnerability assessment and remediation, digital forensics, professional coaching, and guided deployment services.
Options
- A comprehensive contextual framework that seamlessly integrates with various operating systems and circumstances to create a harmonious narrative.
- Automated risk decision.
- Historically, EDR has demonstrated an impressive capacity for retaining knowledge for up to three years.
Professionals
- Reasonably priced beginning plan.
- Automated responses.
- Customizable automations.
Cons
- Can we enhance buyer assistance capabilities?
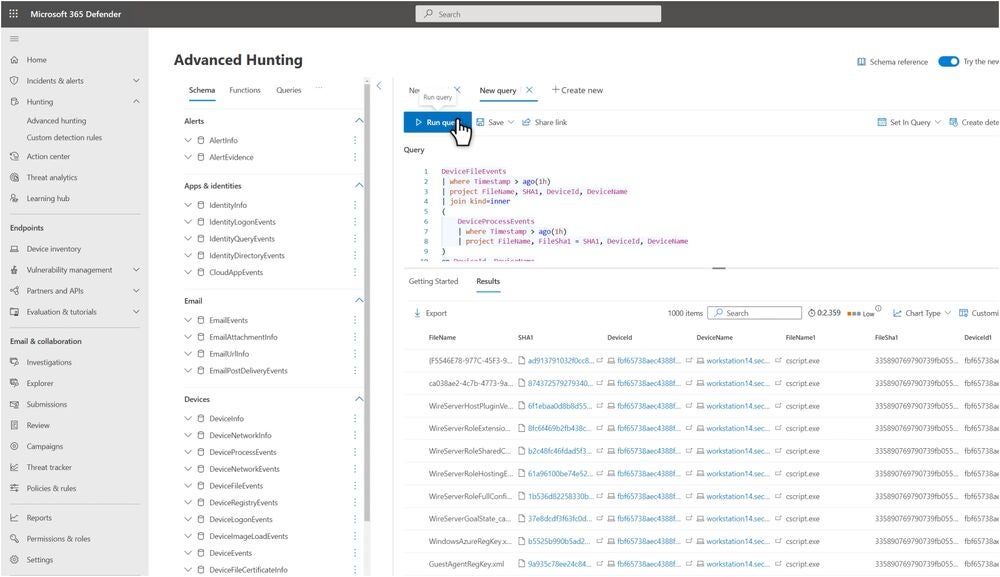
Microsoft Defender for Endpoint: The Optimal Choice for Microsoft-Centric Enterprises

For businesses thoroughly entrenched within the Microsoft universe, the introduction of Microsoft Defender for Endpoint proves an intuitive choice. Utilizing AI-powered strategies, this solution effectively halts cyber and ransomware attacks, while leveraging automated investigation and remediation features and granting access to a global threat intelligence database for enhanced protection.
MDE has garnered widespread acclaim from independent testing firms and earned the distinction of being named a leader.
Microsoft’s commitment to robust security measures resonated with my organization’s needs; therefore, I selected Microsoft Defender for Endpoint. Its comprehensive suite of features effectively protected our devices and networks from emerging threats, thereby minimizing potential vulnerabilities.
I chose Microsoft Defender for Endpoint because of its robust integration with various Microsoft 365 products, as well as its inclusive presence within. By streamlining integration, this simplifies the process for Microsoft-licensed organizations to seamlessly combine EDR resolutions with their existing safety protocols, leveraging their existing investments in Microsoft software solutions.
Pricing
Microsoft Defender for Endpoint offers two tiers of protection: Essential and Advanced. MDE P1 features advanced antimalware and endpoint firewall capabilities for the next generation of protection. In the interim, MDE P2 features automated investigations and remediation capabilities, among other enhancements.
Companies requiring Microsoft’s comprehensive endpoint detection and response capabilities typically benefit from utilizing .Proper. Currently, Microsoft Defender Experts for Enterprise (MDE) P2 is integrated within the Microsoft 365 E5 enterprise software suite.
- Offering a comprehensive solution at $54.75 per person monthly, this package includes MDE EDR, Microsoft Workplace software, advanced analytics, and enhanced security features for seamless scalability.
Options
- Simplified endpoint administration dashboard.
- Copilot for Safety.
- International risk intelligence and analytics.
Professionals
- Bundled with Microsoft 365 E5.
- Seamlessly integrates with various Microsoft security tools, including Intune and Defender for Endpoint.
- Affordably priced, considering the added value of bundled software.
Cons
- May be resource-intensive.
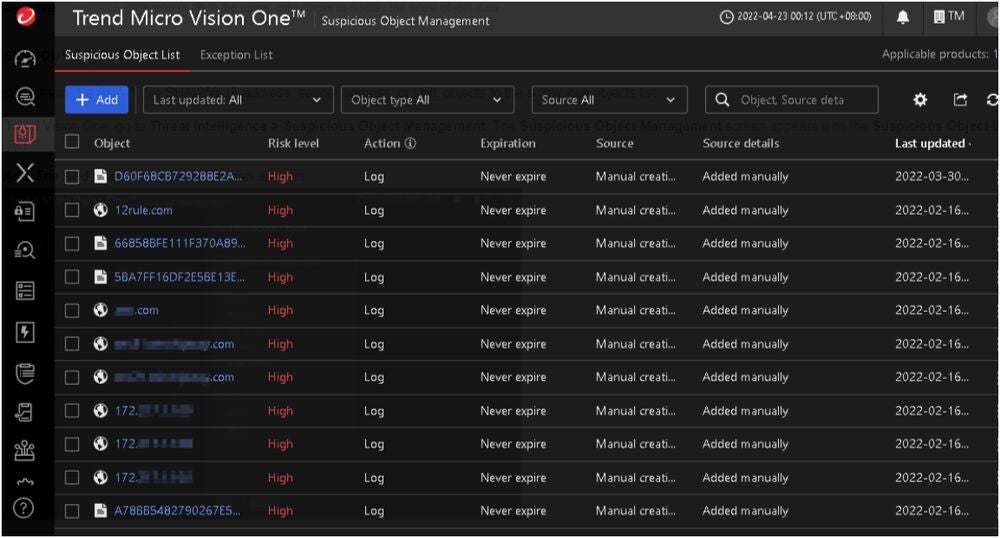
Pattern Micro Innovative AI: Optimal Solution for Comprehensive Security Protection

As a long-established player in the regional security landscape, Pattern Micro remains an excellent option for businesses seeking comprehensive protection from a single provider. One innovative solution provides unified tools to safeguard endpoints, emails, and networks from a single, comprehensive platform. The platform provides advanced, extended detection and response capabilities, or XDR sensors, along with sophisticated contextualization tools to empower analysts. Based on zero-trust networking principles.
Recently, Imaginative and Prescient One earned an impressive distinction when Forrester recognized it as a leader in the endpoint security industry, specifically naming it a Chief.
During the evaluation, Pattern Micro’s emphasis on “constant endpoint safety” and its “granular utility management platform” stood out as notable features.
• Antique music box with delicate ballerina figurine
• Small, intricately carved wooden box with strange symbols
• Vintage photograph of a young woman in a hat and coat
• Old leather-bound book with yellowed pages and no discernible title Picture: Pattern Micro
I chose Pattern Micro Imaginative and Prescient One because.
While Pattern Micro’s Imaginative and prescient One is not exclusively an Extended Detection and Response (EDR) solution, it does offer significant value as an eXtended Detection and Response (XDR) product that can provide comprehensive security across multiple layers of an organization’s infrastructure.
The all-encompassing Zero Trust framework safeguards not just endpoint data, but also various aspects of a technology ecosystem, including the cloud, email services, and other related features.
With the rollout of Pattern Micro on this listing, the company is now concentrating its efforts on delivering comprehensive protection to organizations, transitioning seamlessly from endpoint-focused EDR to a more extensive scope with XDR capabilities.
Pricing
To obtain a clear and accurate quote, I strongly advise that you reach out directly to Pattern Micro via their authorized channels for a detailed assessment of the costs involved. The website features a user-friendly Contact webpage that provides additional information, accompanied by complimentary trials and video demonstrations of the innovative Imaginative and prescient One solution.
You may also navigate a gathering with Pattern Micro through its website, enabling you to learn more about each pricing plan and the functionality set offered by Imaginative and prescient One.
Options
- AI-powered XDR system.
- Unified Platform for Detection, Investigation, and Response.
- Customized playbooks and case administration.
Professionals
- Huge visibility throughout varied layers.
- Versatile deployment choices.
- Streamlines multiple safety devices onto a unified and accessible platform.
Cons
- The technical assistance crew’s performance is inconsistent.
Bitdefender’s GravityZone: A Force to Be Reckoned with in Primary Endpoint Security

If your sole focus is ensuring the primary endpoint’s safety, consider incorporating Bitdefender GravityZone as a reliable solution. This selection prioritizes defence against prevalent threats such as fileless attacks, ransomware, and phishing attempts. This innovative solution provides a unified console for streamlined endpoint security management, bolstered by advanced anti-exploit features and cutting-edge anti-malware protection.
According to unbiased reviews, Bitdefender has been consistently praised for its “near- relentless focus” on thwarting threats, as confirmed by impartial evaluations, including those conducted in This fall 2023, which highlighted the software’s impressive ability to detect and prevent malicious activities through its advanced prevention engine?
Here is the rewritten text:
The exterior of GravityZone’s endpoint safety is notable, but what truly stands out is its flexible licensing and subscription model, allowing organizations to tailor their plan to suit their specific needs.
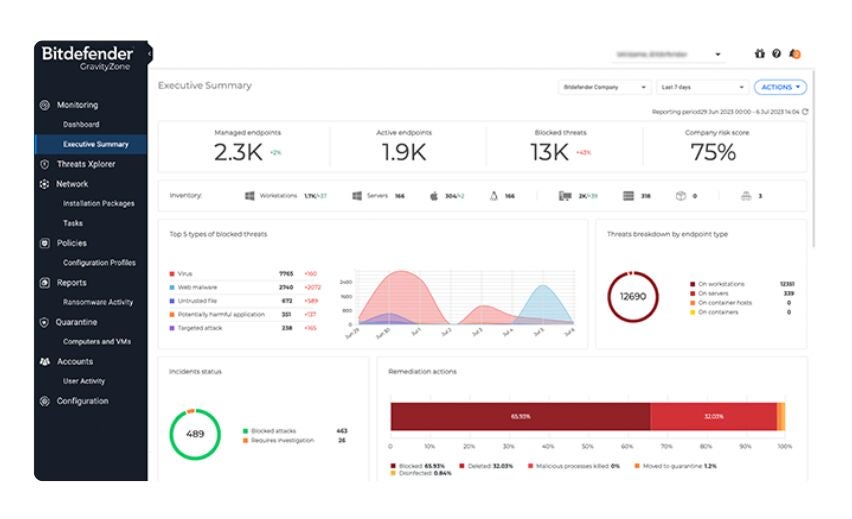
Why I picked Bitdefender GravityZone
I chose Bitdefender GravityZone for its comprehensive risk prevention capabilities and highly tailored subscription options. The flexibility to customize the number and type of units or endpoints in your GravityZone subscription is remarkably intuitive, particularly beneficial for organizations seeking to optimize their security expenditures by selecting only the necessary features.
Pricing
Bitdefender’s GravityZone offers tailored subscription options, adapting to diverse unit requirements and contract sizes.
GravityZone’s small enterprise offering is comprised of three distinct options: GravityZone Small Enterprise Security, GravityZone Enterprise Security, and GravityZone Enterprise Security Premium, catering to the diverse needs of smaller businesses.
Here are the details on each tier’s pricing:
- Offered at a competitive rate of $199.49, this package provides security assurance for 10 units over the course of one year, featuring comprehensive safety protocols that safeguard against ransomware, web-based attacks, and other endpoint threats.
- Priced at $258.99 for a 10-unit, one-year subscription, this package includes all features from the Small Enterprise option, along with internet entry management, device management, and endpoint threat analytics capabilities.
- Available for $570.49 per year for a 10-unit license, this solution comes equipped with comprehensive Enterprise Security features, including customizable machine learning capabilities, advanced sandbox analysis, and robust fileless attack protection.
Options
- Ransomware mitigation.
- Protection towards fileless assaults.
- Purchasable safety add-ons.
Professionals
- A range of subscription options catering to diverse enterprise needs.
- Easy person interface and deployment.
- Low influence on machines.
Cons
- Detailed reporting could potentially reach unprecedented levels of granularity.
The key options of EDR software programs include: enabling real-time threat detection; providing instant incident response; allowing for the collection and analysis of endpoint data; supporting automated containment and remediation; offering advanced analytics and visualizations to identify trends and patterns; facilitating collaboration with security teams through customizable dashboards and reports.
Endpoint detection and response options can vary significantly depending on the features they offer. Several models are integrated within existing software program ecosystems, such as MDE with Microsoft. Companies catering to smaller organizations offer reduced starting costs, such as SentinelOne, while others provide self-contained products offering comprehensive Endpoint Detection and Response (EDR) capabilities.
Regardless of the endpoint detection and response (EDR) provider, certain essential features can be expected from most, if not all, EDR solutions. Here are all key Enterprise Data Repository (EDR) functions and the benefits they bring to organizations:
Endpoint knowledge assortment
Enterprise Digital Records (EDRs) are specifically designed to aggregate and consolidate critical safety information across all connected endpoints within a community. Data transmission encompasses various aspects such as accessing, processing, and linking disparate pieces of information.
Endpoint knowledge consolidation furnishes Extended Detection and Response (EDRs) with a comprehensive vantage point on an organization’s IT infrastructure, thereby offering situational awareness into potential weaknesses or hazards within the system.
Risk detection and response
Enhanced detection and response options scrutinize every unusual activity within a community, examining anomalous events, concealed weaknesses, or suspicious items that warrant further investigation. One significant difference between Endpoint Detection and Response (EDRs) and traditional antivirus solutions is that EDRs have the capability to scrutinize system patterns and behavior, proactively identifying potential threats.
Enhanced Detection Responses leverage advanced algorithms and machine learning technologies to proactively identify anomalies and uncover known and unknown threats by analyzing patterns and behaviors.
In addition to their advanced analytics capabilities, Enterprise Data Repositories (EDRs) are also distinguished by their automation features. As soon as an Enhanced Detection Response (EDR) identifies a threat, it enables the option to trigger an automatic response, which can initiate a relevant action. One potential solution could be as straightforward as issuing a warning or taking concrete steps to mitigate the danger entirely?
Risk looking and forensic analytics
EDRs can significantly enhance organisations’ ability to detect and respond to security incidents by providing real-time visibility into potential threats, enabling a proactive approach to incident response and defence. Enhanced Detection Responses are engineered to overcome prior vulnerabilities, identify recurring patterns, and proactively hunt down potential threats or nefarious actors before they strike.
This technology incorporates advanced forensic analytics, enabling security teams to precisely track the emergence of potential threats, thereby facilitating informed decision-making and subsequent strategic adjustments.
Reporting and prioritization capabilities
EDRs often incorporate comprehensive reporting and robust prioritization capabilities. With enhanced digital reporting (EDR) capabilities, IT analysts can efficiently produce comprehensive reviews and actionable summaries detailing a company’s current state and operational safety efficacy. These tools can be leveraged to streamline compliance and regulatory reporting, thereby reducing the tedious effort required to compile comprehensive safety data sets.
EDR software also features advanced alert prioritization, allowing only the most critical notifications to be swiftly presented to analysts and security professionals. By streamlining the management of a vast amount of data, this solution mitigates the problem of information overload, thereby reducing fatigue among IT teams and decision-makers while keeping them focused on more urgent matters that require their attention.
To determine the ideal Electronic Data Room (EDR) for your team, consider the specific needs and goals of your organization.
Among numerous esteemed EDR providers offering a diverse range of resolutions, pinpointing the ideal EDR solution that aligns with your specific needs can prove daunting. Despite these uncertainties, consider the following factors to help select the most suitable solution for your team.
Considering firm dimension and variety of endpoints?
To initiate the process, consider the scale of your organization and the sheer volume of endpoints that require coverage by an Endpoint Detection and Response (EDR) solution?
By having a rough estimate of endpoint numbers, you can significantly reduce the amount of time required for resolution, especially considering that various options and Endpoint Detection and Response (EDR) subscriptions are better suited to specific enterprise sizes rather than being one-size-fits-all solutions.
Assess the effectiveness of your current safety systems and equipment.
It’s also crucial to consider what types of safety equipment and infrastructure your team currently possesses. When assessing the need for a fleet management solution, consider whether you solely require an Event Data Recorder (EDR) resolution or if your organization necessitates alternative safety software options as well.
This integration may also enhance your purchasing decision since many EDR providers offer various safety features simultaneously. Purchasing a bundle of safety merchandise may result in more attractive online pricing and licensing opportunities.
Evaluate the integrity of safety records and independently verify the consequences.
A key consideration when selecting an EDR supplier is the company’s safety reputation and efficiency in impartially validated testing? While some EDR providers boast about being the “best”, seeking out impartial assessments from reputable third-party organizations offers a more objective perspective on an EDR’s performance.
Moreover, conducting a thorough analysis of an EDR vendor’s safety reputation won’t cause harm. Were there any significant security incidents, such as data breaches or major vulnerabilities that compromised sensitive information or posed a risk to the organization’s assets? Do their clients wholeheartedly believe in their expertise, integrity, and commitment to delivering exceptional outcomes?
When evaluating a service or product, I firmly believe that examining genuine customer feedback is one of the most effective ways to form an informed opinion. What are the actual efficiencies achieved by these EDR solutions in practical applications?
Maximize free trials and demos
You should also take advantage of any complimentary trials or product demonstrations offered by EDR providers to reap additional benefits. Before investing in a solution, it’s essential to ensure that the products align with your team’s needs, considering both the time and financial commitments involved in procurement and deployment.
Free trials and product demonstrations can offer you a comprehensive grasp of whether an endpoint detection and response solution aligns with your team’s needs and requirements.
Despite this, it’s crucial to note that most advanced EDR solutions necessitate some level of collaboration with the vendor’s sales team, thus a moderate amount of preparation time should be factored in.
Discover integrations with third-party merchandise
Prior to finalizing your EDR integration, it’s crucial to assess its compatibility with existing third-party products within your organization’s portfolio. You’re hesitant to invest in a solution that won’t seamlessly integrate with other tools in your workflow, ultimately concluding that it’s not a suitable fit for your needs despite its potential benefits.
Fortunately, online resources offer a diverse range of integration assets and documentation, providing information on which third-party software programs integrate with specific EDR solutions.
Methodology
Here is the rewritten text:
A comprehensive assessment of endpoint detection and response options for businesses in 2024 focused on scrutinizing each EDR solution’s security capabilities, pricing models, and overall value proposition for budget-conscious organizations.
An exhaustive analysis was conducted through a comprehensive review of official product documentation, unbiased test results, and a thorough examination of each product’s efficiency and value proposition. By incorporating genuine user feedback from reputable review platforms, I developed a comprehensive understanding of each EDR solution’s performance in real-world scenarios.
Ultimately, companies specializing in cybersecurity, managed security service providers (MSSPs), and threat intelligence firms likely stand to gain the most from each EDR resolution. My aim is to enable businesses to quickly identify the End-to-End Detection and Response (EDR) provider best suited to their current needs and requirements.

